Release Notes¶
Fugue ensures that cloud infrastructure stays in continuous compliance with enterprise security policies.
2022.06.29¶
Fugue API Update¶
The Fugue API requires an accurate Content-Type header on POST and PATCH requests. Requests without a Content-Type header or with a Content-Type header that does not match the type required by the endpoint are rejected and the following error message is returned: {"type":"InvalidParameterValue","message":"body :: value is not a valid dict","code":400}. Please reach out to support@fugue.co if you have any questions.
2022.06.08¶
Fugue Terraform Provider Updates¶
Version 0.0.11 of the Fugue Terraform Provider was published to the Terraform Registry, and now supports enabling or disabling custom rules. Refer to the documentation for more information.
2022.05.25¶
Visualizer: Expanded AWS Service Coverage¶
Expanded AWS service coverage to include:
aws_s3_bucket_server_side_encryption_configuration (SSE CONFIG) [Displays as a Pod] (Note this resource type is only supported for Repository environments)
2022.05.19¶
Extended AWS Service Coverage (limited beta)¶
Fugue now supports the AWS.Organizations.Account resource type, which enumerates member accounts in an AWS Organization.
Please ensure that you add the AWS Organization root account as a Fugue environment to see results for organizational units (OU) or AWS accounts that belong to the AWS Organization. Please refer to AWS docs here for additional information.
If you are interested in gaining access to this beta resource, please email support@fugue.co.
2022.04.19¶
Fugue CLI Enhancements¶
Fugue adds support for creating and updating waivers with an expiration date via the CLI.
2022.03.30¶
Fugue now supports labels for Google Cloud resources. You can:
View labels associated with Google Cloud resources on the Compliance pages
Create waivers based on labels
View labels in reports
2022.03.17¶
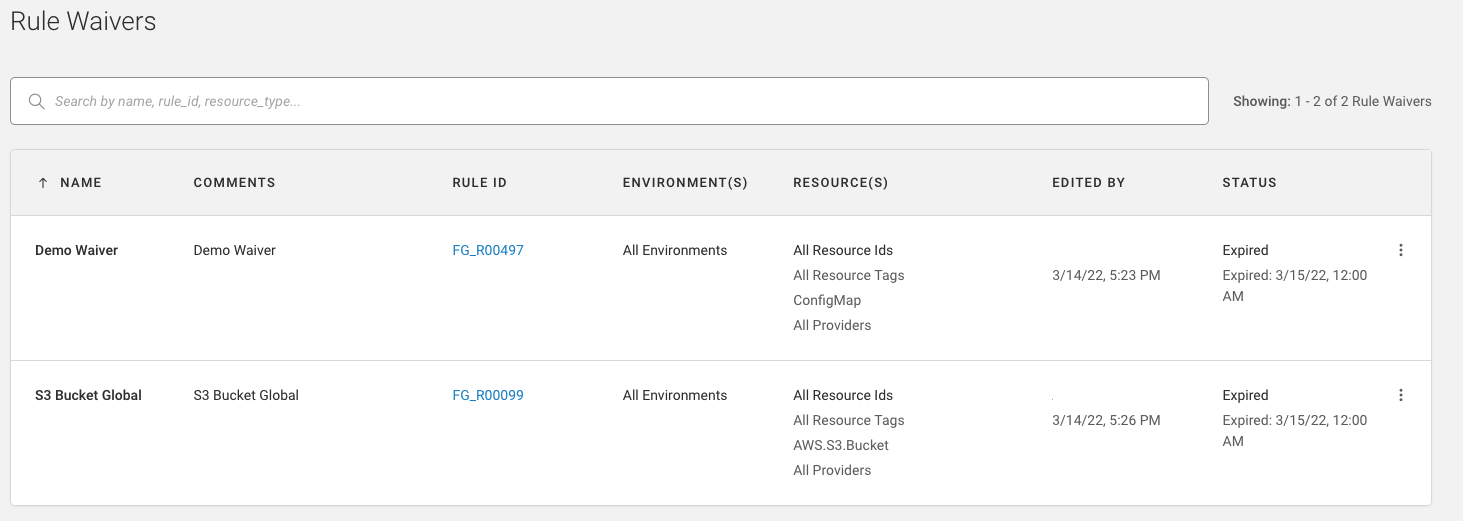
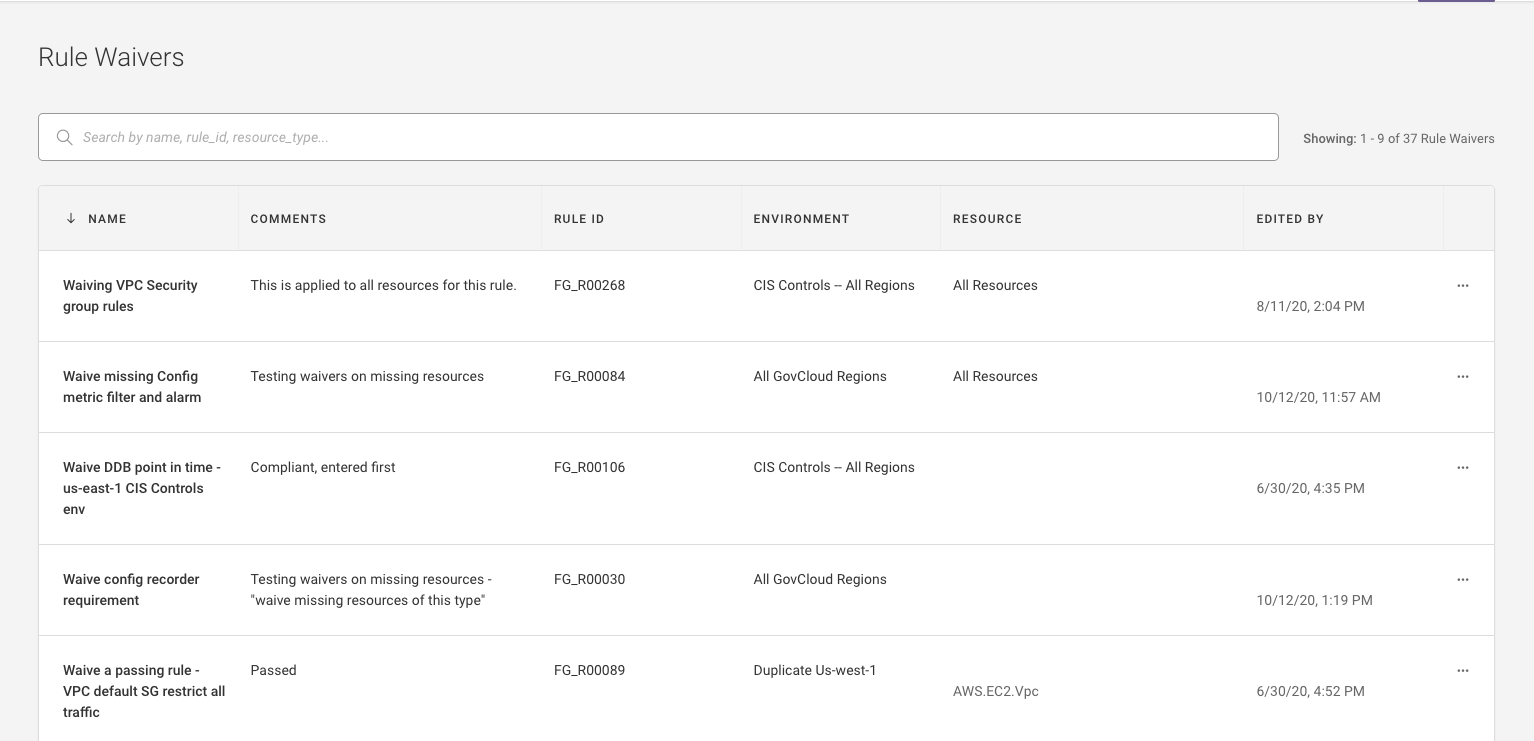
This release includes a number of enhancements to rule waivers in the Fugue UI and API:
Set an expiration date/time
Apply a waiver to all (
*) environmentsConfiguration syncing for repository environments
We’ve also added two AWS rules for configuring account contacts.
Rule Waiver Enhancements¶
Set expiration¶
You can now optionally set waiver expiration by selecting a date or interval in the Fugue UI, or via the API.
Refer to the docs for more information.
Apply to all environments¶
Previously, a rule waiver’s scope was constrained to a single environment. You can now set a waiver’s scope in the UI or API to encompass all (*) environments, if you have the appropriate Fugue role.
Refer to the docs for more information.
Configuration syncing for repository environments (beta)¶
Rule waivers that apply to repository environments can now be “synced” from the Fugue SaaS to the Regula CLI when fugue run --sync is executed. This enables security engineering teams to centrally and consistently manage how rules and waivers are configured across repositories for all developers.
Refer to the docs for more information.
Additional AWS Rules¶
We’ve added two additional rules that align with the CIS AWS Foundations Benchmark (v1.2.0, v1.3.0, and v1.4.0) and AWS Well-Architected Framework (v2020-07-02):
Account alternate contact should be configured (FG_R00501)
Account security alternate contact should be configured (FG_R00502)
These rules are disabled by default. Refer to the docs for more information.
2022.03.03¶
Extended AWS Service Coverage (limited beta)¶
Fugue now supports the AWS.Account.AlternateContact resource type, which will enable rules for checking whether an AWS account has the appropriate security, billing, or operations contacts configured If you are interested in gaining access to this beta resource, please email support@fugue.co.
Please ensure that the Fugue IAM Role has the "account:GetAlternateContact" permission added to the inline IAM policy. Refer to the docs for more information.
2022.02.24¶
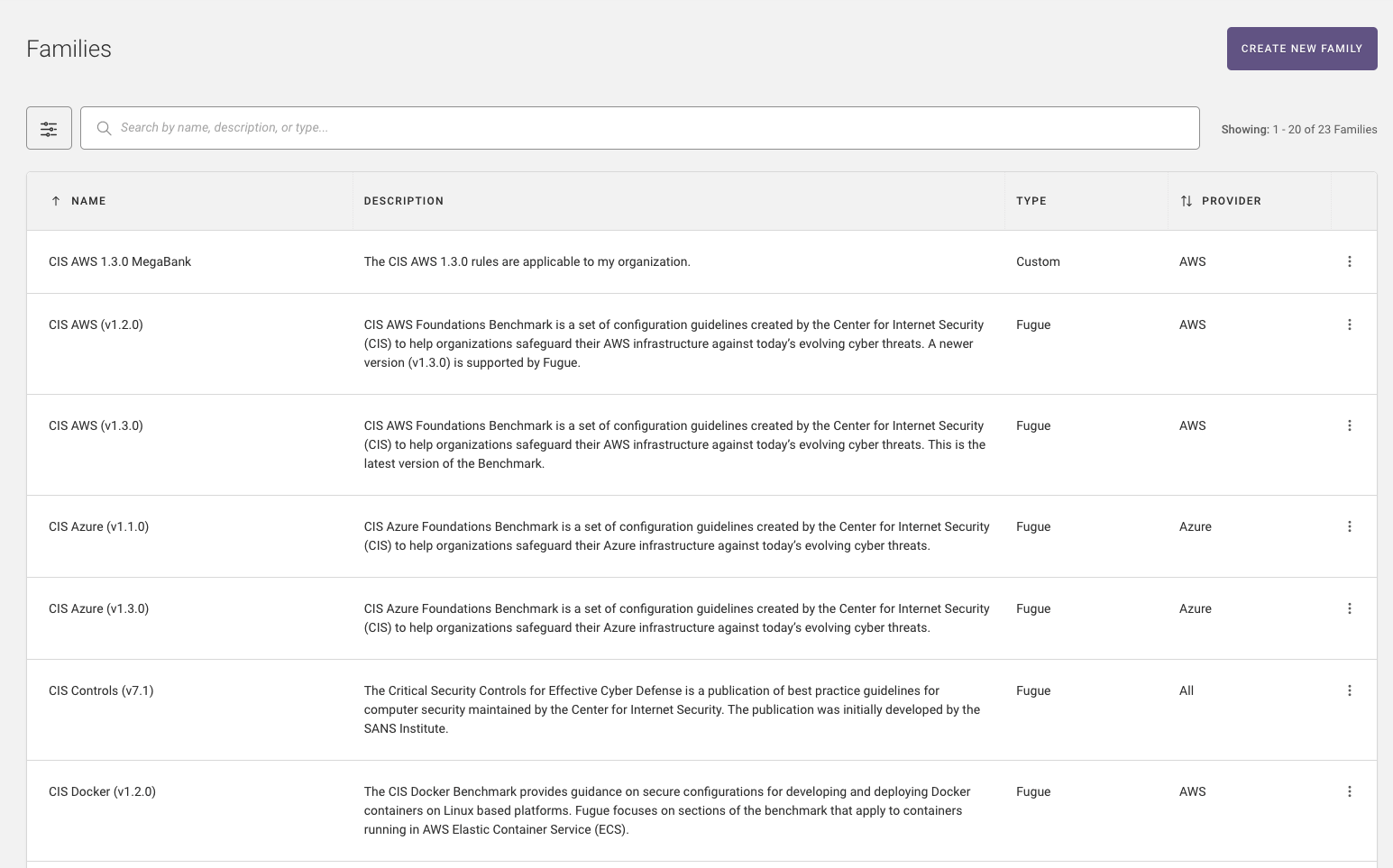
Custom Families (General Availability)¶
Create custom families based on the rules you want to enforce on the Rules, Families pages or from the API or CLI. Refer to the documentation for more information.
Report Performance Improvements¶
The page load time for reports is improved by 36%.
Fugue CLI Enhancements¶
Support for creating and updating repository environments via the CLI. Refer to the documentation for more information.
2022.02.07¶
Custom Families & AWS ARNs in Reports¶
The Current Rule Results and Current Rule Violations reports now include custom families in “compliance family” filters.
The Current Rule Results, Current Rule Violations, and Resources reports now include a “native ID” field that includes a unique resource identifier (URI) that is an address or path to a resource. For AWS, the “native ID” for a resource may be different from its “resource ID.” As an example, an Amazon EC2 instance will have an instance ID (e.g., “i-031c0dc19de2fb70c”) in the “resource ID” field, and an ARN (e.g.,
"arn:aws:ec2:us-east-1:<account-id>:i-031c0dc19de2fb70c") in the “native ID” field. The “Resource ID” and “Native ID” fields will include identical information for Azure (resource ID) and Google Cloud (full resource name).
2022.02.03¶
Additional AWS Region¶
Fugue now supports the AWS eu-north-1 (Stockholm) region. If you have * regions selected for a Fugue AWS environment, the Stockholm region is automatically added to your environment(s). As a result, you may see new compliance events and an increase in Resources Under Management (RUM).
2022.01.20¶
This release includes:
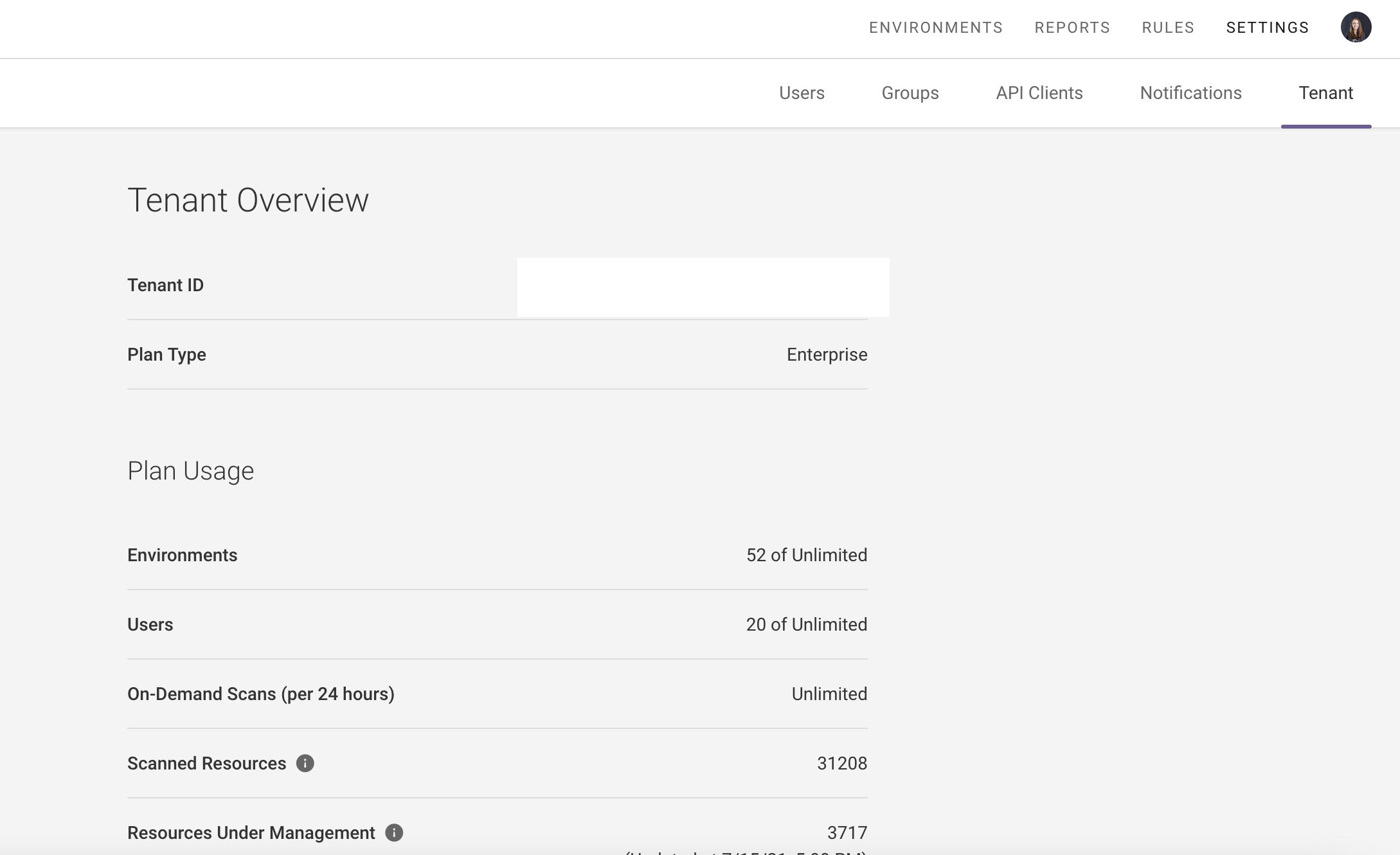
Billing Metrics Dashboard¶
The Billing Metrics Dashboard provides an aggregate view of the number of Resources Under Management (RUM) and scanned resources for a tenant or organization, as well as a breakdown by environment (in a tenant report) or tenant (in an organization report). Refer to the docs for more information.
Visualizer SVG Export¶
Visualizer supports exporting a .SVG file of your visualized infrastructure. SVG is a common file format that tools such as Visio, LucidChart, and OmniGraffle are able to consume, enabling you to easily edit visualizer output for your own purposes. Refer to the docs for more information.
Repository Environment Configuration Syncing (beta)¶
Fugue IaC now supports syncing configurations (which families and rules are enabled) for your repository environments in the SaaS to Regula. When Regula operates in “sync” mode (e.g., regula run --sync), whichever families and rules are enabled on a given repository environment will be executed against your directory/IaC files. Refer to the docs for more information.
Additional AWS Regions (coming soon)¶
Fugue will be adding AWS region support as part of the next release for:
Europe: Stockholm (eu-north-1)
Europe: Milan (eu-south-1)
Middle East: Bahrain (me-south-1)
If you have * regions for a Fugue environment, Europe (Stockholm), Europe (Milan) and Middle East (Bahrain) will be automatically added to your environment(s). As a result, you may see new compliance events and an increase in Resources Under Management (RUM). Note, AWS requires that you opt-in to support Europe (Milan), and Middle East (Bahrain). Fugue will not scan these regions if you have not opted in. See AWS docs for more information.
These regions will be available in the subsequent production release slated for February 3, 2022.
Bug Fix¶
We resolved an issue where the rule “IAM roles used for trust relationships should have MFA or external IDs (FG_R00255)” was evaluating statements for the
sts:AssumeRoleandsts:TagSessionactions. The rule is updated to only evaluate statements with thests:AssumeRoleaction.
2021.12.17¶
This release includes a new Fugue rule that confirms AWS WAFv2 resources are using the AWS-managed rule group used to block request patterns associated with the Log4j vulnerability (CVE-2021-44228). Specifically, the Fugue rule checks for the presence of the “AWSManagedRulesKnownBadInputsRuleSet” to protect against malicious inputs, including the “Log4JRCE” and “Log4JRCE_ALL_HEADER” WAFv2 rules. The Fugue rule also ensures the WAFv2 rules are not set to “count” mode.
