Getting Started¶
Get Started in 5 Minutes¶
Note
For a more detailed guide, see Setup - AWS & AWS GovCloud, Setup - Azure & Azure Government, Setup- Google Cloud or Setup- Repository.
Want to jump right into using Fugue? Follow the steps below to have an environment up and running in 5 minutes.
Sign up for Fugue¶
Register for a free account here. You’ll start with a 30-day free trial, after which you can purchase a paid plan or be transitioned to the free-forever Developer plan.
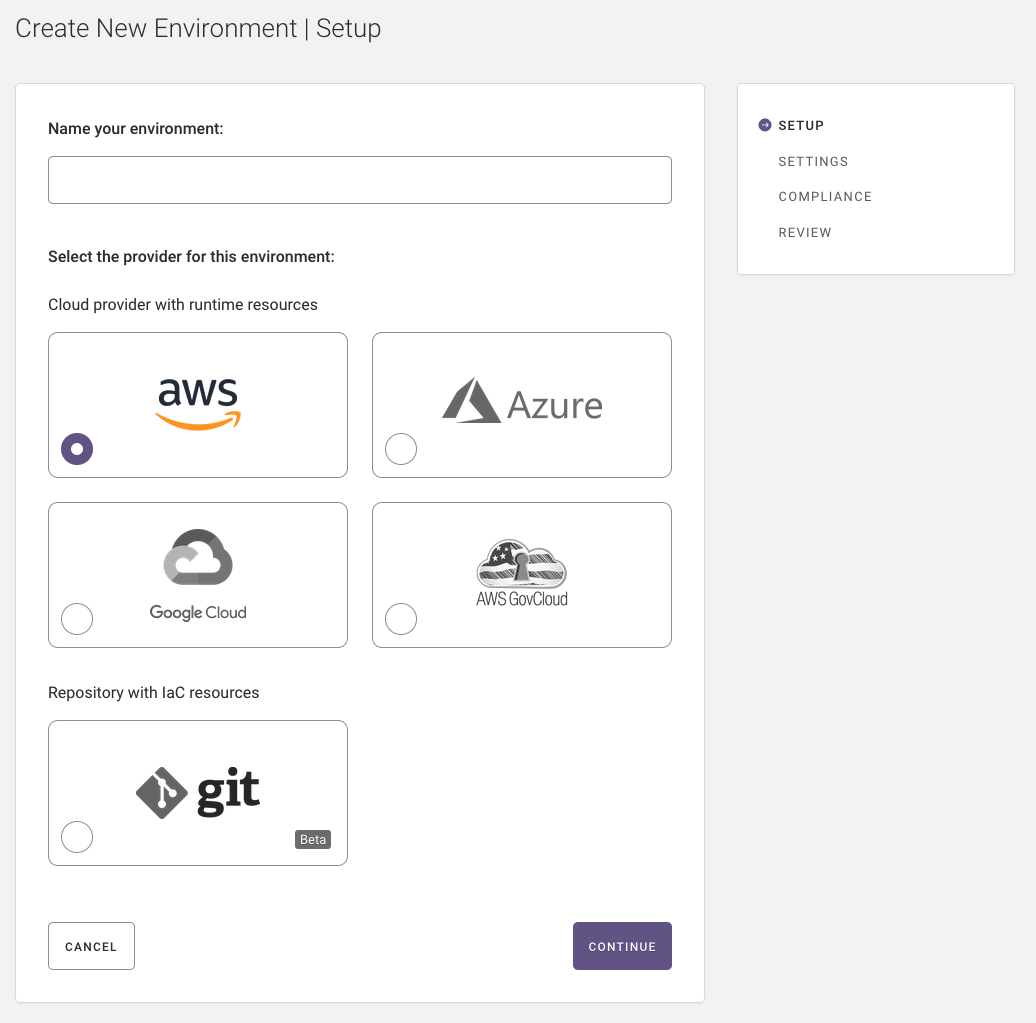
Step 1: Environment Setup¶
Enter your environment’s name and select the provider (AWS, Azure, Google, Repository):
Step 2: Environment Settings¶
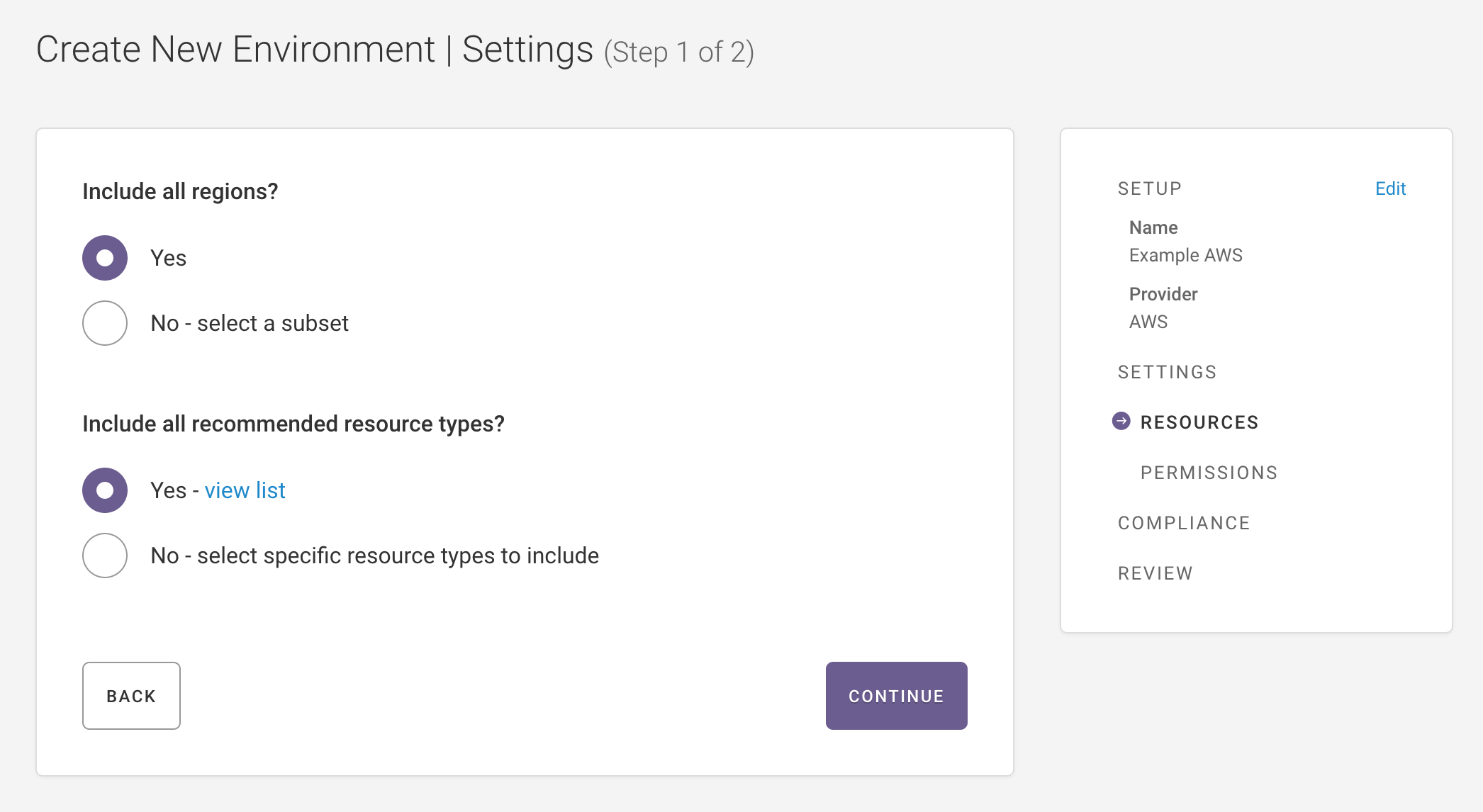
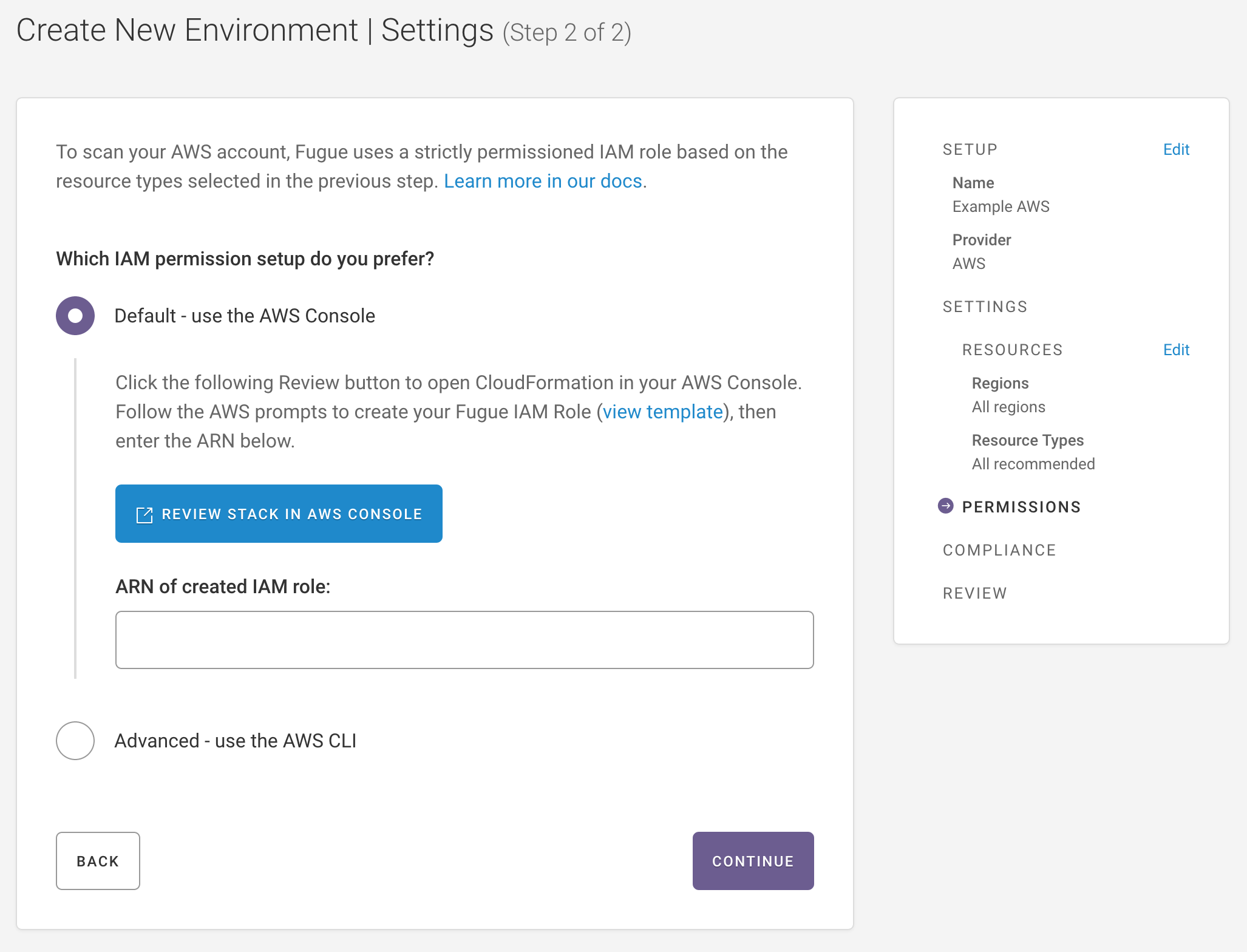
AWS and AWS GovCloud¶