This rule is available in Fugue SaaS and Regula. Refer to the Regula and Fugue docs for more information.
WAFv2 web ACLs should include the ‘AWSManagedRulesKnownBadInputsRuleSet’ managed rule group (FG_R00500)
More information on how to use AWS services to protect against the Log4j vulnerability are available from AWS here.
2021.12.09¶
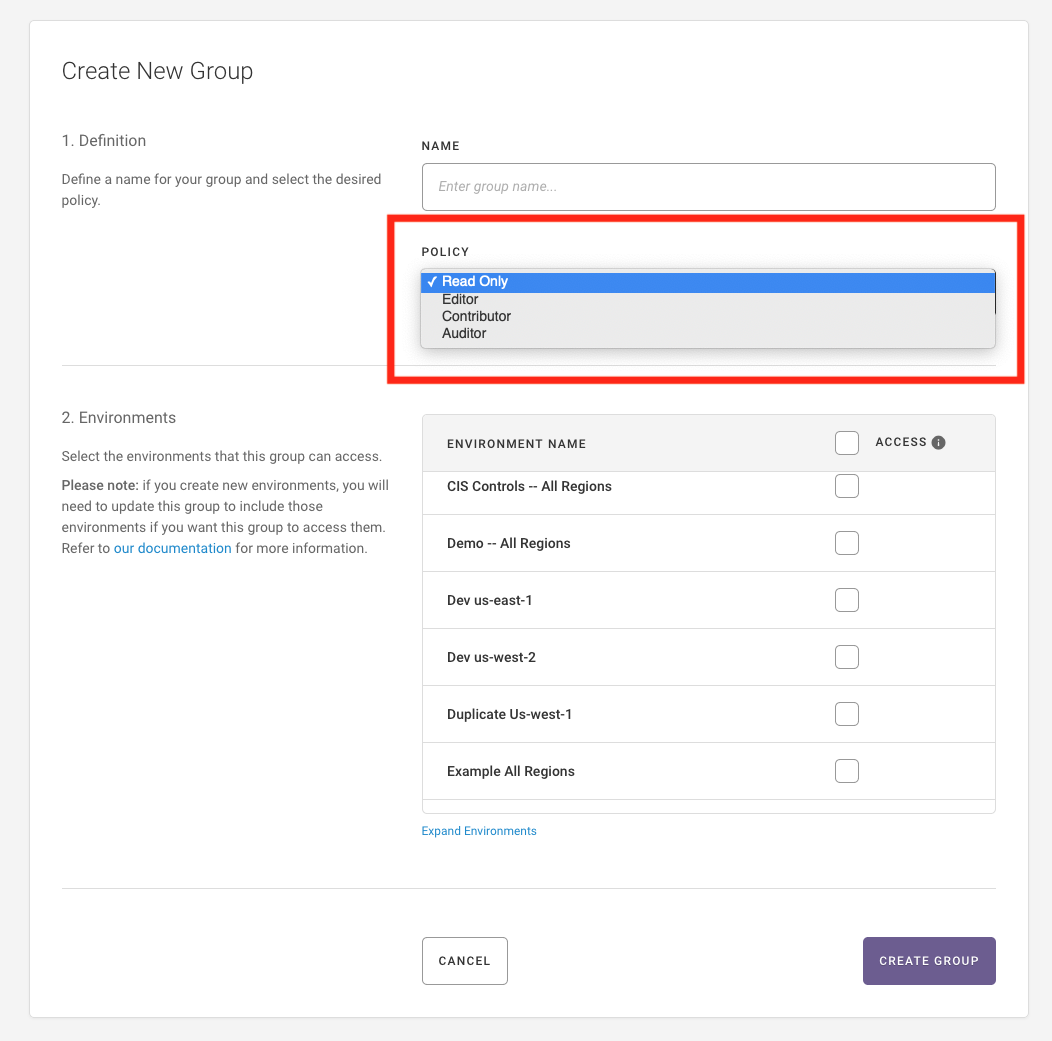
Assign all Environments (Current and Future) to an RBAC Group¶
Admin users can now assign an RBAC group access to all current and future environments in a tenant via the UI, API, and CLI. This simplifies the environment onboarding process, as users no longer need to update RBAC groups to accommodate new environments. Refer to the docs for more information.
2021.12.02¶
This release includes:
Organization Reports¶
Root tenant users can now view dashboards and reports to review and drill down on security and compliance results for all child tenants in an Organization. Fugue supports the following Organization reports:
Compliance Posture Dashboard
Resources Dashboard
Compliance Family-Specific Dashboards
Current Rule Violations Report
Current Rule Results Report
Resources Report
Refer to the docs for more information.
Fugue has added a new RBAC policy:
Organization Report Viewer, which grants users access to view the Organization and Root Tenant reports. Refer to the docs for more information.
RBAC for API Clients¶
Admin users can now assign API clients to a group/RBAC policy. This enables more tightly scoped clients for automation and Fugue IaC use cases. To support this, Fugue has added a new RBAC policy:
IaC Scanner, which allows users to use
regula run --sync --uploadto scan a repository environment and upload the results
Refer to the docs for more information.
UI/UX Improvements: Reports, Visualizer, & Environment Overview Pages¶
We’ve made improvements to pages in our UI as follows:
Reports Overview: Group reports by category and search for reports by name or description
Improved filtering on reports
Visualizer: Copy attribute information in the resource details panel
Rules: View rule definitions for custom rules
Environments Overview: Updated the expand/condense toggle
Improvements to Regula¶
Combined regula sync into regula run. Run regula run --sync --upload to kick off a scan and upload the results into the Fugue SaaS. Refer to the Regula documentation and Setup - Repository (limited beta) for more information.
2021.11.11¶
Bug Fixes¶
Resolved an issue where users could not create a notification for 900+ environments
Resolved an issue where users could not use data export when multi-tenant is enabled
Resolved an issue where users could update rules with bad severity and providers using the PATCH/rules/{rule_id} endpoint
2021.10.28¶
This release includes:
Fugue IaC: Kubernetes Manifests¶
Fugue added support for Kubernetes YAML manifest files as part of Fugue’s Infrastructure as Code (IaC) offering. Support includes:
Onboard a git repository that contains Kubernetes YAML manifest files
View manifest resources and security/compliance results in the UI and reports
Inspect Kubernetes YAML manifest files within Visualizer
Refer to the documentation for more information.
Additional Improvements and Bug Fixes¶
Added an AWS rule: Lambda function policies should not allow global access (FG_R00276)
Resolved an issue where API client “last authorized” time was not always updated
Resolved an issue where searching was not working on the Families page
Visualizer
Resolved an issue where Azure AD resources were displaying as “unknown”
Resolved an issue where AWS Subnet labels were out of order for some environments
Resolved an issue where a connection line was rendering incorrectly
Added support to visualize AWS.S3.Bucket.Policy (POLICY)
2021.10.18¶
This release includes:
Repository Support in Reports¶
Reports now include Repository environments, which include Infrastructure as Code (IaC) files used by tools such as Terraform and CloudFormation.
Always Enabled Option for Families¶
Families now have the option to always be enabled on all scans for environments in a tenant.
Visualizer: Expanded AWS Service Coverage¶
Expanded AWS service coverage to include:
AWS.S3.Bucket.Inventory (INVENTORY)
AWS.S3.Bucket.Metric (METRIC)
AWS.S3.Bucket.Notification (NOTIFY)
AWS.S3.Bucket.Policy (POLICY)
UX Improvement & Bug Fix¶
Improved the UX by making all input type fields searchable (e.g., Family drop-down on the Families page or Severity drop-down on the Create New Rule page)
Resolved an issue where Repository was missing from the Swagger Documentation
2021.09.30¶
This release includes:
Compliance Family Updates (limited beta)¶
Fugue has added:
AWS Well-Architected Framework (v2020-07-02); the Well-Architected Framework describes the key concepts, design principles, and architectural best practices for designing and running workloads on AWS. Fugue supports 16 controls from the Security and Reliability “pillars”
The latest versions of the CIS Foundations Benchmarks for AWS (v1.4.0) and Google Cloud (v1.2.0)
Reports were added for each of the compliance families above where you can view compliance by resource type, severity, and environment.
Please contact support@fugue.co for access and refer to our documentation for more information.
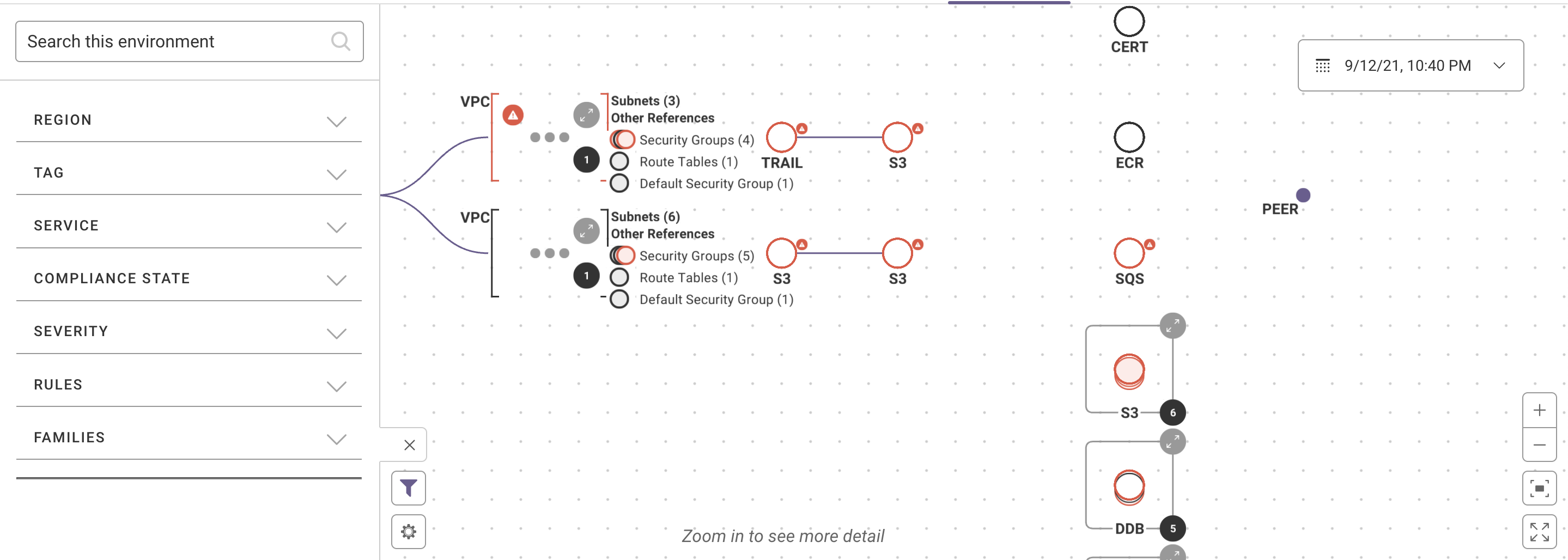
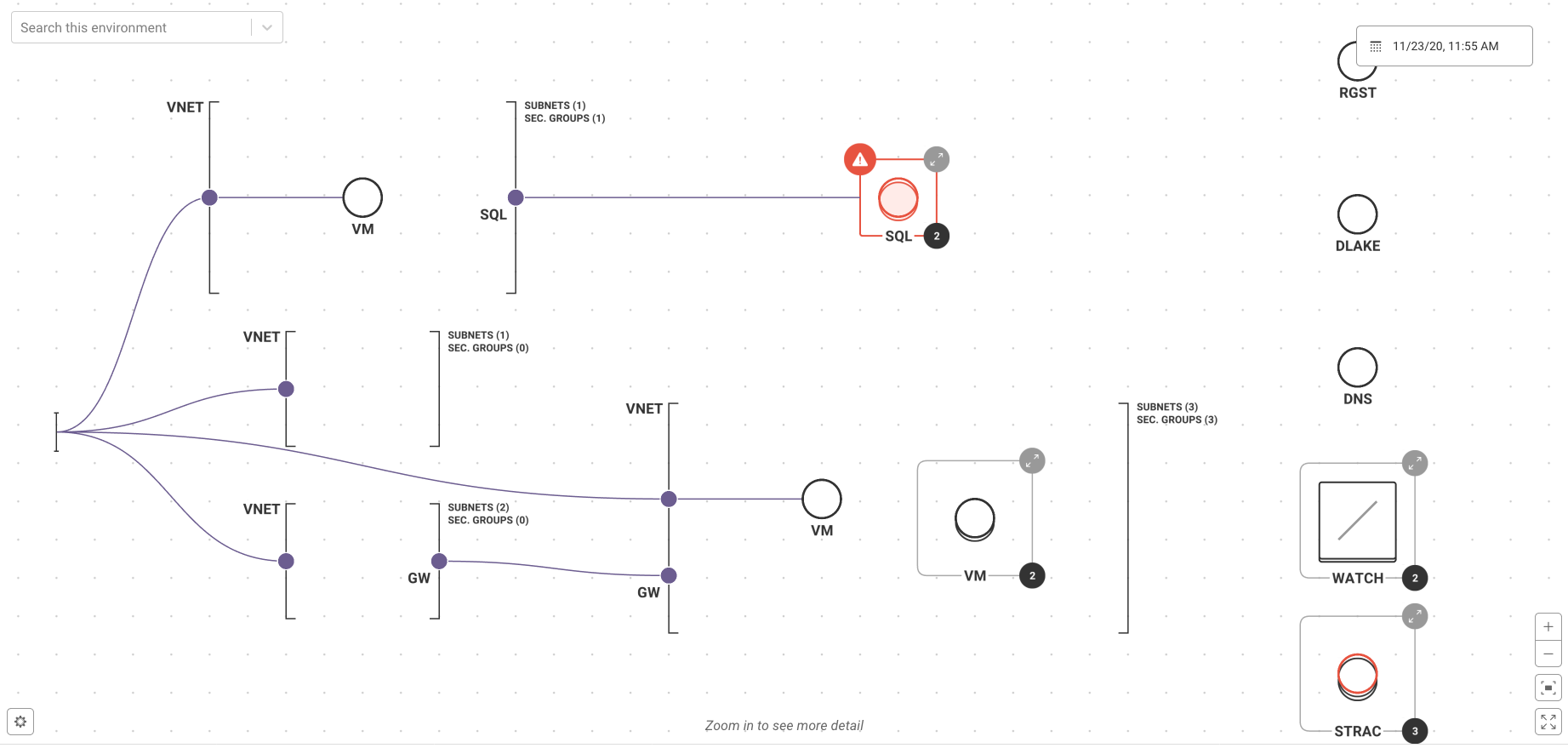
Visualizer: Additional Filter Capabilities¶
We have added filtering by families, rules, severity, and compliance state to the Visualizer. Filtered views can be saved and shared via URL. Refer to the documentation for additional information.
Regula Kubernetes Support¶
Regula supports scanning Kubernetes YAML manifest files and now includes 20 rules that map to the CIS Kubernetes Foundations Benchmark (v1.6.1). Refer to the documentation for more information.
Fugue Terraform Provider Updates¶
We support:
New data sources for querying Fugue
New resource type for custom compliance families
Refer to the documentation for more information.
Bug Fixes¶
Resolved an issue where the rule “Auto Scaling groups should span two or more availability zones (FG_R00014)” was only checking the number of availability zones in the availability_zones property. The rule is updated to check either the availability_zones property of the autoscaling group or the availability zones from subnets that are set through the vpc_zone_identifier property.
Resolved an issue in Visualizer where compliance errors would display when disabled.
2021.09.16¶
Visualizer: Additional Filter Capabilities (limited beta)¶
Visualizer now supports filtering by families, rules, severity, and compliance state. Filtered views can be exported. Refer to the online user guide for additional information. To request access, contact support@fugue.co.
2021.09.02¶
Fugue IaC: limited beta¶
Fugue added support for Infrastructure as Code (IaC) to its multi-cloud security platform. Support includes:
Onboard git repositories to Fugue as environments
View IaC resources and security/compliance results in the UI
Inspect IaC templates within Visualizer
Fugue IaC security integrates with Regula to scan code files locally and in CI/CD pipelines. To request access, contact support@fugue.co. For more information, refer to the documentation.
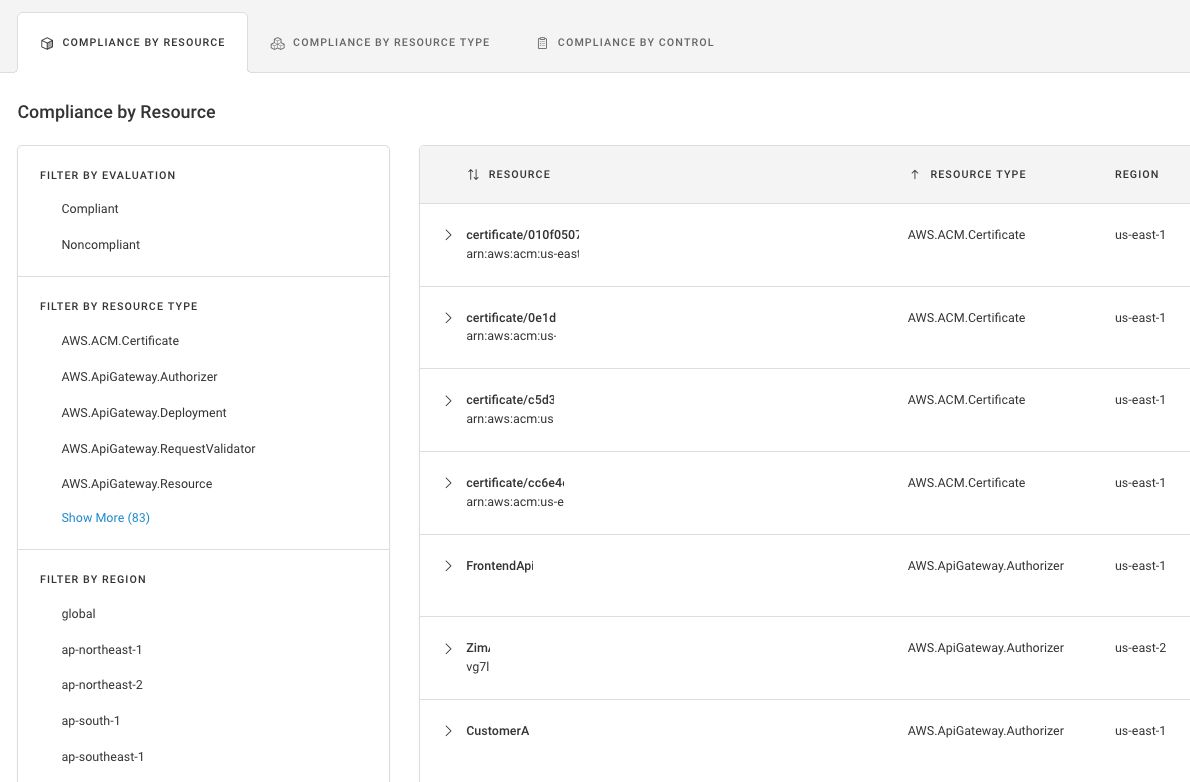
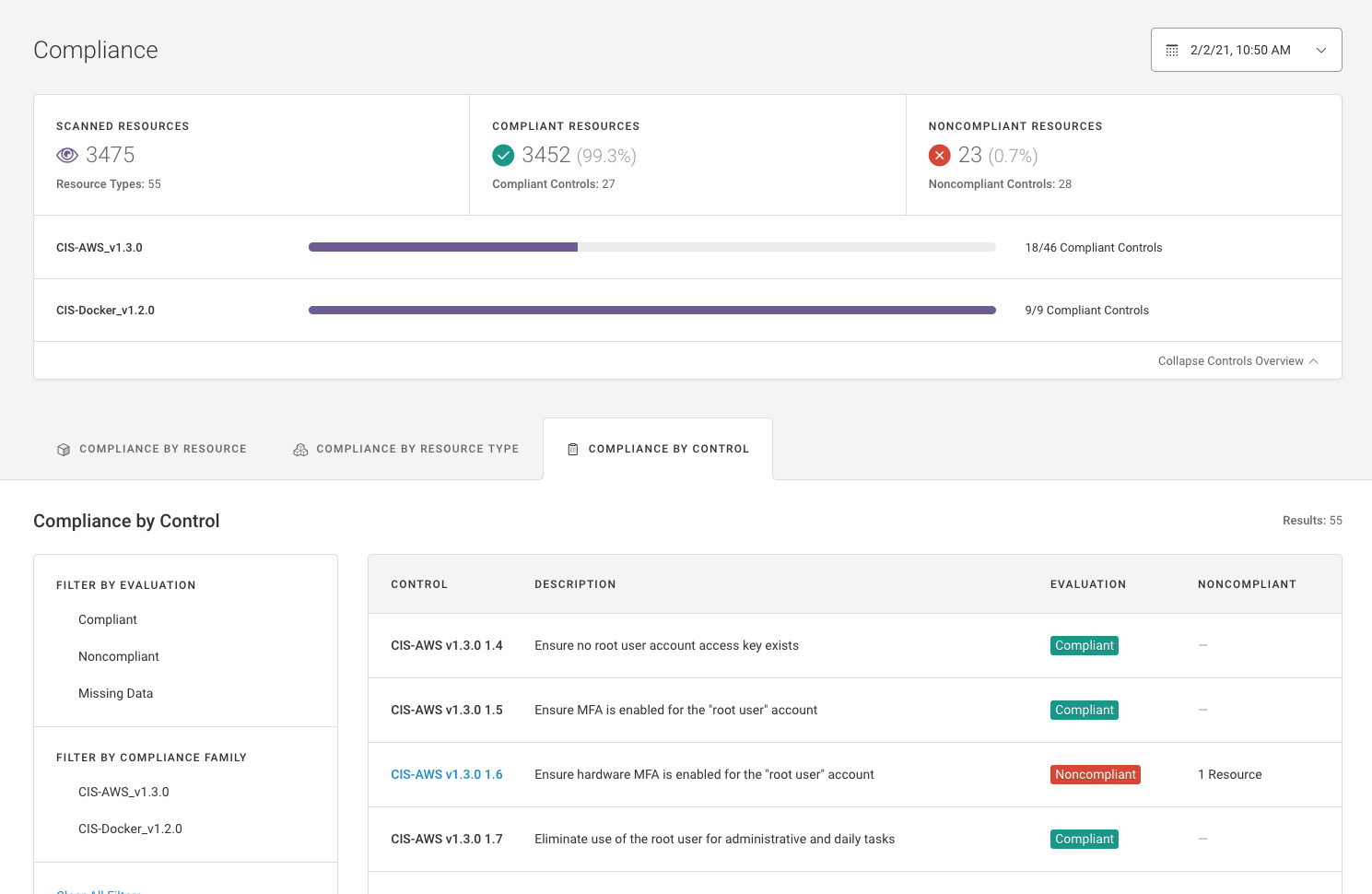
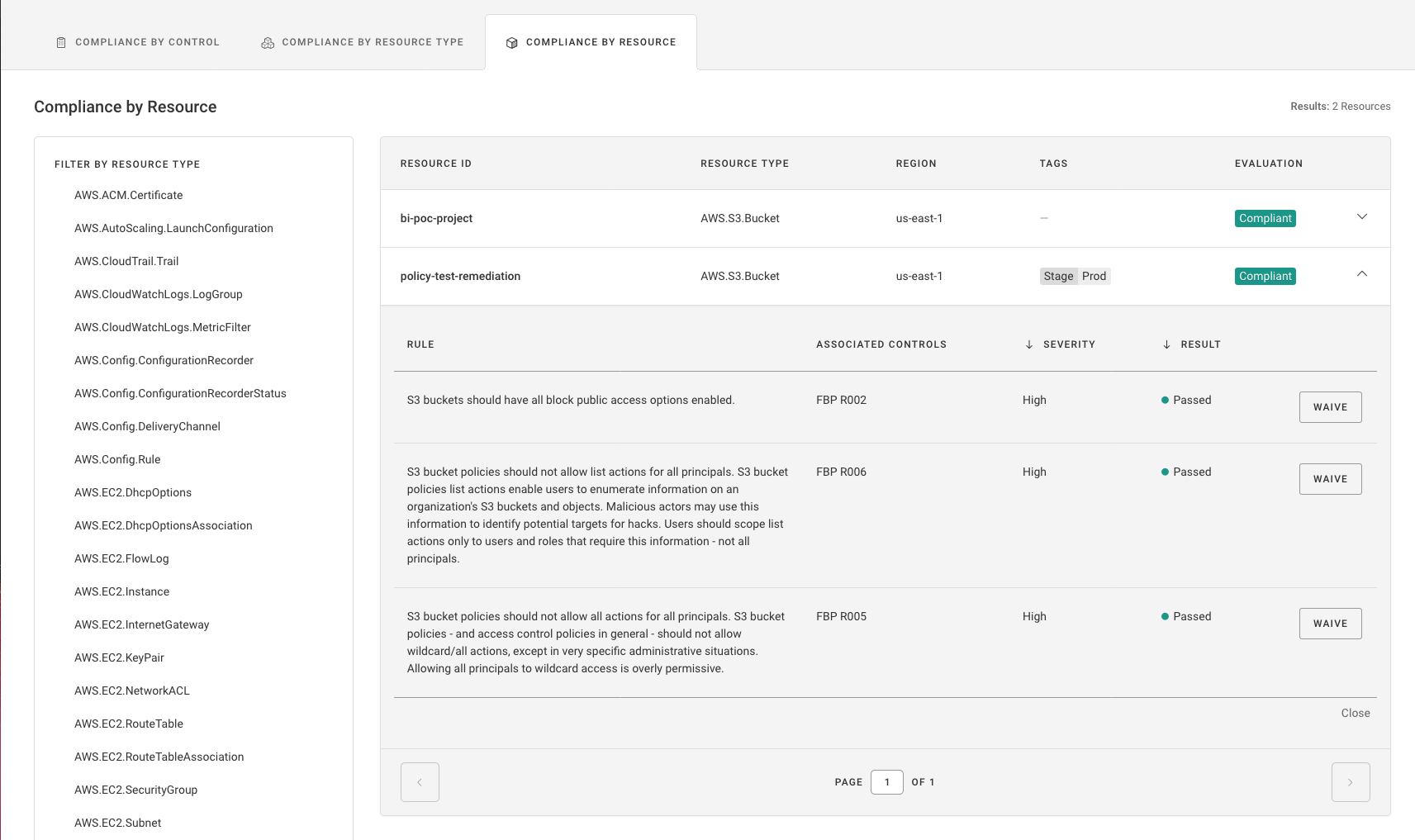
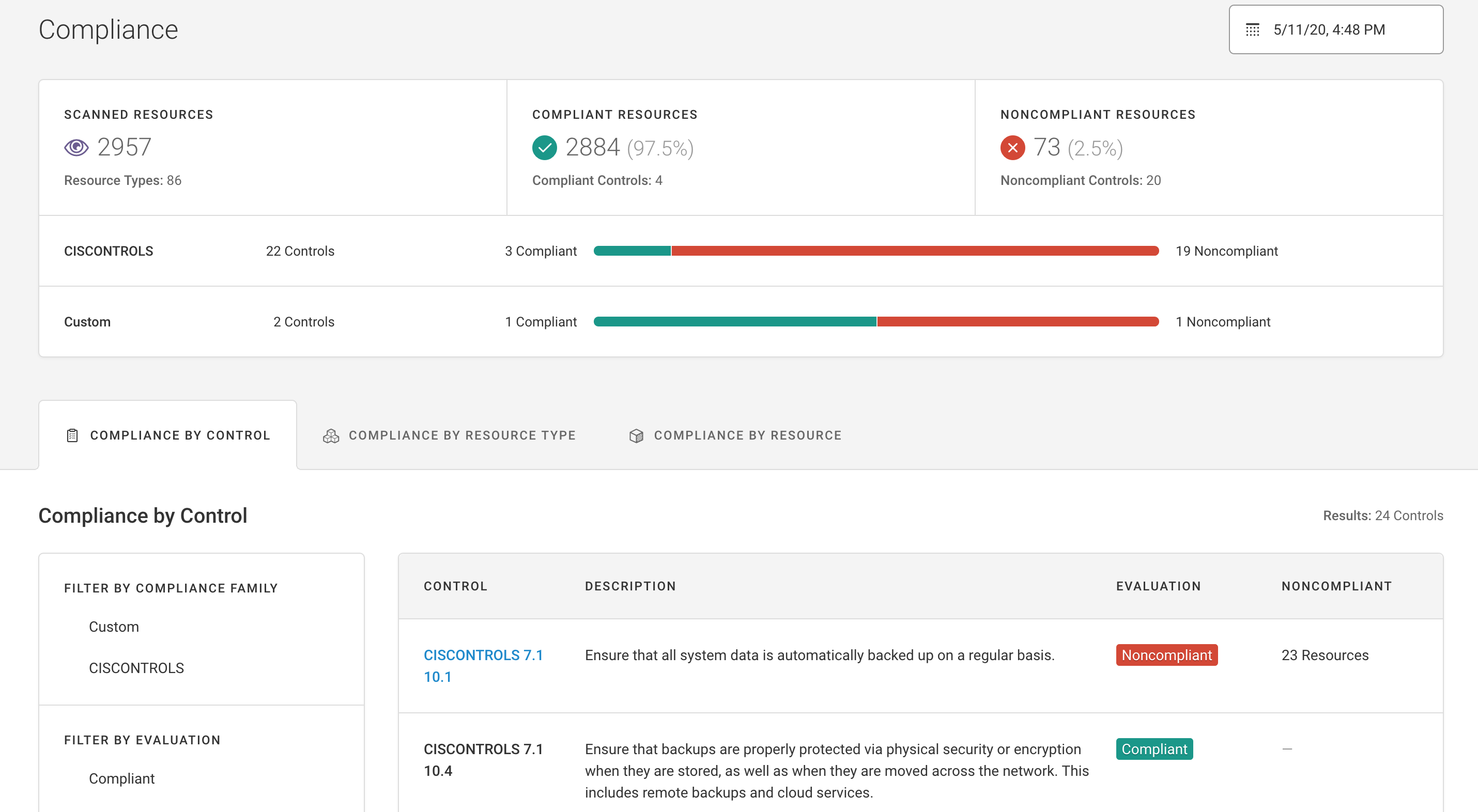
UX Improvements to the Compliance Pages¶
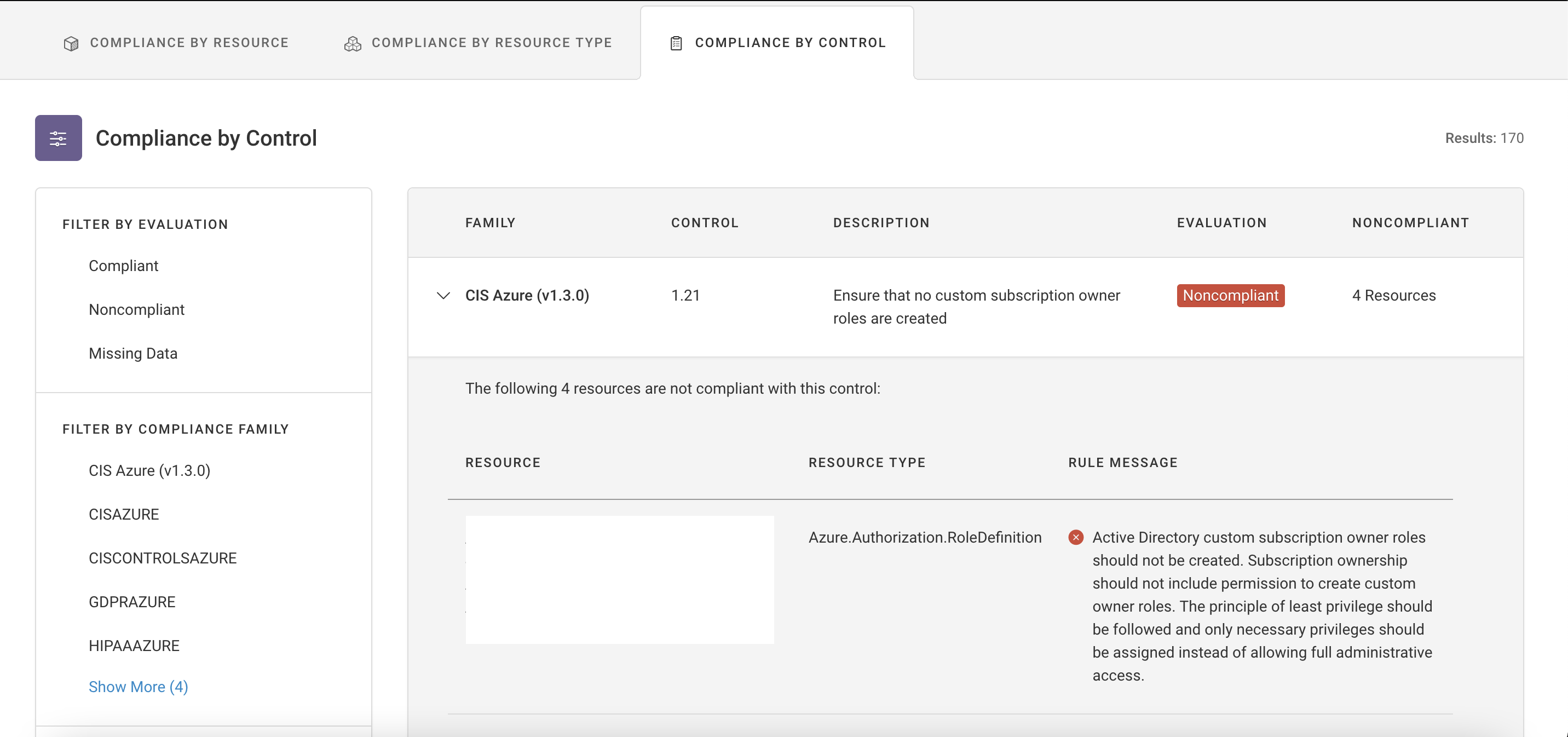
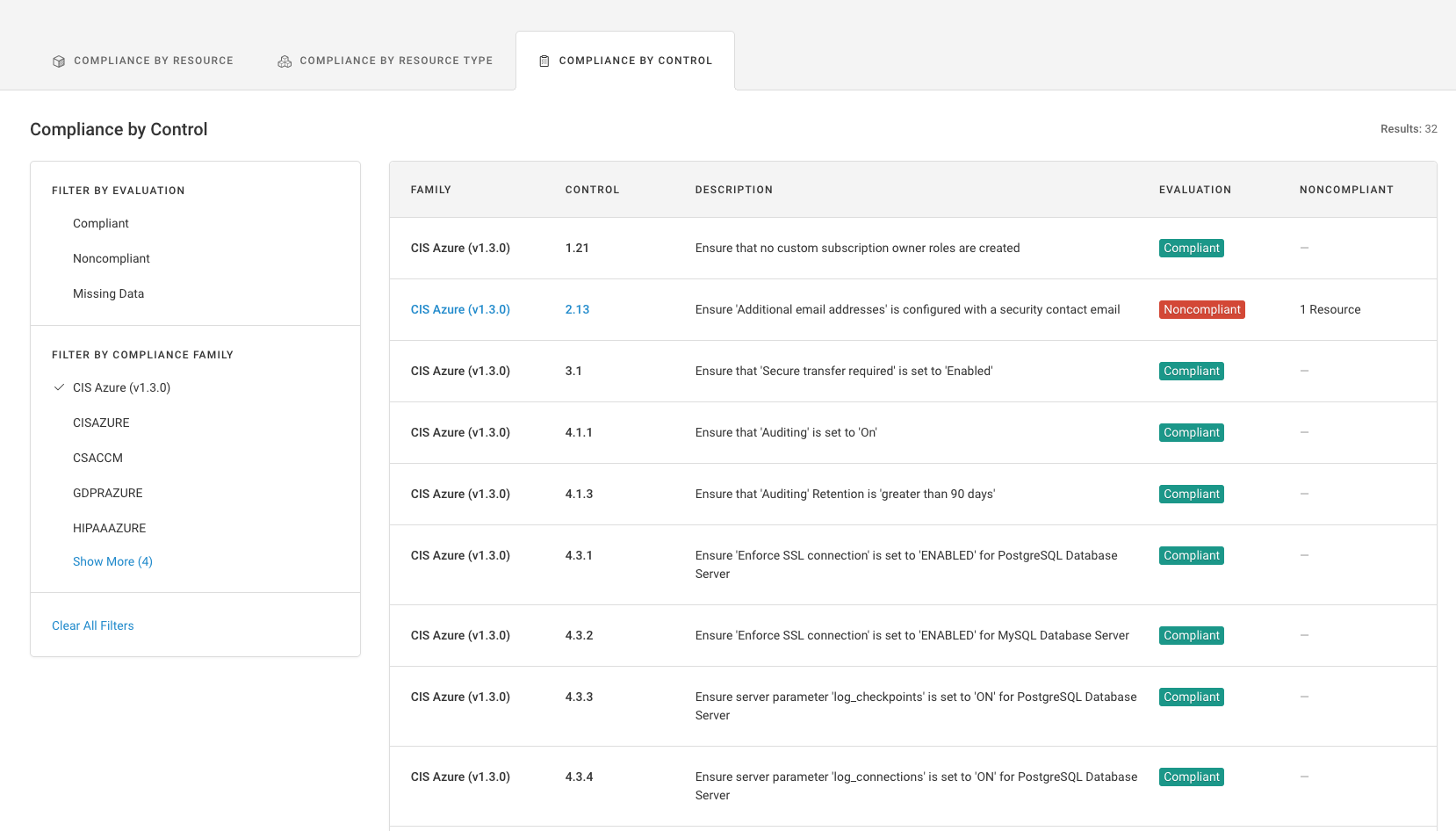
Fugue upgraded the Compliance by Resource Type and Compliance by Control pages to display all data in inline tables rather than separate modals.
Additional Azure Rules¶
Fugue added 6 new Azure rules that map to the CIS Azure Foundations Benchmark v1.3.0:
CIS-Azure_v1.3.0_2.11: Security Center monitoring agent should be automatically provisioned (FG_R00478)
CIS-Azure_v1.3.0_2.14: Security Center setting ‘Notify about alerts with the following severity’ should be set to ‘High’ (FG_R00468)
CIS-Azure_v1.3.0_2.15: Security Center setting ‘All users with the following roles’ should be set to ‘Owner’ (FG_R00469)
CIS-Azure_v1.3.0_4.1.2: SQL Database transparent data encryption should be enabled (FG_R00470)
CIS-Azure_v1.3.0_4.4: SQL Server Active Directory Admin should be configured (FG_R00471)
CIS-Azure_v1.3.0_4.5: SQL Server TDE protector should be encrypted with a Key Vault CMK (FG_R00472)
2021.08.19¶
Visualizer: Expanded AWS & Azure Service Coverage¶
Fugue expanded AWS service coverage support for Visualizer to include:
AWS.AccessAnalyzer.Analyzer (ANALYZ)
AWS.ApiGatewayV2.Api (API)
AWS.ApiGatewayV2.ApiMapping (MAPPING)
AWS.ApiGatewayV2.Authorizer (AUTHORIZR)
AWS.ApiGatewayV2.Deployment (DEPLOY)
AWS.ApiGatewayV2.DomainName (DOMAIN)
AWS.ApiGatewayV2.Integration (INTEG)
AWS.ApiGatewayV2.IntegrationResponse (RESPONSE)
AWS.ApiGatewayV2.Model (MODEL)
AWS.ApiGatewayV2.Route (ROUTE)
AWS.ApiGatewayV2.RouteResponse (RESPONSE)
AWS.ApiGatewayV2.Stage (STAGE)
AWS.ApiGatewayV2.VpcLink (GTW LNK)
AWS.Athena.Workgroup (ATHENA)
AWS.CloudFormation.Stack (STACK)
AWS.CloudFormation.StackSet (STACKSET)
AWS.DocDB.Cluster (DOC DB)
AWS.DocDB.ClusterInstance (DB INST)
AWS.DocDB.ClusterSnapshot (SNAPSHOT)
AWS.EC2.Snapshot (SNAPSHOT)
AWS.EC2.Volume (VOLUME)
AWS.ECR.LifecyclePolicy (LIFECYCLE)
AWS.ECR.RepositoryPolicy (POLICY)
AWS.Elasticsearch.Domain (ESEARCH)
AWS.Glue.CatalogDatabase (GLUE DB)
AWS.Glue.CatalogTable (TABLE)
AWS.Glue.Connection (CONNECTION)
AWS.Glue.Crawler (CRAWLER)
AWS.Glue.Job (GLUE JOB)
AWS.Glue.SecurityConfiguration (SEC CFG)
AWS.Glue.Trigger (TRIGGER)
AWS.Glue.Workflow (WORKFLOW)
AWS.IAM.ServerCertificate (IAMSRV)
AWS.Lambda.Permission (PERMISSION)
AWS.Neptune.Cluster (NEPTUNE)
AWS.Neptune.ClusterInstance (NPT INST)
AWS.Neptune.ClusterSnapshot (SNAPSHOT)
AWS.RAM.PrincipalAssociation (PRINCIPAL)
AWS.RAM.ResourceAssociation (RESOURCE)
AWS.RAM.ResourceShare (RAM)
AWS.RDS.Snapshot (SNAPSHOT)
AWS.S3.AccountPublicAccessBlock (PUB ACCESS)
AWS.Sagemaker.Endpoint (SAGE ENDPT)
AWS.Sagemaker.EndpointConfiguration (CONFIG)
AWS.Sagemaker.Model (SAGE MDL)
AWS.Sagemaker.NotebookInstance (SAGE NOTE)
AWS.Sagemaker.NotebookInstanceLifecycleConfiguration (LIFECYCLE)
AWS.SecretsManager.Secret (SECRET)
AWS.Workspaces.Directory (WORK DIR)
AWS.Workspaces.IPGroup (IP GROUP)
AWS.Workspaces.Workspace (WORKSP)
Fugue expanded Azure service coverage support for Visualizer to include:
Azure.ActiveDirectory.Application (APP)
Azure.ActiveDirectory.ServicePrincipal (PRINCPL)
Azure.ActiveDirectory.User (AD USER)
Azure.Authorization.PolicyAssignment (PLCY ASSIGN)
Azure.Authorization.RoleAssignment (ROLE ASSIGN)
Azure.Authorization.RoleDefinition (ROLE DEF)
Azure.Compute.VirtualMachineScaleSet (SCALE SET)
Azure.Container.Group (GROUP)
Azure.ManagedIdentity.Identity (MNGED ID)
Azure.MySQL.ConfigurationSet (CONFIG SET)
Azure.Network.DDoSProtectionPlan (DDOS)
Azure.Network.NetworkInterface (NETINT)
Azure.Network.RouteTable (ROUTE TBL)
Azure.PostgreSQL.ConfigurationSet (CONFIG SET)
Azure.SecurityCenter.Contact (CONTACT)
Azure.SecurityCenter.SubscriptionPricing (PRICING)
Azure.SQL.ElasticPool (POOL)
Azure.Web.FunctionApp (FN APP)
Refer to the documentation for more information.