Select the region(s) and resource types to scan, then create an IAM role and enter the role ARN:
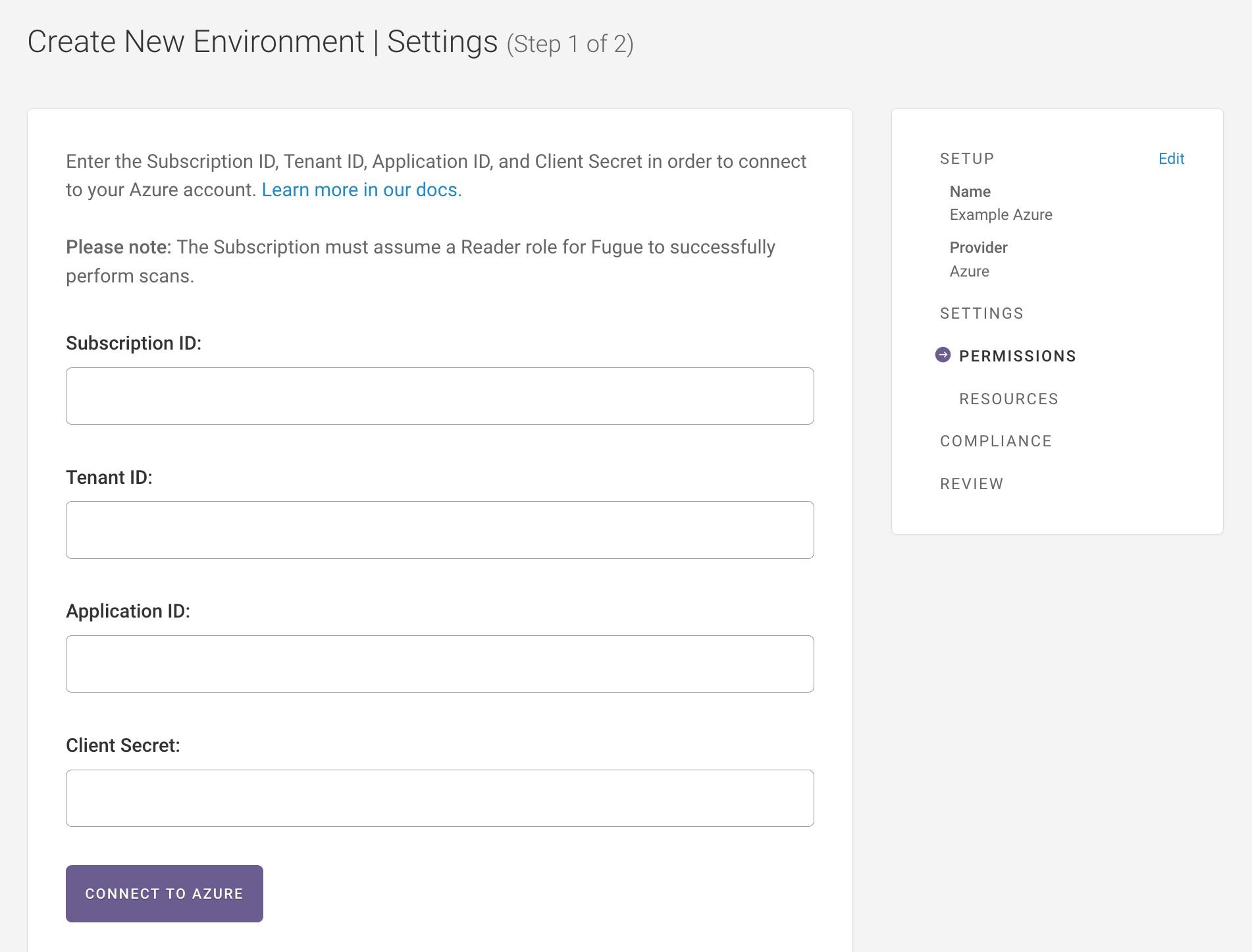
Azure and Azure Government¶
Create an Azure Active Directory application and service principal.
Assign the service principal a
ReaderRBAC role.If you want access to Active Directory resources then additionally assign the required AD role. We recommend only activating Active Directory support for the credentials associated with a single Fugue environment. Your Active Directory resources will show up in this environment and if you add Active Directory permissions in other environments, the resources will be duplicated.
Generate a client secret.
Enter tenant ID, subscription ID, application (client) ID, and client secret into the environment creation page.