Regula Improvements¶
Fugue’s Regula open source infrastructure-as-code (IaC) security project supports an optional .regula.yaml configuration file to set some default options and inputs for regula run. For example, you can set the minimum severity that will result in a non-zero exit code. Refer to the documentation for more information.
2021.08.05¶
Custom Families: beta¶
Fugue supports creating custom families from the UI, API, or CLI. You create custom families based on the rules you want to enforce on the Rules or (new) Families pages.
Here is an example of creating a custom family on the Families page. Refer to the documentation for more information.
Here is an example of creating a custom family on the Rules page. Refer to the documentation for more information.
The new Families page can be used to view/configure Fugue-defined and custom families. Refer to the documentation for more information.
Additional Azure Rules¶
Fugue added 15 new Azure rules that map to the CIS Azure Foundations Benchmark v1.3.0:
CIS-Azure_v1.3.0_2.1: Azure Defender should be enabled for Virtual Machines (FG_R00455)
CIS-Azure_v1.3.0_2.2: Azure Defender should be enabled for App Services (FG_R00456)
CIS-Azure_v1.3.0_2.3: Azure Defender should be enabled for SQL Servers (FG_R00457)
CIS-Azure_v1.3.0_2.4: Azure Defender should be enabled for SQL Servers on Virtual Machines (FG_R00458)
CIS-Azure_v1.3.0_2.5: Azure Defender should be enabled for Storage Accounts (FG_R00459)
CIS-Azure_v1.3.0_2.6: Azure Defender should be enabled for Kubernetes Services (FG_R00460)
CIS-Azure_v1.3.0_2.7: Azure Defender should be enabled for Container Registries (FG_R00461)
CIS-Azure_v1.3.0_2.8: Azure Defender should be enabled for Key Vaults (FG_R00462)
CIS-Azure_v1.3.0_3.6: Storage Account default network access rules should deny all traffic(FG_R00154)
CIS-Azure_v1.3.0_3.7: Storage Accounts should have ‘Trusted Microsoft Services’ enabled (FG_R00208)
CIS-Azure_v1.3.0_4.2.2: SQL Server vulnerability assessments should be enabled (FG_R00463)
CIS-Azure_v1.3.0_4.2.3: SQL Server ‘periodic recurring scans’ for vulnerability assessments should be enabled (FG_R00464)
CIS-Azure_v1.3.0_4.2.4: SQL Server ‘send scan reports’ for vulnerability assessments should be enabled (FG_R00465)
CIS-Azure_v1.3.0_4.2.5: SQL Server ‘also send email notifications to admins and subscription owners’ for vulnerability assessments should be enabled (FG_R00466)
CIS-Azure_v1.3.0_7.7: Virtual Machine legacy virtual hard disks should be encrypted (FG_R00467)
2021.07.09¶
AWS Resource Types (beta)¶
Fugue has added support for the following 50 new AWS resource types across 17 services:
AWS.AccessAnalyzer.Analyzer
AWS.ApiGatewayV2.Api
AWS.ApiGatewayV2.ApiMapping
AWS.ApiGatewayV2.Authorizer
AWS.ApiGatewayV2.Deployment
AWS.ApiGatewayV2.DomainName
AWS.ApiGatewayV2.Integration
AWS.ApiGatewayV2.IntegrationResponse
AWS.ApiGatewayV2.Model
AWS.ApiGatewayV2.Route
AWS.ApiGatewayV2.RouteResponse
AWS.ApiGatewayV2.Stage
AWS.ApiGatewayV2.VpcLink
AWS.Athena.Workgroup
AWS.CloudFormation.Stack
AWS.CloudFormation.StackSet
AWS.DocDB.Cluster
AWS.DocDB.ClusterInstance
AWS.DocDB.ClusterSnapshot
AWS.EC2.Snapshot
AWS.ECR.LifecyclePolicy
AWS.ECR.RepositoryPolicy
AWS.Elasticsearch.Domain
AWS.Glue.CatalogDatabase
AWS.Glue.CatalogTable
AWS.Glue.Connection
AWS.Glue.Crawler
AWS.Glue.Job
AWS.Glue.SecurityConfiguration
AWS.Glue.Trigger
AWS.Glue.Workflow
AWS.IAM.ServerCertificate
AWS.Lambda.Permission
AWS.Neptune.Cluster
AWS.Neptune.ClusterInstance
AWS.Neptune.ClusterSnapshot
AWS.RAM.PrincipalAssociation
AWS.RAM.ResourceAssociation
AWS.RAM.ResourceShare
AWS.RDS.ClusterInstance
AWS.RDS.Snapshot
AWS.S3.AccountPublicAccessBlock
AWS.Sagemaker.Endpoint
AWS.Sagemaker.EndpointConfiguration
AWS.Sagemaker.Model
AWS.Sagemaker.NotebookInstance
AWS.Sagemaker.NotebookInstanceLifecycleConfiguration
AWS.Workspaces.Directory
AWS.Workspaces.IPGroup
AWS.Workspaces.Workspace
These resource types are in beta, so please contact support@fugue.co for access and refer to our documentation for more information.
Once you add the beta resource types to an environment, you must update the AWS Identity & Access Management (IAM) role so Fugue can access the resource configuration properly. Refer to How To: Update the Fugue IAM Role for more information.
2021.06.24¶
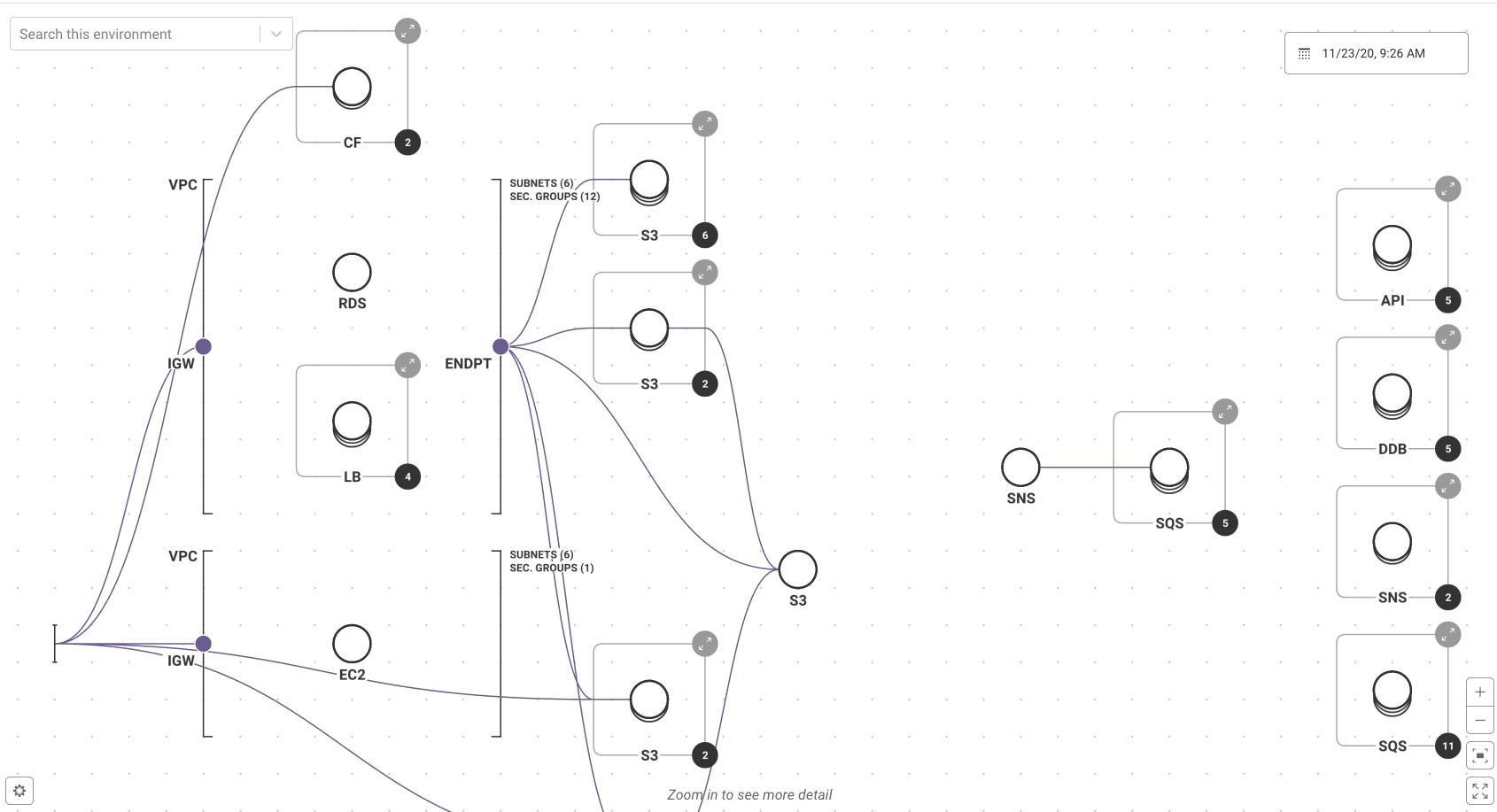
Pods for Visualizer¶
Fugue enhanced the visualizer by adding support for pods, which are small circles that show other resources referenced by the node resource. For example, a security group referenced by an EC2 instance displays as a pod above it. Click on the pod to view resource details about the security group. Refer to the documentation for more information.
Schedule/Send All Reports to an S3 Bucket¶
Fugue can now send and schedule reports to an AWS S3 bucket via an IAM Role. Refer to the documentation for more information.
Bug Fix¶
Resolved an issue where the rule message did not display in the product for “Storage Accounts for critical data should be encrypted with Customer Managed Key” (Rule ID: FG_R00442).
2021.06.10¶
Saved Filter State for Compliance, Baseline, and Events Pages¶
Filters that are applied on Compliance, Baseline, and Events pages can now be saved and shared via URL.
Updates CIS Azure v1.3.0 Rules¶
Fugue added 5 new rules for the CIS Azure Foundations Benchmark 1.3.0:
Rule “CloudTrail should have at least one CloudTrail trail set to a multi-region trail” (rule ID: FG_R00238) was updated to show “missing resource” instead of failing if no valid CloudTrails are found. This effectively makes the rule more sensitive to potential misconfigurations. Refer to the online user guide for additional information.
2021.05.27¶
Resource Name and Tag Patterns for Waivers¶
Fugue supports waivers based on resource name or tag patterns via the user interface, API, or CLI. Refer to the documentation for additional information.
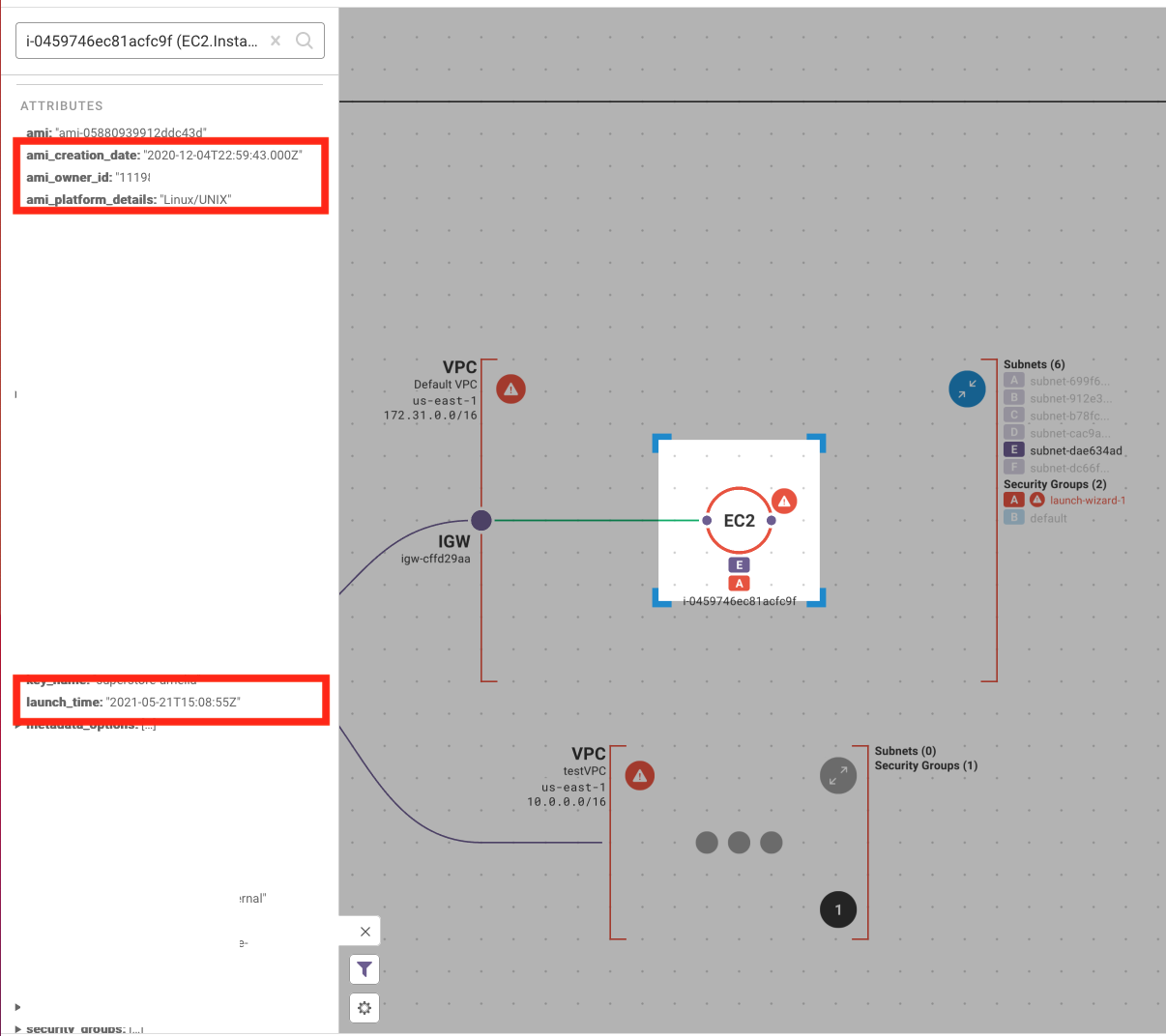
AMI & Launch Time Attributes to EC2 Instances¶
Fugue added the following AWS EC2 instance attributes:
ami_creation_date
ami_owner_id
ami_plaform_details
launch_time
You can write custom rules against these new resource attributes or view them in visualizer, as shown below.
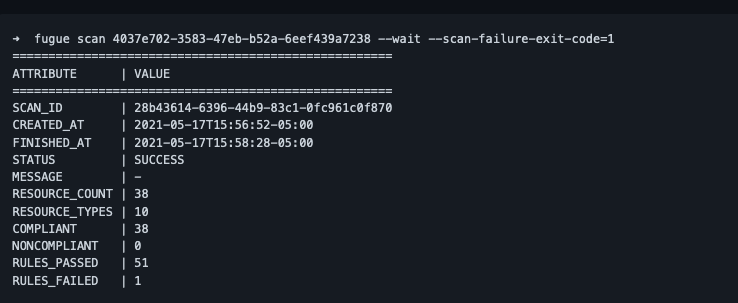
Fugue CLI Flag: Fail on Scan Failures¶
The Fugue CLI supports setting an exit code (scan-failure-exit-code) if a Fugue scan results in an error. Refer to the documentation for more information.
Regula CLI¶
Fugue’s open source Regula project for infrastructure as code (IaC) security now includes a CLI that makes using Regula even easier.
A simple “regula run” command will search through your entire repository, find all relevant infrastructure as code configurations, and evaluate them against Regula’s rule libraries.
Additional features and options include:
Running Regula on a specific input type, such as CloudFormation or Terraform files
Running Regula on a directory or individual IaC files
Specifying additional rules, or directories of rules for Regula to use
Commands for debugging and testing custom rules, such as “regula repl” and “regula test”
Get started today by installing Regula via Homebrew on a Linux or Mac machine, or by accessing the Regula Docker image here. The Regula CLI is built using Go, which means it is installed as a single self-contained binary. Documentation is available at regula.dev.
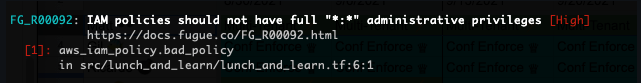
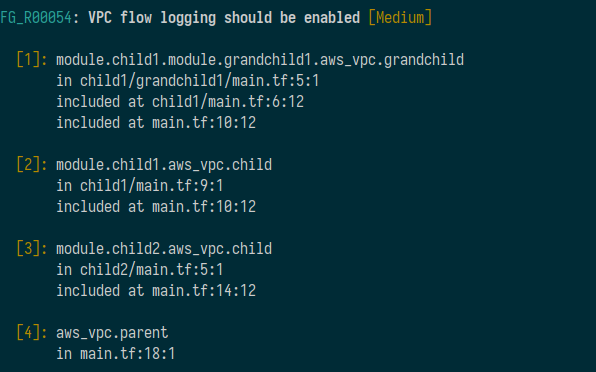
Regula Terraform HCL (.tf) Support¶
Regula now supports Terraform HCL (.tf) files directly, in addition to Terraform plan files. This enables users to check for security and compliance violations in their Terraform files earlier in the cloud development lifecycle.
Regula handles Terraform modules and can run on an entire directory or target individual files.
Additional Controls for CIS Azure 1.3.0 General Availability¶
Fugue expanded support for CIS Azure 1.3.0 by adding 10 new controls including:
Ensure Custom Role is assigned for Administering Resource Locks (CIS Azure (v1.3.0) 1.23)
Ensure soft delete is enabled for Azure Storage (CIS Azure (v1.3.0) 3.8)
Ensure storage for critical data are encrypted with Customer Managed Key (CIS Azure (v1.3.0) 3.9)
Ensure Virtual Machines are utilizing Managed Disks (CIS Azure (v1.3.0) 7.1)
Ensure that ‘OS and Data’ disks are encrypted with CMK (CIS Azure (v1.3.0) 7.2)
Ensure that ‘Unattached disks’ are encrypted with CMK (CIS Azure (v1.3.0) 7.3)
Ensure that the expiration date is set on all keys (CIS Azure (v1.3.0) 8.1)
Ensure that the expiration date is set on all secrets (CIS Azure (v1.3.0) 8.2)
Refer to our documentation for more information.