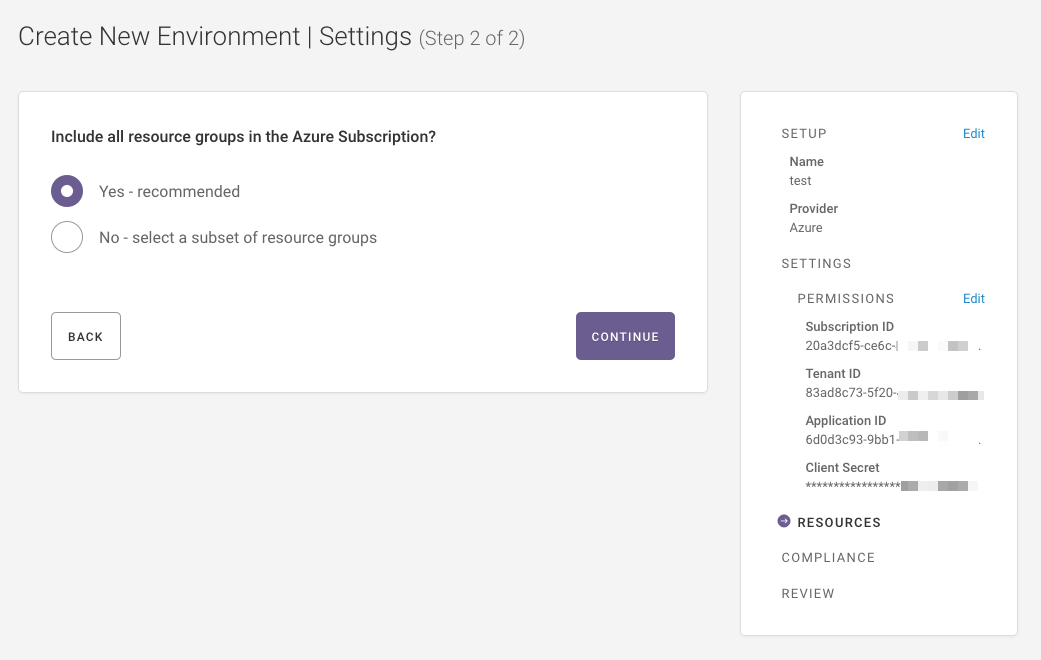
5. Select resource groups to scan.
Google¶
Create a Service Account and enter the returned email address back in the Fugue environment setup.
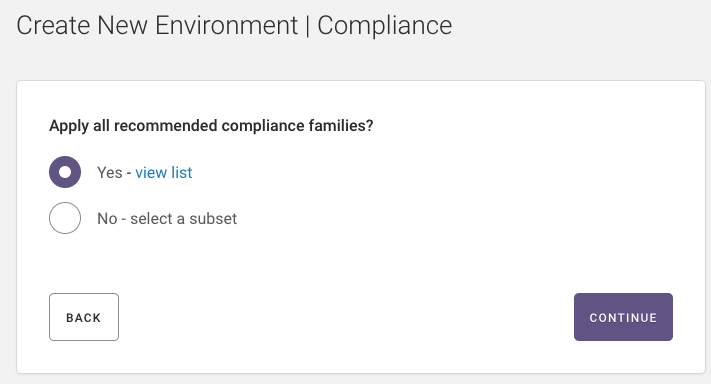
Step 3: Select Compliance Families¶
Select the compliance families you want Fugue to use to assess your infrastructure (AWS, Azure, or Google):
Note
Select Yes to use the list recommended compliance families, which includes Fugue out-of-the-box compliance families, as well as custom families.
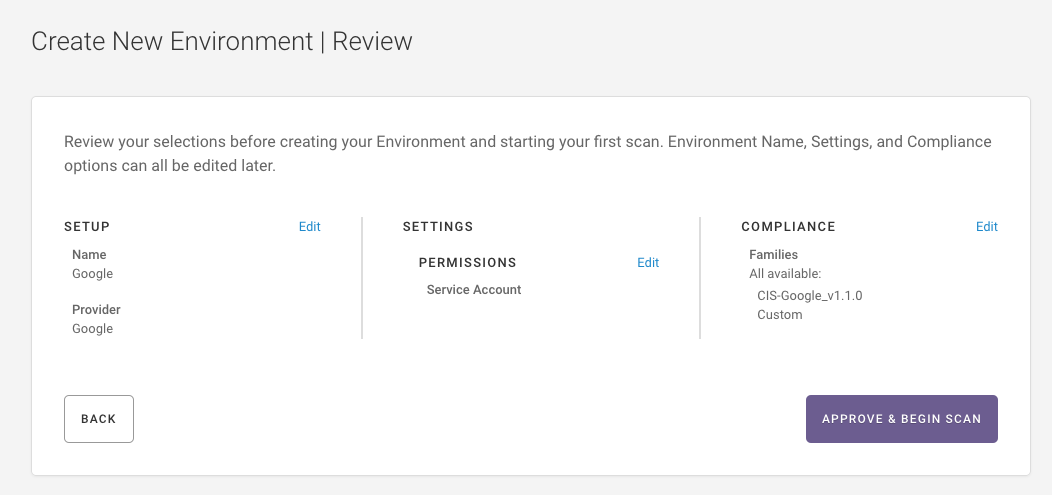
Step 4: Review¶
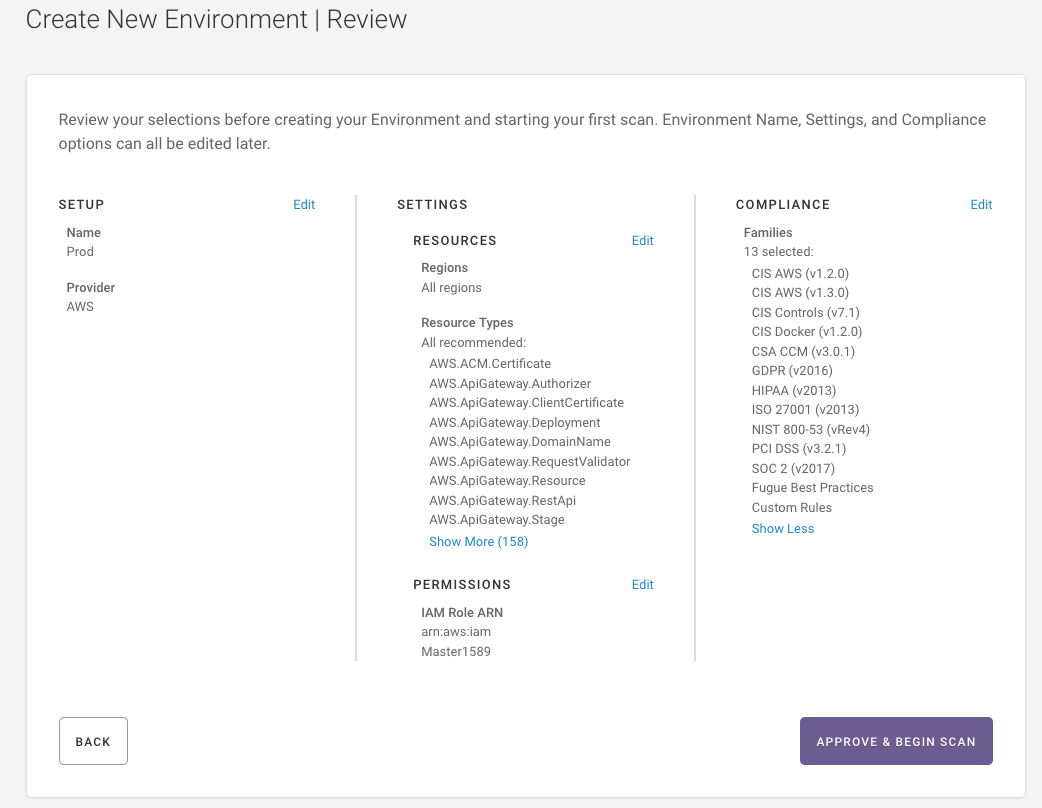
AWS and AWS GovCloud¶
Environment name
Region(s)
AWS IAM role ARN
Compliance standards
Resource types to scan
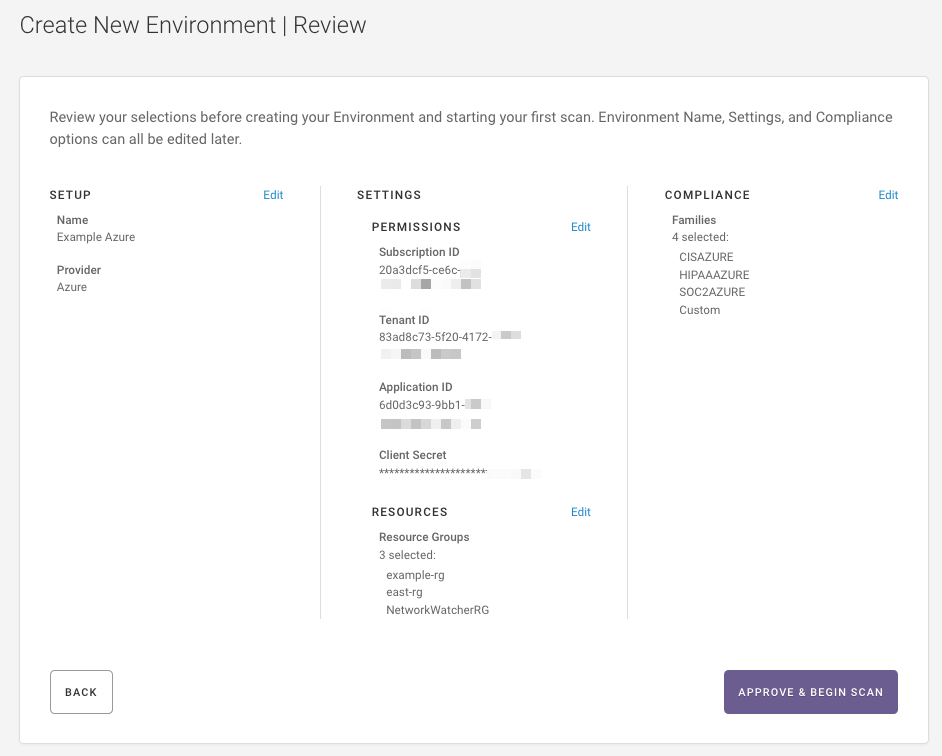
Azure and Azure Government¶
Environment name
Credentials