2021.05.13¶
Current Rule Results Report¶
Fugue has added a Current Rule Results Report. It is based on the Current Rule Violations Report and it supports the filtering and searching of violation data based on tags. Additionally, you can schedule this report to be sent to an AWS S3 Bucket. Refer to Current Rule Results for more information.
General Availability: AWS Resource Types¶
22 additional AWS resource types are now generally available:
AWS.EC2.Image (aws_ami)
AWS.WAFRegional.GeoMatchSet (aws_wafregional_geo_match_set)
AWS.WAFRegional.RateBasedRule (aws_wafregional_rate_based_rule)
AWS.WAFRegional.RegexMatchSet (aws_wafregional_regex_match_set)
AWS.WAFRegional.RegexPatternSet (aws_wafregional_regex_pattern_set)
AWS.WAFRegional.Rule (aws_wafregional_rule)
AWS.WAFRegional.RuleGroup (aws_wafregional_rule_group)
AWS.WAFRegional.SQLInjectionMatchSet (aws_wafregional_sql_injection_match_set)
AWS.WAFRegional.SizeConstraintSet (aws_wafregional_size_constraint_set)
AWS.WAFRegional.WebACL (aws_wafregional_web_acl)
AWS.WAFRegional.XSSMatchSet (aws_wafregional_xss_match_set)
AWS.WAFv2.LoggingConfiguration (aws_wafv2_logging_configuration)
AWS.WAFv2.RegexPatternSet (aws_wafv2_regex_pattern_set)
AWS.WAFv2.RuleGroup (aws_wafv2_rule_group)
AWS.WAFv2.WebACL (aws_wafv2_web_acl)
AWS.WAFv2.WebACLAssociation (aws_wafv2_web_acl_association)
AWS.WAFv2.LoggingConfiguration (aws_wafv2_logging_configuration)
AWS.WAFv2.RegexPatternSet (aws_wafv2_regex_pattern_set)
AWS.WAFv2.RuleGroup (aws_wafv2_rule_group)
AWS.WAFv2.WebACL (aws_wafv2_web_acl)
AWS.WAFv2.WebACLAssociation (aws_wafv2_web_acl_association)
CIS Azure Foundations Benchmark v1.3.0 (limited beta)¶
Fugue added support for CIS Azure Foundations Benchmark version 1.3.0, the latest version of the benchmark. This is in limited beta, so please contact support@fugue.co for access and refer to our documentation for more information.
User Experience Improvements: Hyperlinks to the Rules Page and Saving Search Terms/Filters¶
Rules on the Compliance by Resource and Waivers pages are hyperlinked to the Rules page for more details.
Search terms and filters on both the Rules and Waivers pages can be saved and shared via URL.
2021.04.29¶
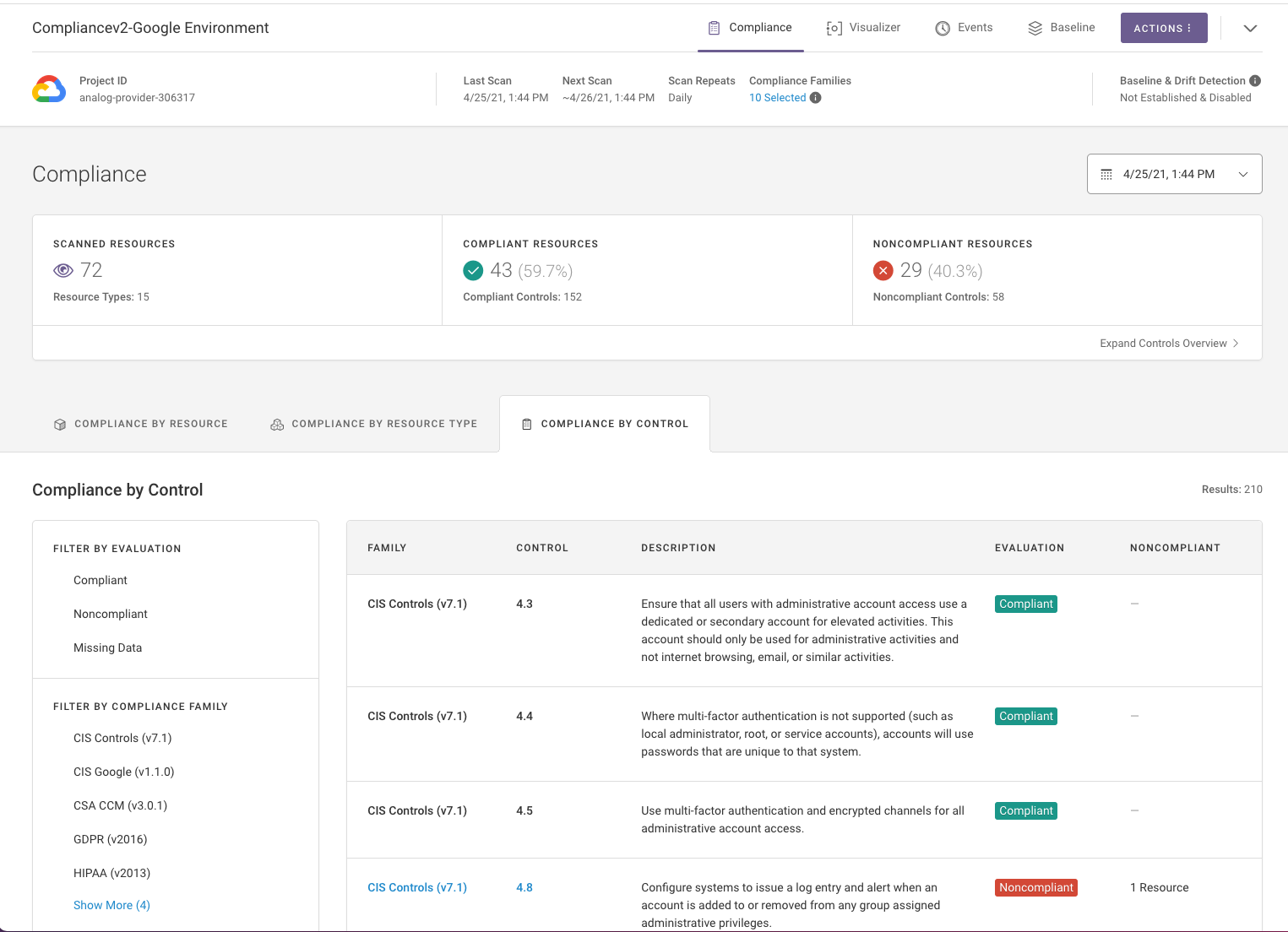
General Availability: Google Cloud¶
Fugue added support for Google Cloud to its multi-cloud security platform. Fugue support for Google Cloud initially includes 59 resource types and audit, reporting capabilities for the CIS Google (v1.1.0), CIS Controls (v7.1), CSA CCM (v3.0.1), GDPR (v2016), HIPAA (v2013), ISO 27001(v2013), NIST 800-53 (vRev4), PCI DSS (v3.2.1), SOC 2 (v2017), and custom enterprise policies.
New RBAC Policy: Manager¶
Fugue added a new RBAC policy, Manager, which grants all the permissions of the Contributor policy with the addition of deleting environments. For more information on working with RBAC, refer to Role-Based Access Control (RBAC).
Rules Page Improvements¶
Fugue made the following improvements to the Rules page:
All users with at least Read permissions can view the Rules page.
The Rules page has a new column, rule ID, and users can search by it.
Controls are grouped by Compliance Family.
Waivers Page Improvements¶
Fugue made the following improvements to the Waivers page:
All users with at least Read permissions can view the Waivers page.
You can search by the environment name (i.e., environment_name:CIS Controls - All Regions).
The Waivers table has two new columns: Rule ID and Resource Name/ID.
Compliance Page Improvements¶
Fugue made the following improvements to the Compliance pages:
Users can copy the resource ID/name from the Compliance by Resources page.
The Compliance by Resources table has a new column: Rule ID.
The Compliance by Control table has a new column: Family.
Bug Fixes¶
We resolved a bug where AMIs would not load in the visualizer due to an AWS API Gateway Limit. The load time subsequently improved by 50% or more for larger environments.
FG_R00288 Azure: Fugue updated the “Active Directory custom subscription owner roles should not be created” rule to not flag Azure built-in roles as non-compliant.
2021.04.15¶
Search Capabilities on the Waivers Page¶
You can search for a waiver by name, rule ID, resource provider (i.e., AWS, Azure, or Google), resource type, and waiver ID.
Compliance Pages Improvements to Display Resource Name & ID¶
The Compliance pages were updated to include the resource name and resource ID, when available.
Scan Google Cloud Project Without Enabling Compute Engine API¶
The Compute Engine API no longer has to be enabled for Fugue to scan a Google Cloud project.
Please contact support@fugue.co to enable Google Cloud support for your organization and refer to our documentation for more information.
Fugue Rule Improvements¶
FG_R00010 AWS: Fugue updated the “CloudFront distribution origin should be set to S3 or origin protocol policy should be set to https-only” rule to support evaluating Virtual Hosting S3 buckets.
2021.04.01¶
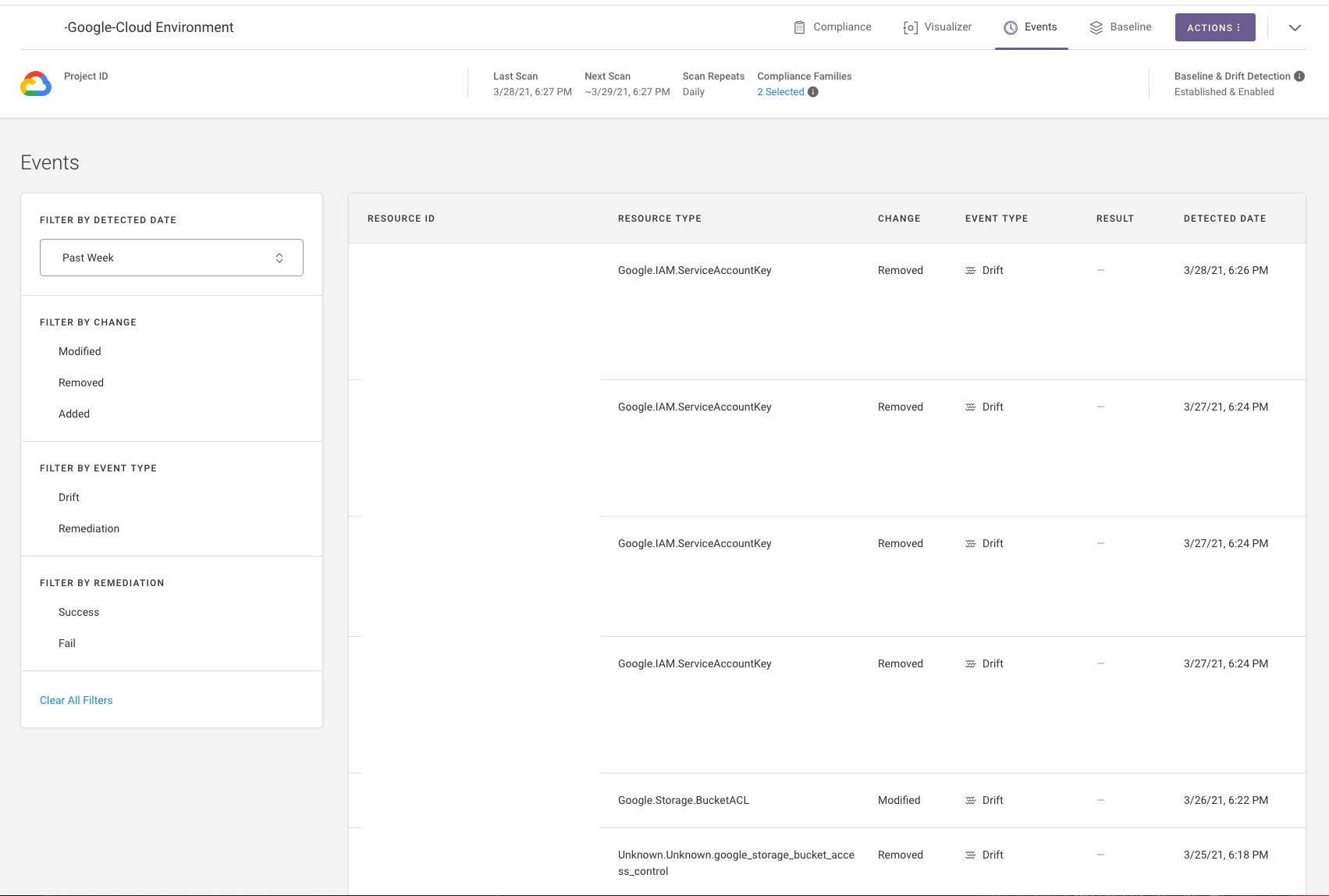
Google Cloud Enhancements (limited beta)¶
Fugue added the following enhancements for Google Cloud:
Added support for drift detection
Added links to the Google remediation steps on the Rules page
Updated abbreviations for Google resources in the Visualizer
Fixed missing Google provider options in the Fugue API’s Swagger definition for the Update Environment request
Please contact support@fugue.co to enable Google support for your organization and refer to our documentation for more information.
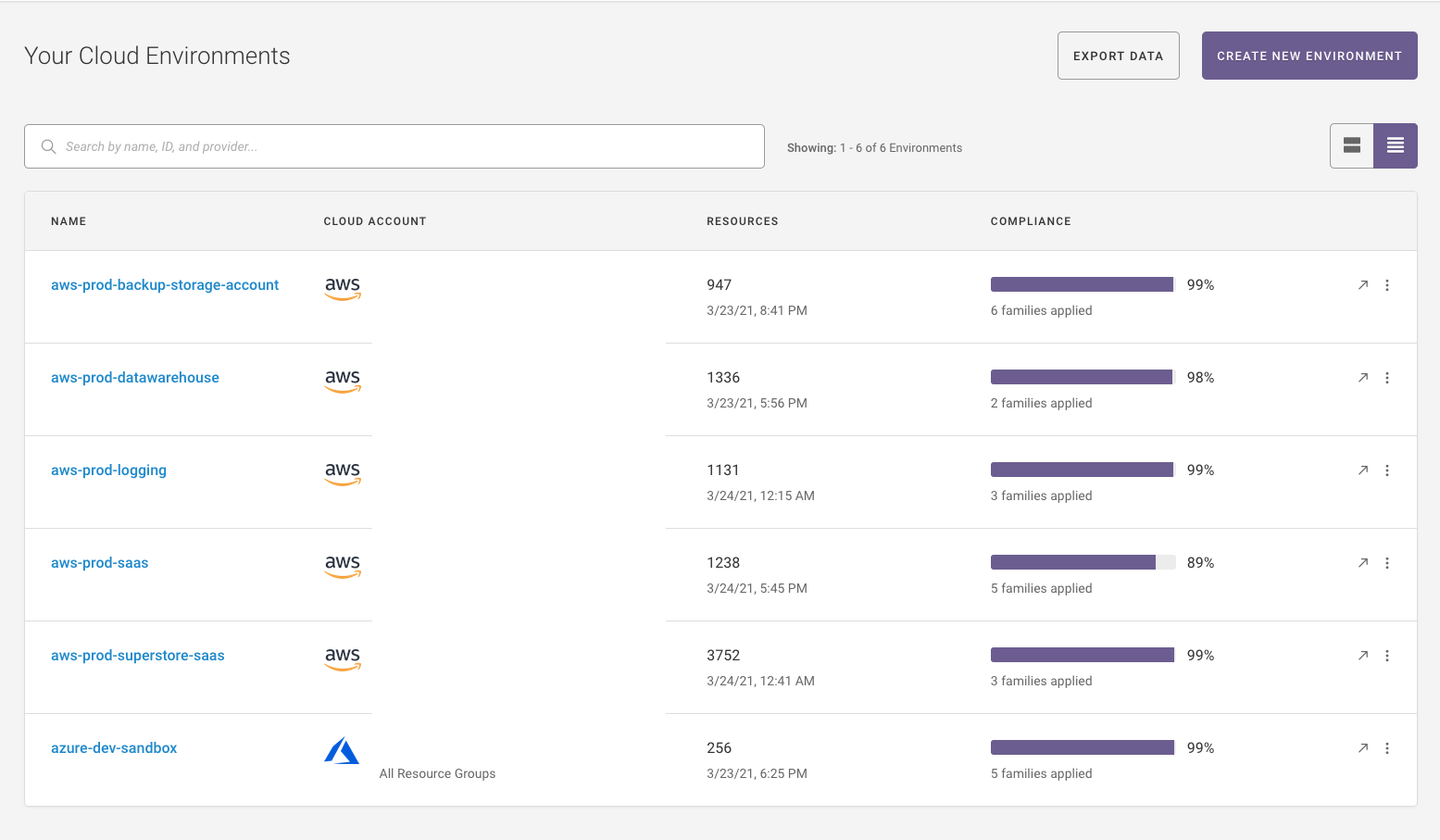
New Default View for the Environment Summary Page¶
The condensed view displays by default on the Environment Summary page, which makes it easier to scan and find a specific environment.
Regula Improvements¶
Regula can now process multiple IaC files (CloudFormation templates, Terraform plan files, and Terraform HCL directories) in a single test run and combines all results into one report. Regula report output has also been reorganized and updated to provide more information on rule results, accommodate multiple files and IaC platforms, and provide additional summary metrics. Rule severity and rule result values now match the values used in the Fugue API for easier reuse of scripts and reporting across both IaC and runtime resources.
Fugue Terraform Provider Updates¶
Version 0.0.5 of the Fugue Terraform Provider was published to the Terraform Registry. This updates the provider to support managing Azure and Google environments in Fugue. Existing Fugue environments may also now be imported into Terraform using the “terraform import” command.
2021.03.18¶
Support for Google Cloud (limited beta)¶
Fugue now supports Google Cloud resources across most major feature areas and interfaces (Visualizer, API, etc.) in limited beta. Drift detection is not yet available and will be added in a subsequent release. Please contact support@fugue.co for access and refer to our documentation for more information.
Additional Compliance Family Dashboards¶
Fugue now supports Compliance Family Dashboards for the following families:
CIS AWS (v1.3.0)
CIS Controls (v7.1)
CIS Docker (v1.2.0)
CIS Google (v1.1.0) Dashboard: Beta
CSA CCM (v3.0.1)
GDPR (v2016)
HIPAA (v2013)
ISO 27001 (v2013)
NIST 800-53 (vRev4)
Refer to the documentation for additional information.
Audit Log Support via the API¶
Fugue now supports access to an audit log via the API. Fugue currently logs all write actions (e.g., environment creation/modification, scans, creating/modifying waivers) that are taken within the Fugue web UI and by API clients. Audit log events are logged within 15 minutes of the action occurring. For more information, see the API Reference and API Request Examples.
Improvements to the Environment Summary Page¶
You can toggle between a collapsed and expanded environment view on the Environment Summary page. If you have a lot of environments, the condensed view makes it easier to scan and find a specific environment.
Regula Support for AWS CloudFormation¶
Fugue is the primary sponsor of Regula, an open source project for validating infrastructure-as-code built on Rego/Open Policy Agent policies. Regula now supports AWS CloudFormation, including SAM templates, and is now also available in a Docker container. Any custom rules written for Regula can also be applied as custom rules in the Fugue SaaS platform for runtime checks. If you would like more information, please reach out to support@fugue.co or check out the Regula README.
Bug Fixes & Misc. Improvements¶
Resolved an issue where waivers display for deleted environments.
Renamed rule_waiver to rule-waiver in the CLI.
Added Waiver support in the Fugue Terraform Provider.
2021.03.04¶
Visualizer: Support for Filtering by Regions, Tags, and Services¶
Visualizer now supports filtering by region, tags, or services. Filtered views can be exported. Filter options are populated on the first scan after the release. If filters aren’t available, run one scan and then visit the Visualizer again to see the filter options. Refer to the online user guide for additional information.
Rule Update¶
Rule “S3 bucket policies and ACLs should not be configured for public read access” (rule ID: FG_R00279) is now sensitive to additional permissions when determining whether an S3 bucket allows “public read access.” This effectively makes the rule more sensitive to potential misconfigurations in S3 bucket ACLs. Refer to the online user guide for additional information.
2021.02.18¶
Six New Rules for AWS CIS Foundations Benchmark 1.3.0¶
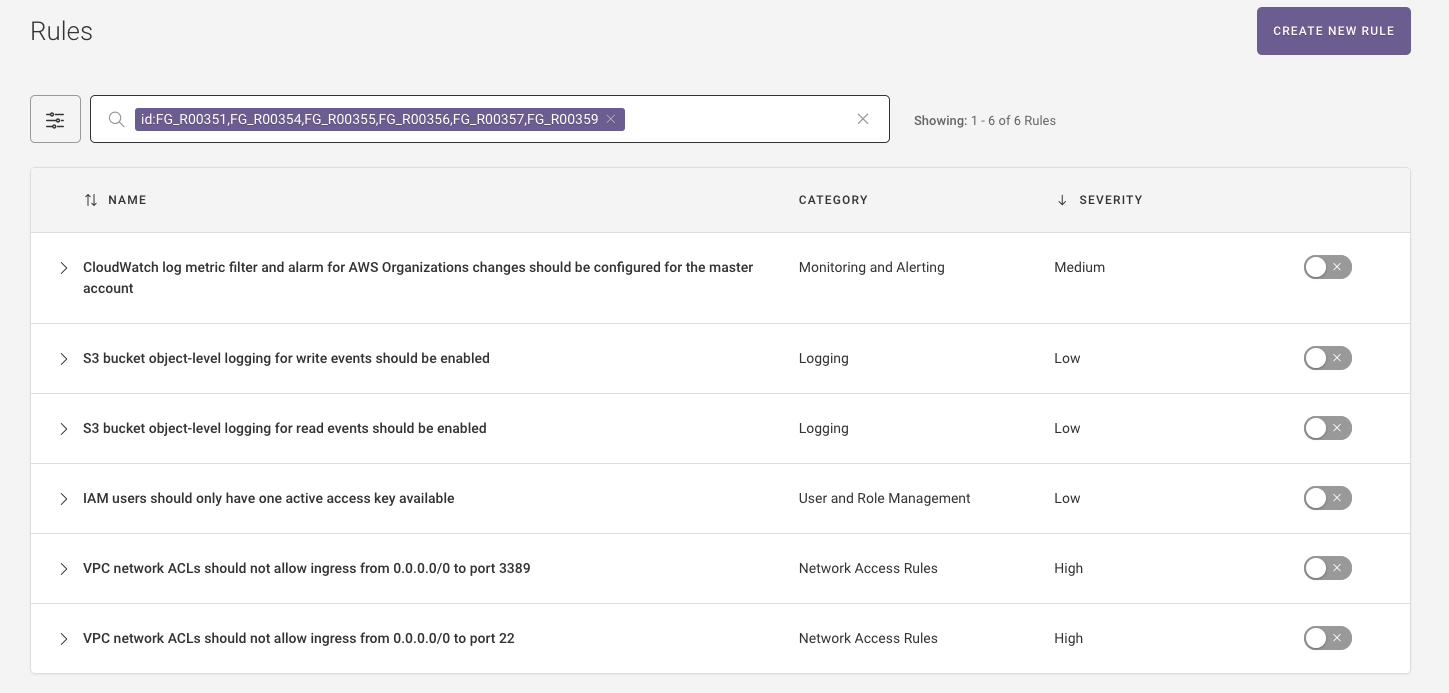
Fugue added 6 new rules for the AWS CIS Foundations Benchmark 1.3.0:
S3 bucket object-level logging for write events should be enabled
S3 bucket object-level logging for read events should be enabled
VPC network ACLs should not allow ingress from 0.0.0.0/0 to TCP/UDP port 22
VPC network ACLs should not allow ingress from 0.0.0.0/0 to TCP/UDP port 3389
These rules are disabled by default. To enable them, navigate to the Rules page to turn on the new rules then add the new CIS AWS v.1.3.0 compliance family to the settings for each applicable environment. Refer to the online documentation for more information.
Tip
To find the newly added rules, navigate to the Rules page and enter the following in the search: id:FG_R00351,FG_R00354,FG_R00355,FG_R00356,FG_R00357,FG_R00359.
Additionally, Fugue expanded the rule (FG_R00066) “Load balancer access logging should be enabled” to check both ELBv1 and ELBv2 load balancers.
Expanded Azure Service Coverage¶
Fugue expanded Azure service coverage support to include:
Azure.ActiveDirectory.Application
Azure.ActiveDirectory.Group
Azure.ActiveDirectory.ServicePrincipal
Azure.ActiveDirectory.User
These resources are marked as beta so please contact support@fugue.co if you would wish to access them. Refer to the online documentation for more information.
Waiver Support in the API and CLI¶
The Fugue API now supports actions for waiving rules, including:
Listing all rule waivers
Creating a new rule waiver
Retrieving details and rule metadata for a rule waiver
Updating a rule waiver
Deleting a rule waiver
Refer to the API Examples and API Reference for more information.
CLI: Additional Filter Support on the Environments API Endpoint¶
The Fugue CLI now supports additional filters for the /list endpoint, including:
Ability to filter by
--id,--arn, and--statusAbility to search across all environments by name, id, and provider using
--search
Refer to the online documentation for more information.
2021.02.04¶
SSO: Okta Tile Support¶
Users can log into the Fugue application using an Okta tile. Previously, SSO enabled organizations would need to navigate to https://riskmanager.fugue.co/login to log into the application, which is not a natural workflow for organizations with SSO enabled. Refer to the online documentation for more information.
CIS Docker 1.2.0 & CIS AWS 1.3.0 Compliance Families¶
Fugue added support for CIS AWS Foundations Benchmark 1.3.0 and CIS Docker Benchmark 1.2.0. CIS AWS Foundations Benchmark 1.3 is the latest version of the benchmark. The CIS Docker Benchmark provides guidance on secure configurations for developing and deploying Docker containers on Linux based platforms.
Expanded AWS and Azure Service Coverage: Beta¶
Fugue expanded AWS and Azure service coverage support to include:
AWS.WAF.ByteMatchSet
AWS.WAF.GeoMatchSet
AWS.WAF.RateBasedRule
AWS.WAF.RegexMatchSet
AWS.WAF.RegexPatternSet
AWS.WAF.Rule
AWS.WAF.RuleGroup
AWS.WAF.SQLInjectionMatchSet
AWS.WAF.SizeConstraintSet
AWS.WAF.XSSMatchSet
AWS.WAFRegional.ByteMatchSet
AWS.WAFRegional.GeoMatchSet
AWS.WAFRegional.RateBasedRule
AWS.WAFRegional.RegexMatchSet
AWS.WAFRegional.RegexPatternSet
AWS.WAFRegional.Rule
AWS.WAFRegional.RuleGroup
AWS.WAFRegional.SQLInjectionMatchSet
AWS.WAFRegional.SizeConstraintSet
AWS.WAFRegional.WebACL
AWS.WAFRegional.XSSMatchSet
AWS.WAFv2.LoggingConfiguration
AWS.WAFv2.RegexPatternSet
AWS.WAFv2.RuleGroup
AWS.WAFv2.WebACL
AWS.WAFv2.WebACLAssociation
Azure.Authorization.RoleAssignment
Azure.ManagedIdentity.Identity
If you are interested in gaining access to the beta AWS and Azure resources, please reach out to support@fugue.co. Once you gain access to the AWS beta resources, you will need to update your IAM role.
API Updates: Environment Queries¶
The /environments API endpoint now supports querying environments by AWS account ID, AWS ARN, and Azure subscription ID. Refer to the online documentation for additional information.
CLI Support for Users and Groups¶
The Fugue CLI now supports actions for managing users and groups, including:
Inviting users
Creating groups
Editing user group assignments
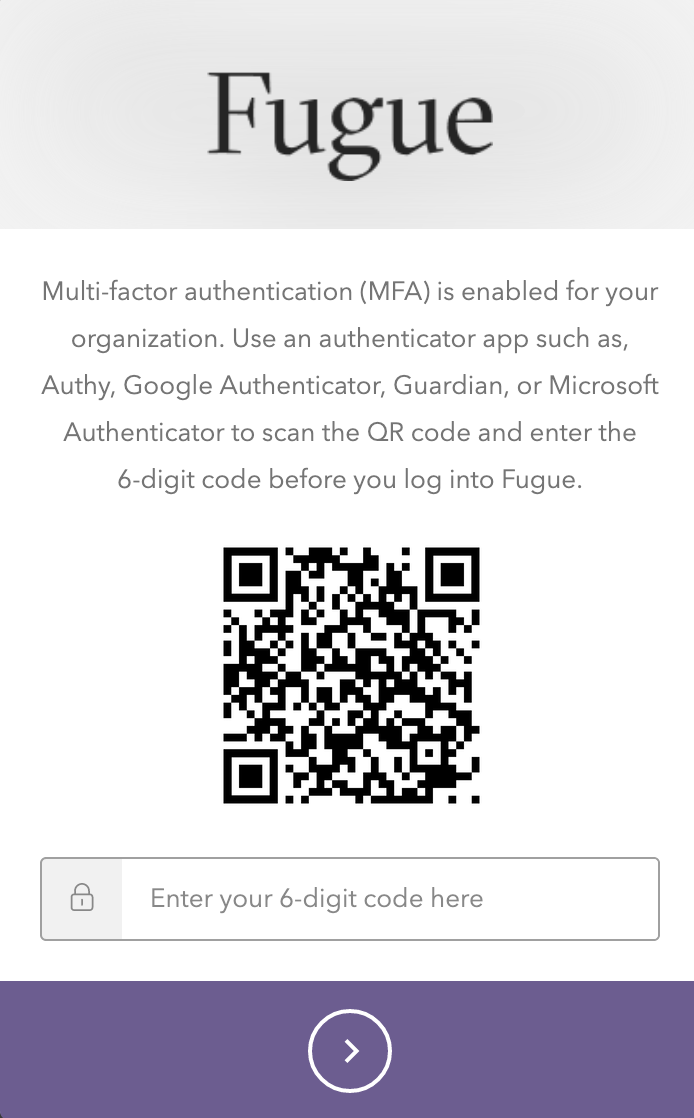
UX Improvements to the MFA Authentication Screen¶
The MFA authentication screen displays a “friendly” name instead of an auto generated name.
2021.01.21¶
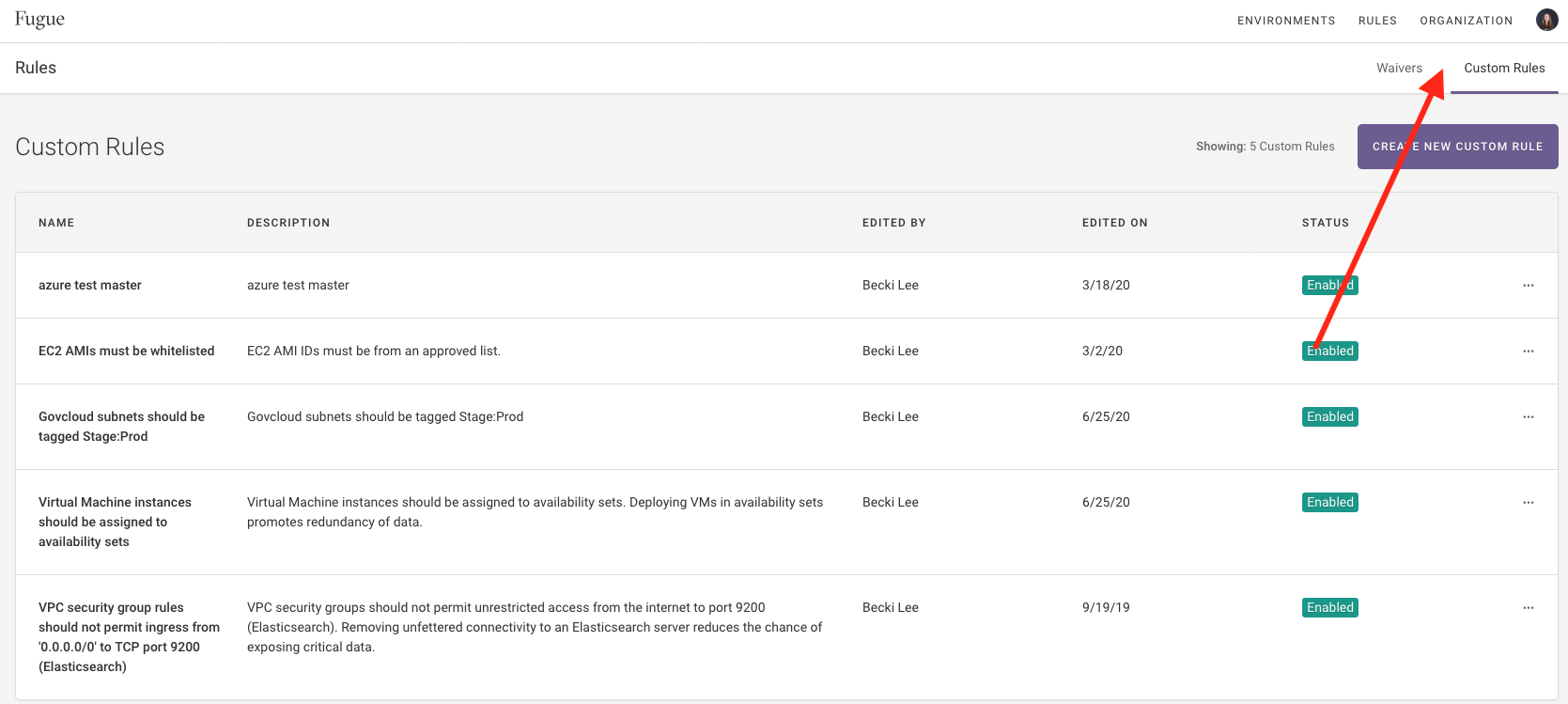
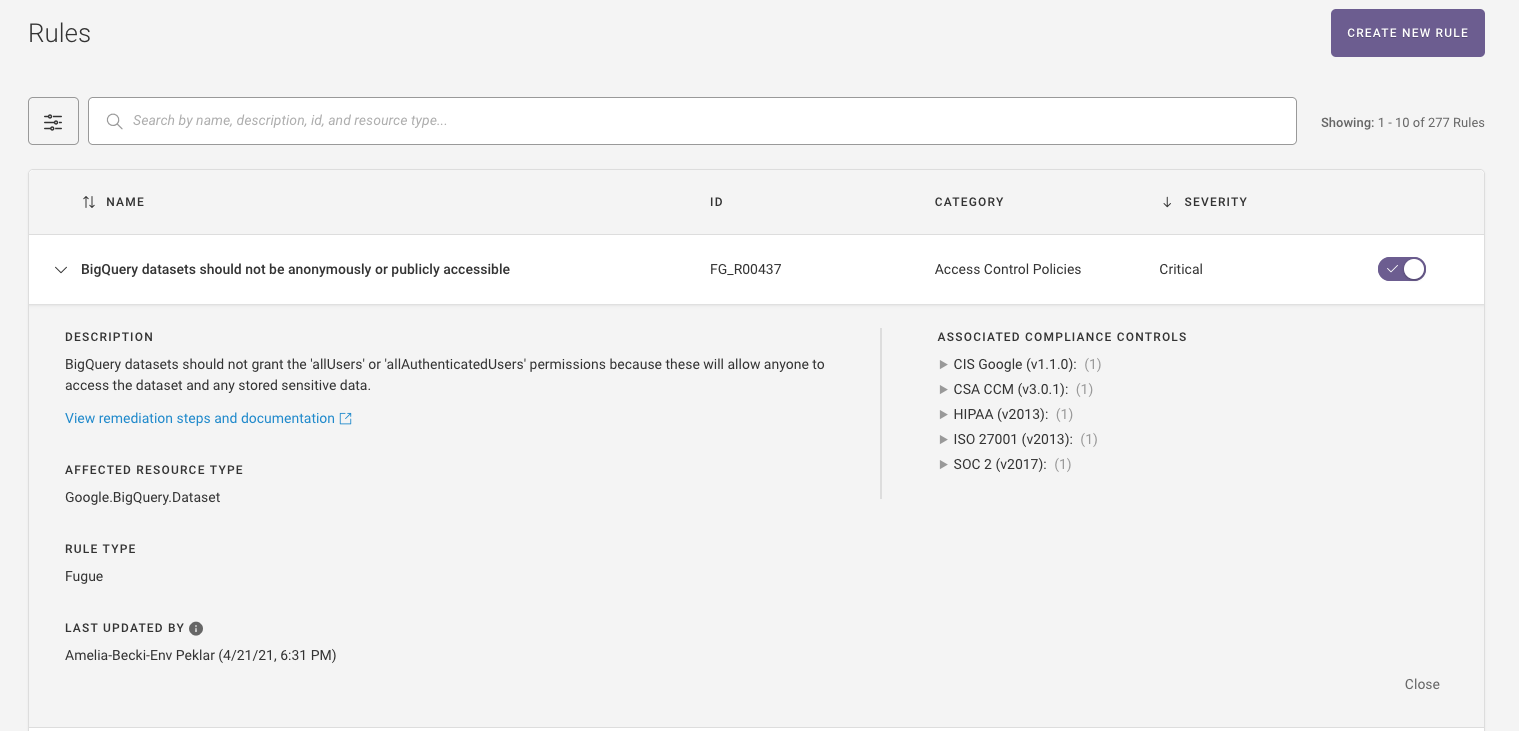
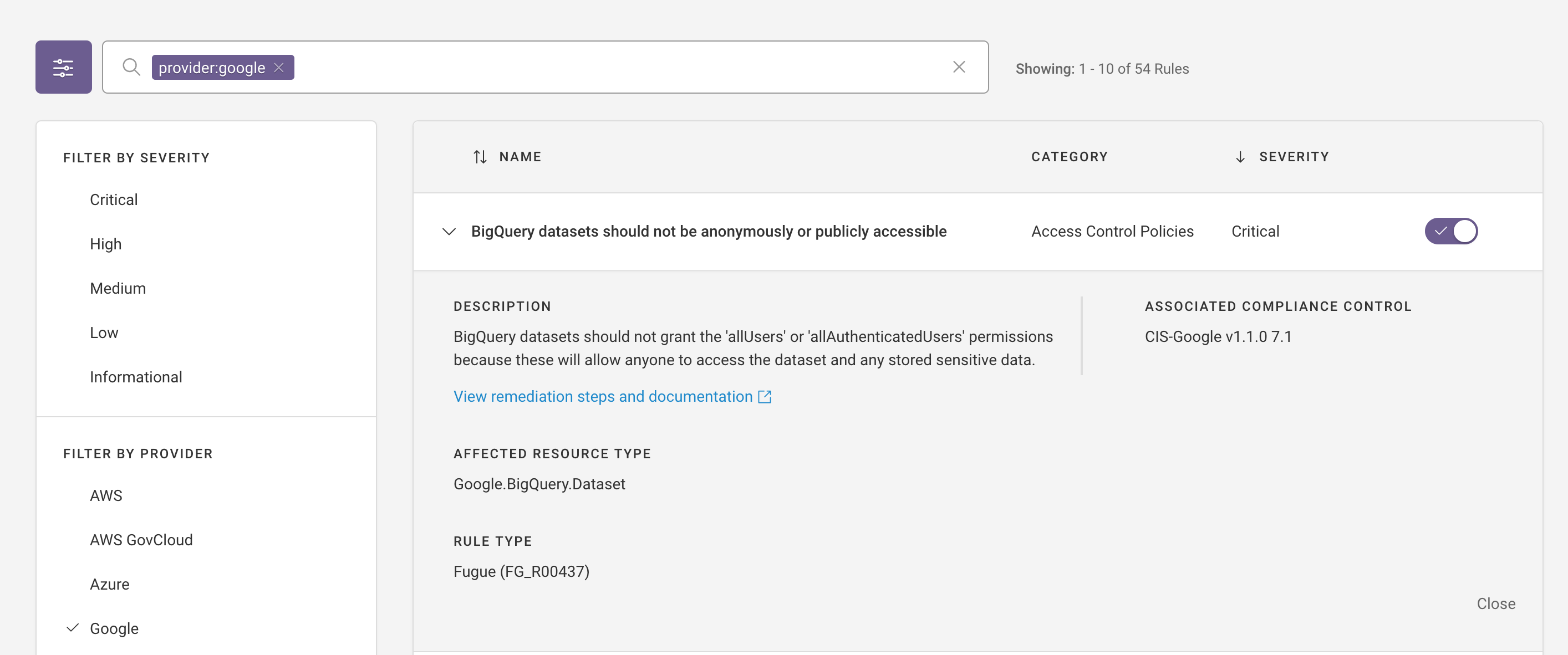
New Rules Page¶
Fugue now supports a new Rules page for viewing/configuring which rules are enabled for an organization (more on this later), and adding/modifying custom rules.