Tenant ID
Subscription ID
Application (client) ID
Client secret
Compliance standards
Resource groups to scan
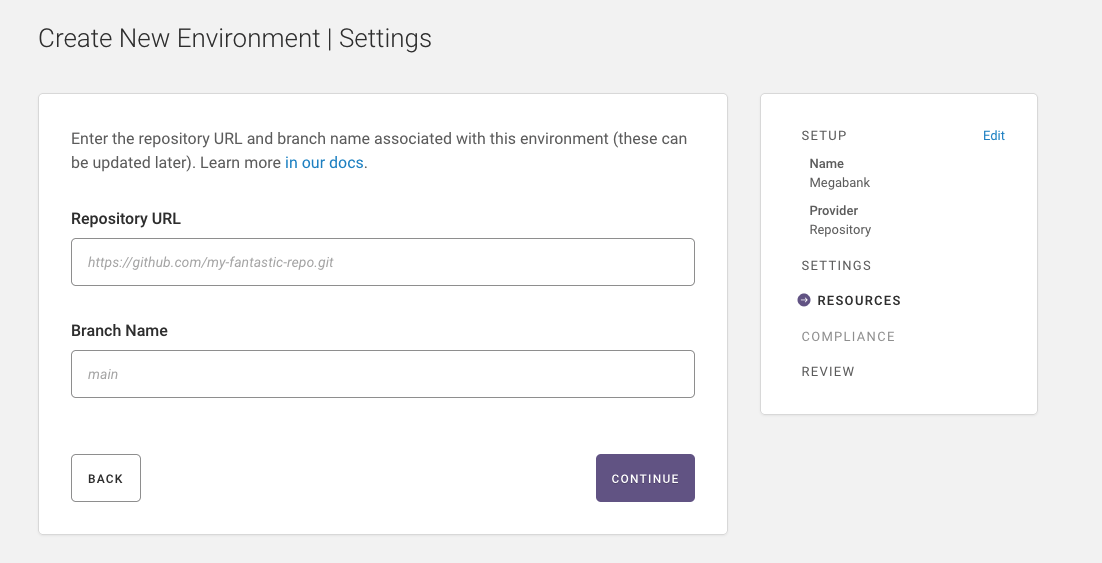
Repository¶
Environment name
Provider
URL
Branch name
Compliance families
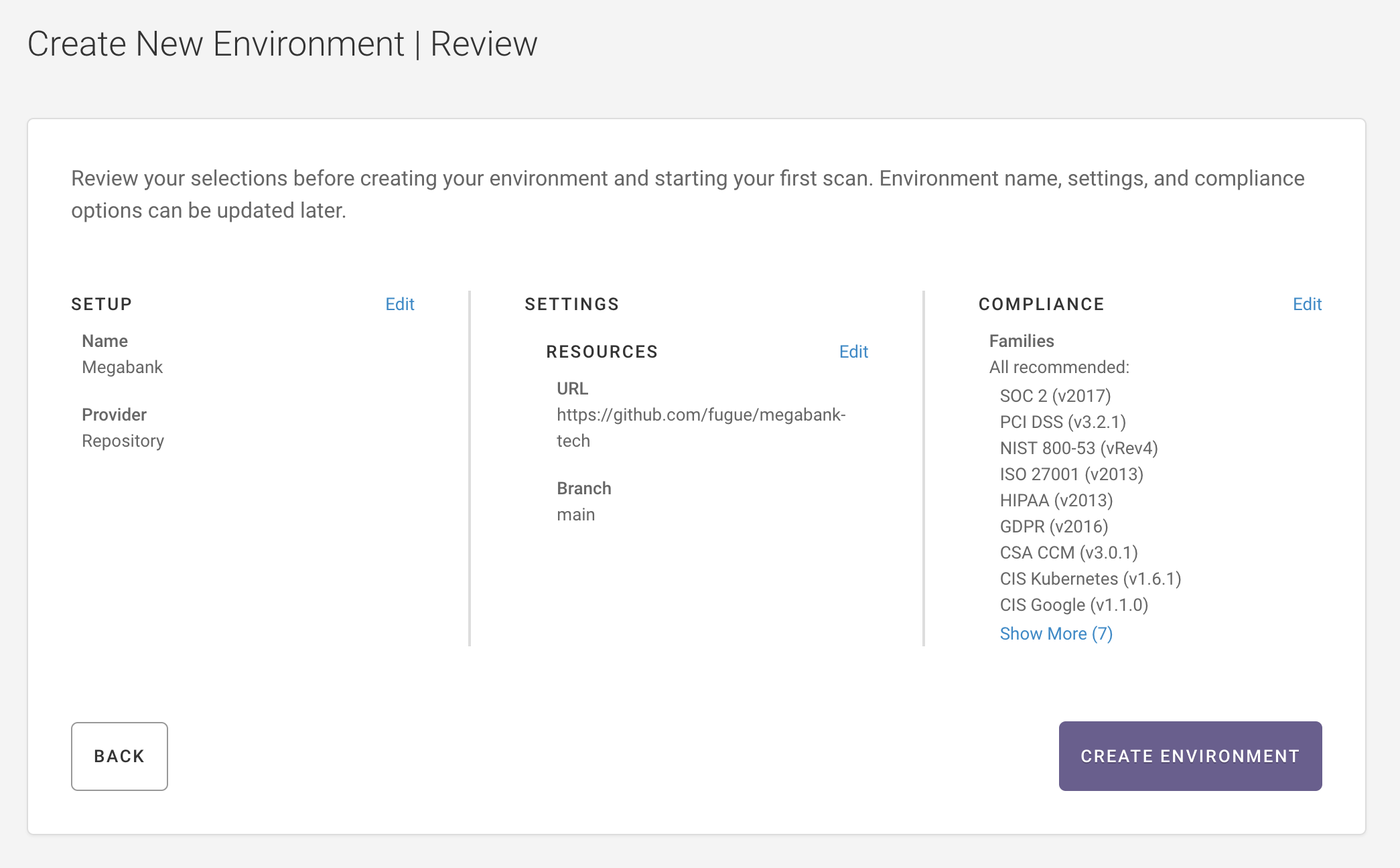
Kick off a scan to view resource details about your repository. See Setup- Repository.
Further Reading¶
Setup - AWS & AWS GovCloud, Setup - Azure & Azure Government, Setup- Google, and Setup- Repository – More detailed information about setting up Fugue
Example: Scan, Detect Drift, Enforce – How to enable drift detection and enforcement