Refer to the online documentation for more information.
On the Rules page, you can view the details about a rule including: rule description, affected resource type, rule type (Fugue or Custom), associated compliance controls, and more.
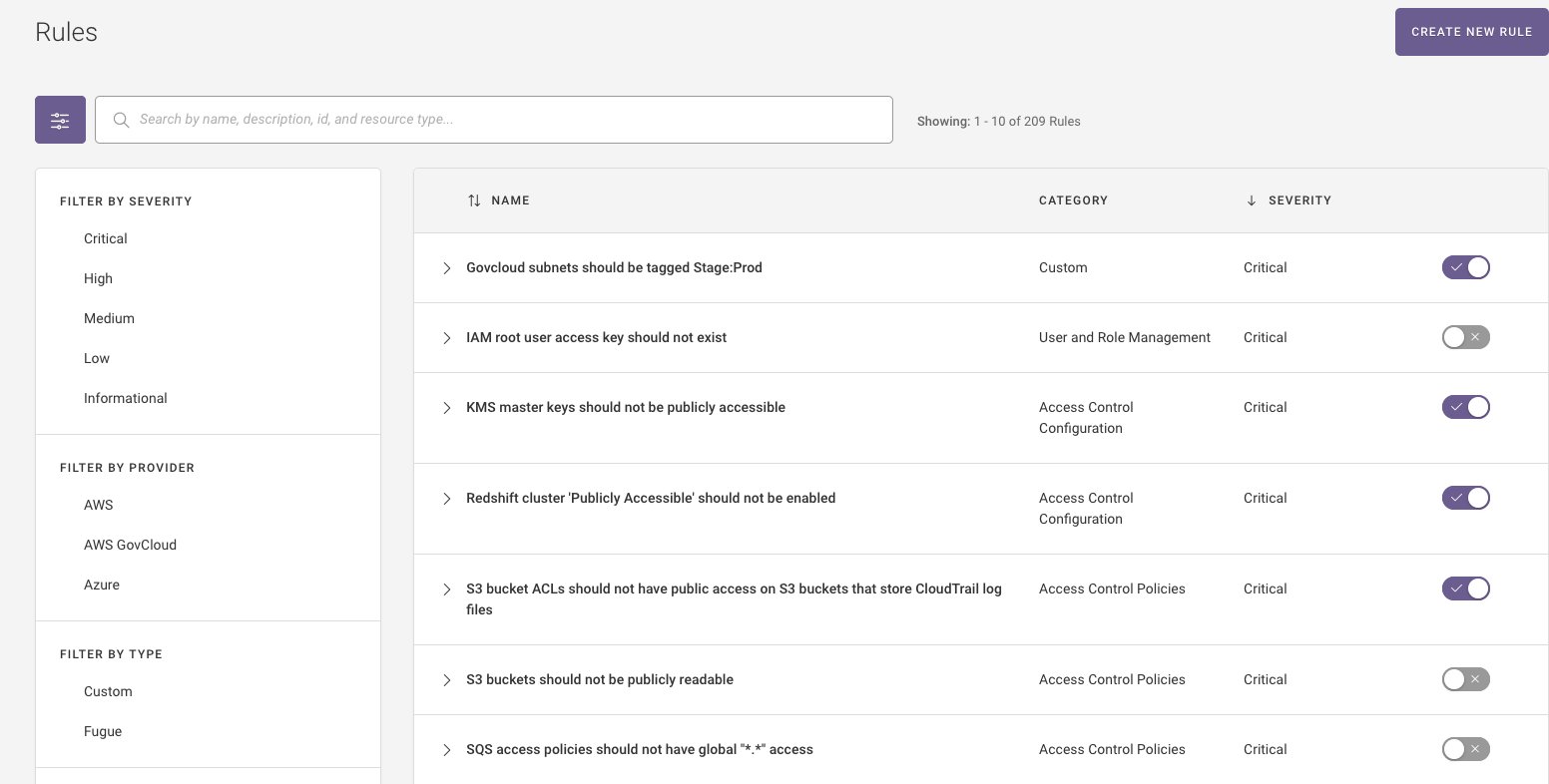
Enable/Disable Rules for your Organization¶
Fugue has added support for enabling/disabling rules for an organization. This works in conjunction with Fugue’s rule waivers features, which applies to specific resources/all resources within an environment. Once a rule is enabled/disabled in the UI, the rule will no longer apply to your organization’s environments on the next scan.
API Support for Users and Groups¶
The Fugue API now supports actions for managing users and groups, including:
Inviting users
Creating groups
Editing user group assignments
Refer to the API Examples and API Reference for more information.
Visualizer: Expanded AWS Service Coverage¶
Fugue expanded AWS service coverage support for visualizer to include:
ACM.Certificate (ACM)
ApiGateway.ClientCertificate (only shown as label)
ApiGateway.Deployment (only shown as label)
ApiGateway.RequestValidator (only shown as label)
ApiGateway.Resource (only shown as label)
ApiGateway.Stage (only shown as label)
ApiGateway.UsagePlan (only shown as label)
Cloud.Trail (TRAIL)
IAM.User (USER)
KMS.Key (KEY)
EC2.RouteTable (only shown as label)
WAF.WebACL (WAF)
Updated Fugue Rules¶
Fugue made improvements to the following Fugue rules:
CloudTrail trails should not be associated with missing SNS topics.
This rule was updated to support looking at AWS SNS topic by name or ARN.
IAM roles attached to instance profiles should not allow broad list actions on S3 buckets.
This rule was updated to filter policies where resources= * to be more targeted in calling policies non-compliant. This update applies to environments in AWS GovCloud only.
IAM policies should not allow broad list actions on S3 buckets.
Ensure a support role has been created to manage incidents with AWS Support.
These two rules were updated to no longer evaluate AWS ARN prefixes as some GovCloud resources use the cloud partition aws-us-gov.
2021.01.05¶
Enable or Disable a Rule for Your Entire Organization: Beta¶
Fugue added support to disable or enable a rule for your entire organization. On the subsequent scan, the enabled or disabled rule is no longer applied to your environment.
On the Rules page, you can view the details about a rule including: rule description, affected resource type, rule type (Fugue or Custom), associated compliance controls, and more.
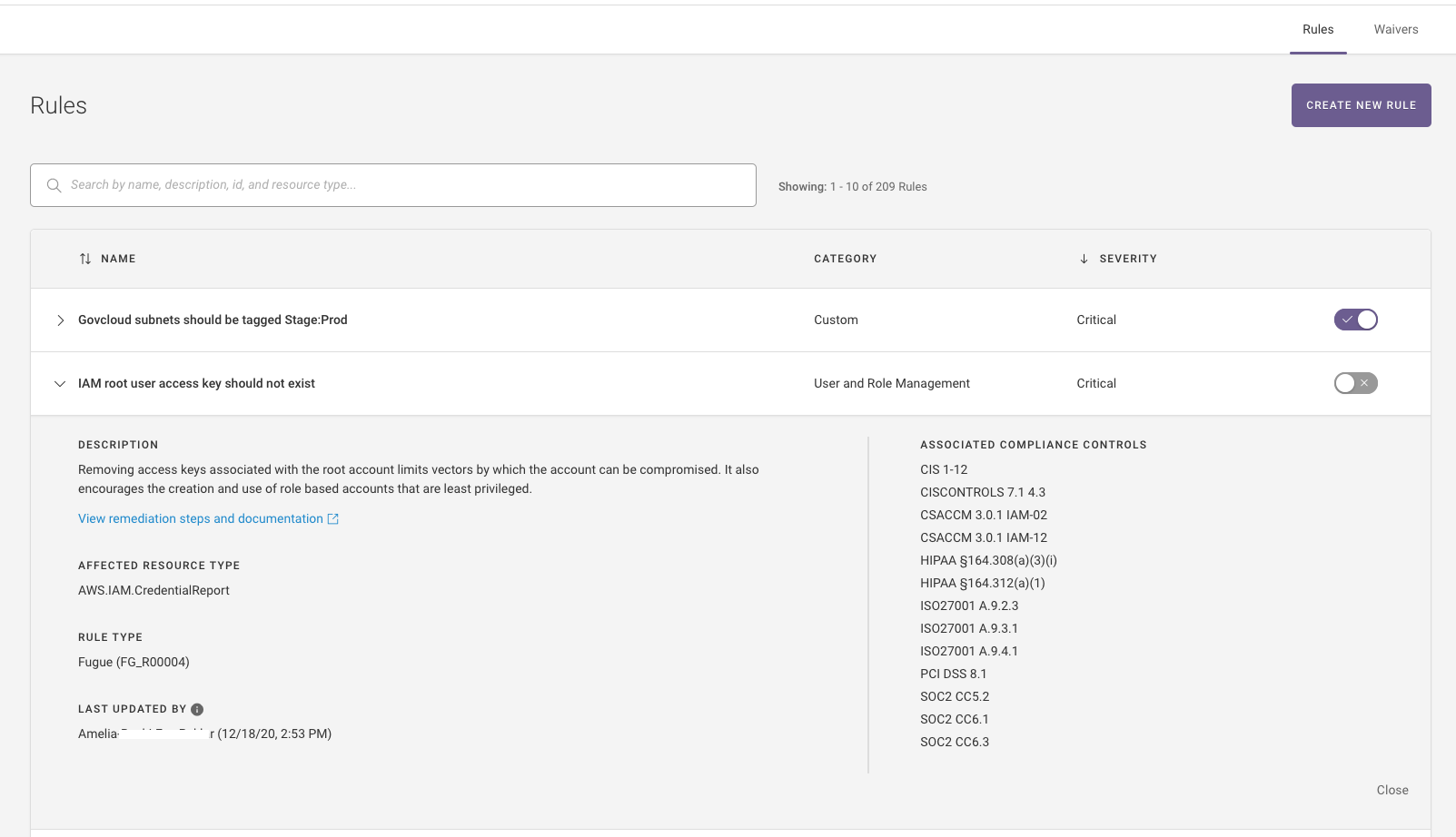
If you are interested in gaining access to the beta enable/disable rules, please reach out to support@fugue.co. Refer to Enabling and Disabling Rules for more information.
Improvements to Visualizer¶
Fugue enhanced filtering/searching capabilities on the visualizer to support regions. Default AWS VPCs, regions, and Azure VNETs are collapsed by default upon initial load making it easier to find information. Refer to Visualizer for additional information.
2020.12.09¶
Reporting Updates¶
Reports and Dashboards are now generally available! Refer to Reports & Dashboards for more information.
Fugue added support for a “Resources Report,” which generates a tabular representation of all of your resources, with corresponding compliance evaluations and rule results. This provides additional visibility into your cloud resource inventory and compliance.

Fugue added the following filters to the “Current Rule Violations” report: resource type, account ID, and compliance family.
Rules Updates¶
Fugue added 5 rules that validate whether AWS resources are utilizing TLS protocol versions 1.2 and above. These new rules map to the CSA Cloud Controls Matrix (v3.0.1) and SOC 2 (2017 Trust Services Criteria).
CloudFront distribution viewer certificate should use secure TLS protocol versions (1.2 and above)
CloudFront distribution custom origins should use secure TLS protocol versions (1.2 and above)
ELB HTTPS listeners should use secure TLS protocol versions (1.2 and above)
ELBv2 HTTPS listeners should use secure TLS protocol versions (1.2 and above)
API Gateway classic custom domains should use secure TLS protocol versions (1.2 and above)
Rules that inspect IAM user settings (e.g., MFA) now generate rule violations on AWS.IAM.User resources, instead of AWS.IAM.CredentialReport
Rules that check for the existence of something (e.g., whether a support role has been created to manage AWS Support incidents) no longer generate extraneous “passing” rule results. This will not impact your compliance posture.
Azure Subscription Onboarding¶
Fugue now automatically adds all Azure resource groups to an environment for a given subscription when all resource groups are selected. Previously, new resource groups had to be added manually via the API. Refer to Setup - Azure & Azure Government for additional information.
Expanded Service Coverage: Azure¶
Fugue expanded Azure service coverage for compliance and drift for the following resource types:
Azure.ApplicationInsights.Component
Azure.Authorization.PolicyAssignment
Azure.Authorization.RoleDefinition
Azure.Cdn.Endpoint
Azure.CosmosDB.Account
Azure.DataLakeAnalytics.Account
Azure.DataLakeAnalytics.FirewallRule
Azure.DataLakeStore.Account
Azure.DataLakeStore.FirewallRule
Azure.KeyVault.Certificate
Azure.KeyVault.Key
Azure.KeyVault.Secret
Azure.Kubernetes.Cluster
Azure.Monitor.ActionGroup
Azure.Monitor.ActivityLogAlert
Azure.Monitor.DiagnosticSetting
Azure.Monitor.LogProfile
Azure.Monitor.MetricAlert
Azure.MySQL.ConfigurationSet
Azure.Network.LoadBalancerNatRule
Azure.Network.LoadBalancerProbe
Azure.Network.LoadBalancerRule
Azure.Network.NetworkWatcherFlowLog
Azure.PostgreSQL.ConfigurationSet
Azure.Redis.Cache
Azure.Redis.FirewallRule
Azure.SecurityCenter.Contact
Azure.SecurityCenter.SubscriptionPricing
Azure.Web.AppService
Azure.Web.AppServicePlan
Azure.Web.FunctionApp
Refer to Service Coverage - Azure & Azure Government for additional information.
API Updates: Events¶
The /events API endpoint now supports relative time offsets; for example, to retrieve events between one and two hours ago, set range_from to -7200 and range_to to -3600 (in seconds). Refer to the API Reference for additional information.
2020.12.01¶
Visualizer: Expanded AWS and Azure Service Coverage¶
Fugue expanded AWS service coverage support for the visualizer to include:
DirectoryService.Directory (DIR)
Kinesis.Stream (KNSIS)
SNS.Topic (SNS)
SQS.Queue (SQS)
Fugue expanded Azure service coverage support for the visualizer to include DataLakeStore.Account (DLAKE).
Bug Fixes¶
Fugue improved the speed to scan Azure environments.
2020.11.10¶
Added Advanced Reporting Capabilities - Beta¶
Fugue added a dedicated Reports section featuring advanced reporting and data analytics. You can access the following predefined reports and dashboards:
Compliance Posture Dashboard: Visualize information on rule violations by severity, service, environment, as well as resource compliance and control evaluations over time.
Current Rule Violations: View details in tabular format on outstanding rule violations and filter by severity, resource type, rule, and more.
Resources Dashboard: Visualize information on resource compliance by resource type, severity, and environment over time.
Compliance Family Dashboards: Visualize information on resource compliance by resource type, severity, and environment over time. This information is available in 4 specific compliance dashboards:
CIS AWS Foundations Benchmark Dashboard
CIS Azure Foundations Benchmark Dashboard
SOC 2 Dashboard
PCI-DSS Dashboard
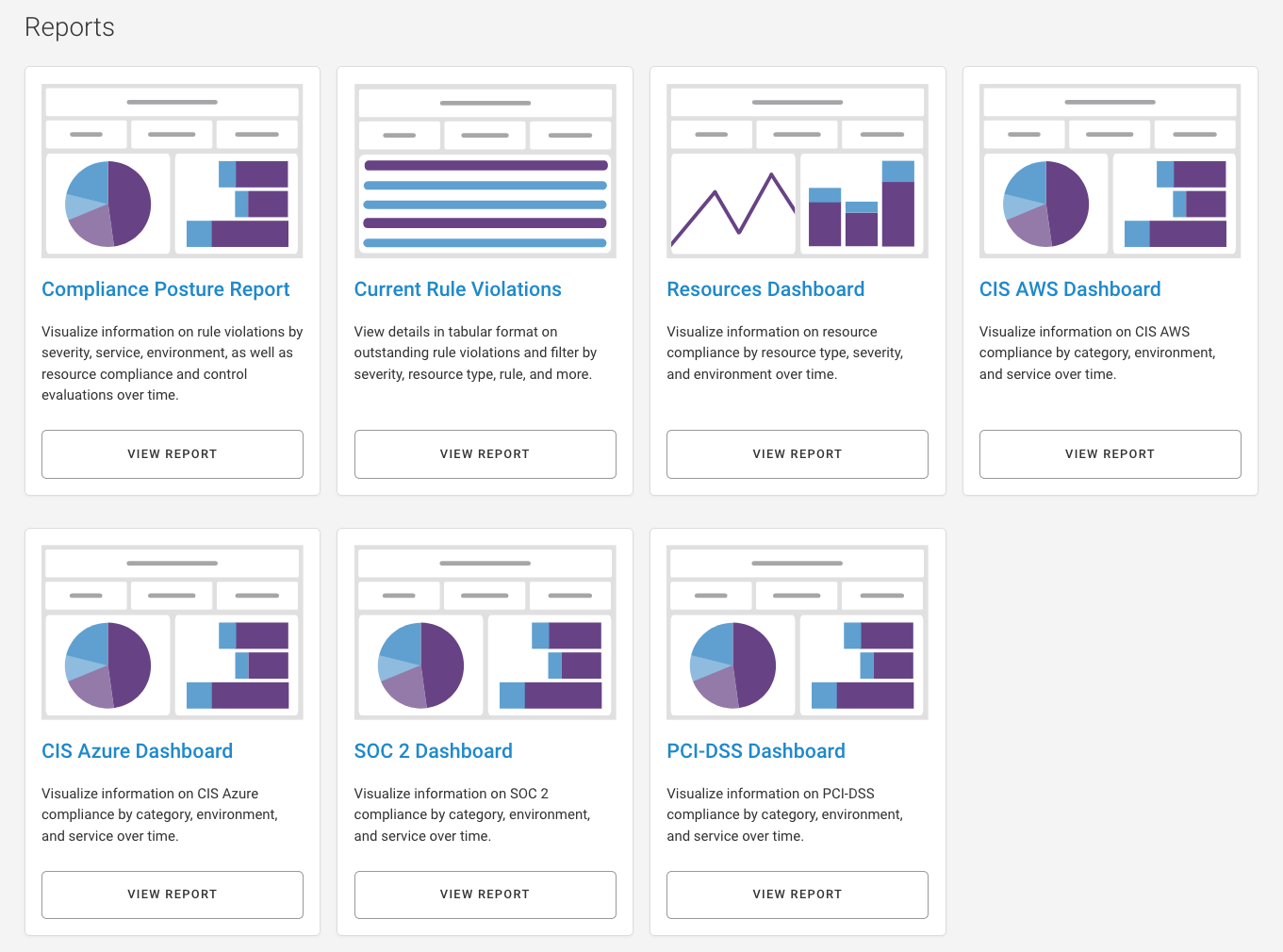
Selecting a dashboard or dashboard displays it with default values set for the filters. You have the following options:
Change the exposed filters of the report/dashboard
Download the report/dashboard as a PDF or set of XLSX/CSV files
Send an email with the report/dashboard to one or more recipients
Schedule an email with the report/dashboard for one or more recipients
Configure email alerts when a metric breaches a specified threshold
Drill into a report for further investigation
Refer to Report Dashboards (Beta) for more information.
Expanded Default Compliance Standard Library- CSA CCM¶
Fugue added support for the Cloud Security Alliance Cloud Controls Matrix (CSA CCM) compliance family. CSA CCM is a framework that provides security professionals with guidance in assessing their overall security risks in the cloud.
2020.10.27¶
UX Improvements to the Environment Overview Page¶
Fugue added support to trigger a scan from the Environment Overview page. Previously, you would need to click into environment-specific pages to trigger a scan.
The entire “environment card” on the Environment Overview page is clickable to environment-specific pages.
UX Improvements to Tables¶
Fugue added the capability to sort on the Users, Groups, API Clients, Notifications, Waivers, and Custom Rules tables.
Fugue added configurable row count in the tables throughout the user interface. These changes apply to the tables on the Compliance, Events, Baseline, Users, Groups, API Clients, Notifications, Waivers, and Custom Rules pages.
Fugue added pagination to the Baseline, Users, Groups, API Clients, Notifications, Waivers, and Custom Rules tables.
Expanded Azure Service Coverage - Beta¶
Fugue expanded service coverage for Azure and it includes 11 new Azure resources:
Azure.Cdn.Endpoint
Azure.CosmosDB.Account
Azure.DataLakeAnalytics.Account
Azure.DataLakeAnalytics.FirewallRule
Azure.DataLakeStore.Account
Azure.DataLakeStore.FirewallRule
Azure.Network.LoadBalancerNatRule
Azure.Network.LoadBalancerProbe
Azure.Network.LoadBalancerRule
Azure.Redis.Cache
Azure.Redis.FirewallRule
If you are interested in gaining access to the beta Azure resources, please reach out to support@fugue.co. Refer to Service Coverage - Azure & Azure Government for more information.
Visualizer - Azure Service Coverage¶
Fugue added service coverage support in the visualizer for the Azure resources in beta — Azure.CosmosDB.Account and Azure.Redis.Cache.
Bug Fixes¶
Fugue resolved an issue where users assigned to the Contributor role could not see the environments that they created.
2020.10.13¶
UX Improvements to the Environment Compliance Summary¶
Fugue made the Environment Compliance Summary collapsible and expandable, providing more screen real estate to review compliance results.
Additionally, the order of the compliance pages changed — Compliance by Resource and Compliance by Control pages switched places. The first page is Compliance by Resource and the last page is Compliance by Control.
Create a Waiver on a Missing Resource¶
Fugue added support to create a waiver on a missing resource. Refer to Waivers for additional information about waivers. Note, the environment needs a rescan before the missing resources display on the Compliance by Resource page.
Scheduled Report Improvements¶
Fugue values feedback from our customers and made updates to our reports based on your feedback. The updates include:
All reports:
Updated the chart colors to make them easier to read.
Compliance Posture and Resource Dashboards
Updated the charts to display percent of noncompliant resources instead of compliant resources
Compliance Family Dashboard
Added the percentages of noncompliant resources to the charts.
These reports are currently available by email upon request. Fugue is actively working on integrating these reports into the product. If you are interested in receiving these reports, please contact support@fugue.co. For more information about these reports, refer to Organization-Level Enterprise Compliance Reports.
Deprecated Support for TLS 1.0 and TLS 1.1¶
Fugue deprecated support for Transport Layer Security (TLS) versions 1.0 and 1.1 to align with industry best practices and data integrity. If you have any questions, please contact support@fugue.co.
2020.09.23¶
RBAC Improvements¶
Fugue added support for users to belong to multiple groups. Refer to the RBAC docs for more information.
Deprecating TLS 1.0 and TLS 1.1¶
In the next deployment, Fugue is deprecating support for Transport Layer Security (TLS) versions 1.0 and 1.1 to align with industry best practices and data integrity. If you have any questions, please contact support@fugue.co.
Enhancements to Scanning of S3 Resources¶
The v0.39.0 release (2020.09.23) contains two enhancements relating to the scanning of S3 resources. These changes mean Fugue is now able to report on the compliance of S3 resources that previously were not scanned by Fugue. This means some users will see changes in environment compliance and notifications regarding S3 resources.
More information on these two adjustments is as follows:
Prior to this change, Fugue used the S3
HeadBucketoperation to check for bucket existence and to see if Fugue had permission to read bucket metadata. We discovered that theHeadBucketoperation is sometimes blocked by bucket policies*, so moving forward Fugue will rely on other operations to check for bucket existence.The second change is that, previously, an error on one S3 resource would prevent subsequent S3 resources from being scanned in some cases. Moving forward, the scan is more resilient to these errors and the scan will continue for the remaining resources.
Together, these improvements mean Fugue will now see some S3 buckets, and sub-resources such as bucket policies, that previously were not captured in scans. For such resources, you should expect to receive drift notifications for “newly added” resources and compliance notifications for “newly non-compliant” for any noncompliant S3 resources that are now visible to Fugue.
Resource types affected by this change include:
AWS.S3.Bucket
AWS.S3.BucketInventory
AWS.S3.BucketMetric
AWS.S3.BucketNotification
AWS.S3.BucketPolicy
AWS.S3.BucketPublicAccessBlock
* The S3 HeadBucket operation actually requires s3:ListBucket permissions according to its AWS documentation.
Bug Fixes¶
Fugue resolved an issue where if you had a large environment (6 mb or greater), the rules/test/input API endpoint would timeout.
2020.09.09¶
New Azure Rules¶
As part of our commitment to continually updating rules associated with compliance families, we have created 35 additional Azure rules including:
SQL Server auditing retention should be greater than 90 days
Virtual Network security group flow log retention period should be set to 90 days or greater
Active Directory custom subscription owner roles should not be created
Security Center default policy setting ‘Monitor System Updates’ should be enabled
Security Center default policy setting ‘Monitor OS Vulnerabilities’ should be enabled
Security Center default policy setting ‘Monitor Endpoint Protection’ should be enabled
Security Center default policy setting ‘Monitor Disk Encryption’ should be enabled
Security Center default policy setting ‘Monitor Network Security Groups’ should be enabled
Security Center default policy setting ‘Monitor Web Application Firewall’ should be enabled
Security Center default policy setting ‘Monitor Vulnerability Assessment’ should be enabled
Security Center default policy setting “Monitor Storage Blob Encryption” should be enabled
Security Center default policy setting “Monitor JIT Network Access” should be enabled
Security Center default policy setting “Monitor Adaptive Application Whitelisting” should be enabled
Security Center default policy setting “Monitor SQL Auditing” should be enabled
Security Center default policy setting “Monitor SQL Encryption” should be enabled
PostgreSQL Database configuration ‘log_checkpoints’ should be on
PostgreSQL Database configuration ‘log_connections’ should be on
PostgreSQL Database configuration ‘log_disconnections’ should be on
PostgreSQL Database configuration ‘log_duration’ should be on
PostgreSQL Database configuration ‘connection_throttling’ should be on
PostgreSQL Database configuration ‘log_retention days’ should be greater than 3
Monitor ‘Activity Log Retention’ should be 365 days or greater
Monitor log profile should have activity logs for global services and all regions
App Service web apps should have ‘Minimum TLS Version’ set to ‘1.2’
App Service web apps should have ‘Incoming client certificates’ enabled
These rules will cause compliance event notifications. If you have any questions, please reach out to support@fugue.co.
Expanded Service Coverage for Azure - Beta¶
Fugue added beta support for:
Azure.Authorization.PolicyAssignment
Azure.Authorization.RoleDefinition
Azure.KeyVault.Certificate
Azure.KeyVault.Key
Azure.KeyVault.Secret
Azure.Kubernetes.Cluster
Azure.Monitor.DiagnosticSetting
Azure.Monitor.LogProfile
Azure.MySQL.ConfigurationSet
Azure.Network.NetworkWatcherFlowLog
Azure.PostgreSQL.ConfigurationSet
Azure.SecurityCenter.Contact
Azure.SecurityCenter.SubscriptionPricing
Azure.Web.AppService
Azure.Web.AppServicePlan
Azure.Web.FunctionApp
If you are interested in gaining access to the beta Azure resources, please reach out to support@fugue.co. Refer to Service Coverage - Azure & Azure Government for more information.
Expanded Service Coverage for AWS - Beta¶
Fugue added service coverage for AWS.EC2.Image. If you have a large number of AMIs, you may want to confirm whether you want to scan for this resource type because each AMI is considered to be one resource.
If you are interested in gaining access to the beta AWS resource, please reach out to support@fugue.co. Refer to Service Coverage - AWS & AWS GovCloud for more information.
Visualizer - Azure Service Coverage¶
Fugue added service coverage support in the visualizer for the Azure resources in beta.
UX Improvements to the Group and Notification Pages¶
Fugue added environment search on the Group and Notification pages, making it easier to configure specific environments with groups or notifications. You can search by name, ID, or provider. See Role-Based Access Control (RBAC) and Notifications for details.
2020.08.17¶
New Azure Rules¶
As part of our commitment to continually updating rules associated with compliance families, we have created 10 additional Azure rules including:
Key Vault ‘Enable Soft Delete’ and ‘Enable Purge Protection’ should be enabled
Monitor Activity Log Alert should exist for Create Policy Assignment
Monitor Activity Log Alert should exist for Create or Update Network Security Group
Monitor Activity Log Alert should exist for Delete Network Security Group
Monitor Activity Log Alert should exist for Create or Update Network Security Group Rule
Monitor Activity Log Alert should exist for Delete Network Security Group Rule
Monitor Activity Log Alert should exist for Create or Update Security Solution
Monitor Activity Log Alert should exist for Delete Security Solution
Monitor Activity Log Alert should exist for Create or Update or Delete SQL Server Firewall Rule
Monitor Activity Log Alert should exist for Update Security Policy
These rules will cause compliance event notifications. If you have any questions, please reach out to support@fugue.co.
Custom Rule Severity¶
You can modify the severity of your custom rules from high to critical, medium, low, or informational. Refer to Rule Severity Definitions for more information, and see instructions for modifying rules via the UI or API.
Waiver Improvements¶
Fugue supports the ability to waive all resources for a rule within your environment. Refer to Rule Waivers and Working with Rule Scope for more information.
Azure Government Support¶
Fugue supports Azure Government via the Fugue application and API. All existing functionality for Azure is supported by Azure Government. Refer to Setup - Azure for more information.
Expanded Azure Service Coverage- Beta¶
Fugue adds beta support for Azure Insights and Monitor types. If you are interested in gaining access to the beta Azure resources, please reach out to support@fugue.co.
Visualizer Updates¶
Fugue improves the speed of image export.
UX Improvements¶
Fugue improves the environment search by storing the search term in the browser session.
Bug Fixes¶
API bug fixes, fugue-client updates (e.g., ability to set custom rule severity), and more.
2020.08.04¶
Enhancements to the All Environments Landing Page¶
Fugue made the following enhancements to the All Environments landing page:
Environment search improvements
Search environments by the following key-value pairs: name, provider, and ID (i.e., AWS account ID, Azure subscription ID, and environment ID)
Search terms can be saved and shared via URL
Pagination for faster performance
Visualizer¶
The visualizer supports searching on resource ID, resource type, and resource name. Search makes it easier to find specific resources and drill down on resource details.
Extended Service Coverage Support for Azure¶
Fugue launched support for the following Azure services:
Azure.Automation.Account
Azure.Automation.Credential
Azure.Automation.Schedule
Azure.Cdn.Profile
Azure.Compute.AvailabilitySet
Azure.Compute.Image
Azure.Compute.SharedImageGallery
Azure.Compute.Snapshot
Azure.Compute.VirtualMachineScaleSet
Azure.Container.Group
Azure.Container.Registry
Azure.Databricks.Workspace
Azure.KeyVault.Vault
Azure.MySQL.Database
Azure.MySQL.FirewallRule
Azure.MySQL.Server
Azure.MySQL.VirtualNetworkRule
Azure.Network.ApplicationGateway
Azure.Network.ApplicationSecurityGroup
Azure.Network.DDoSProtectionPlan
Azure.Network.DNSZone
Azure.Network.Firewall
Azure.Network.LoadBalancer
Azure.Network.RouteTable
Azure.PostgreSQL.Database
Azure.PostgreSQL.VirtualNetworkRule
Azure.PostgreSQL.Server
Azure.PostgreSQL.FirewallRule
Azure.SQL.Database
Azure.SQL.ElasticPool
Azure.SQL.VirtualNetworkRule
Deprecating TLS 1.0 and TLS 1.1¶
On September 29, 2020, Fugue will be deprecating support for Transport Layer Security (TLS) versions 1.0 and 1.1 to align with industry best practices and data integrity. If you have any questions, please contact support@fugue.co.
2020.07.30¶
Fugue supports the following new rules:
CloudTrail trails should be configured to log data events for S3 buckets
CloudTrail trails should be configured to log management events
CloudTrail should have at least one CloudTrail trail set to a multi-region trail
CloudTrail trails should not be associated with missing SNS topics
EC2 instance detailed CloudWatch monitoring should be enabled
IAM roles used for trust relationships should have MFA or external IDs
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 636 (LDAP SSL)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 7001 (Cassandra)
Redshift cluster ‘Publicly Accessible’ should not be enabled
EC2 instances should not have a public IP association (IPv4)
S3 bucket replication (cross-region or same-region) should be enabled
S3 bucket policies and ACLs should not be configured for public read access
2020.07.21¶
Compliance Family¶
Users can select or deselect the Custom Rule compliance family when creating or editing an environment.
Note that when creating environments you will need to explicitly enable custom rules if those should be active on the environment. Any environment creation scripts may need to take this into account if they assume custom rules are automatically added.
Updates to Data Export¶
Data export has been updated to include rules with a waived rule result.
The rule description field has been updated to include the rule message that displays within the compliance modal. For example, VPC flow logging should be enabled. AWS VPC Flow Logs provide visibility into network traffic that traverses the AWS VPC. Users can use the flow logs to detect anomalous traffic or insight during security workflows.
Bug Fixes¶
Resolved a bug where compliance families not selected for a specific environment would display in the panel in the visualizer and on the Waivers page.
Improved the load time of the visualizer.
Resolved a bug where users assigned with the read role could not export environment data.
2020.07.08¶
Rule Waivers¶
Rule waivers provide exceptions on rule violations that apply to a specific resource. Waived rules no longer count as “Failed” in compliance calculations.
You can view waived resources on the Waivers page.
Refer to Rule Waivers for more information about working with waivers.
Rule Severity on the Compliance by Resource Page¶
Rule severity establishes the level of risk posed by a misconfiguration to your cloud security posture. Severity falls into the following categories: critical, high, medium, or low. Adding rule severity to the Compliance by Resource page makes it easier for you to prioritize fixing the resources that have a higher severity. Refer to Compliance for more information on rule severity.
Two New RBAC Policies¶
Fugue added two new RBAC policies – Contributor and Auditor. The Contributor policy grants all the permissions in the Editor policy, as well as allows users to waive rules, create custom rules, and create environments. The Auditor policy grants all the permissions in the Read Only policy, as well as allows users to run a scan and create notifications. For more information on working with RBAC, refer to Role-Based Access Control (RBAC).
Bug Fixes¶
The rule that checks the CloudFront viewer protocol policy was updated to support redirect-to-https in addition to https-only. Refer to the remediation steps for more information.
2020.06.05¶
Ability to export compliance data via the UI¶
Fugue now supports the capability to export compliance data for multiple environments at the same time for AWS accounts and Azure subscription levels. On the Environment Landing page, clicking on the Export Data button allows you to download the Rule Results with Controls data as a CSV or Excel (.xlsx). Refer to Export Data for more information.
2020.06.04¶
Extended Azure Service Coverage Beta¶
Fugue launched support for resources in the following Azure services in beta:
Azure.Automation.Account
Azure.Automation.Credential
Azure.Automation.Schedule
Azure.Cdn.Profile
Azure.Compute.AvailabilitySet
Azure.Compute.Image
Azure.Compute.SharedImageGallery
Azure.Compute.Snapshot
Azure.Compute.VirtualMachineScaleSet
Azure.Container.Group
Azure.Container.Registry
Azure.Databricks.Workspace
Azure.KeyVault.Vault
Azure.MySQL.Database
Azure.MySQL.FirewallRule
Azure.MySQL.Server
Azure.MySQL.VirtualNetworkRule
Azure.Network.ApplicationGateway
Azure.Network.ApplicationSecurityGroup
Azure.Network.DDoSProtectionPlan
Azure.Network.DNSZone
Azure.Network.Firewall
Azure.Network.LoadBalancer
Azure.Network.RouteTable
Azure.PostgreSQL.Database
Azure.PostgreSQL.VirtualNetworkRule
Azure.PostgreSQL.Server
Azure.PostgreSQL.FirewallRule
Azure.SQL.Database
Azure.SQL.ElasticPool
Azure.SQL.VirtualNetworkRule
If you are interested in gaining access to these Azure beta resources, please send an email to support@fugue.co.
For a full list of supported Azure types, see Service Coverage - Azure.
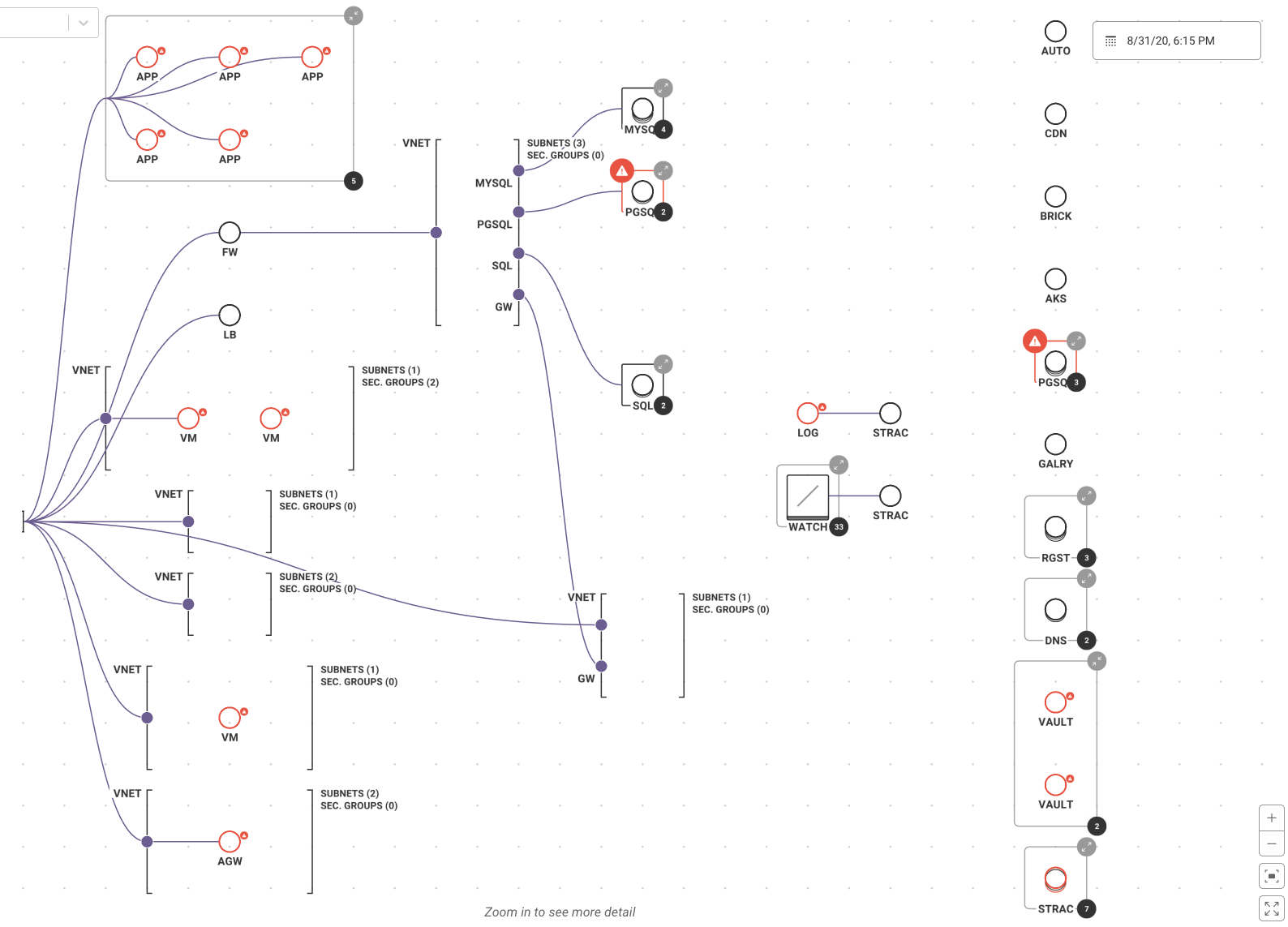
Visualizer Updates¶
Updates to the visualizer include:
The region name displays when the visualizer is zoomed out.
Expanded support for Azure beta service coverage:
Azure.Automation.Account (AUTO)
Azure.Cdn.Profile (CDN)
Azure.Compute.SharedImageGallery (GALRY)
Azure.Container.Registry (RGST)
Azure.Databricks.Workspace (DATAB)
Azure.MySQL.Server (MYSQL)
Azure.Network.ApplicationGateway (AGW)
Azure.Network.DNSZone (DNS)
Azure.Network.Firewall (FW)
Azure.Network.LoadBalancer (LB)
Azure.PostgreSQL.Server (PGSQL)
Made an UX improvement — clicking the compliance icon redirects you to the compliance section in the panel.
Refer to Visualizer for more information.
Updates to Compliance Rules¶
The following rules were added to the CIS Controls 7.1., ISO 27001, SOC 2, NIST 800-53, and HIPAA Compliance Families:
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 11215 (Memcached SSL)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 135 (MSSQL Debugger)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 137 (NetBIOS Name Service)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 138 (NetBios Datagram Service)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 139 (NetBios Session Service)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 1433 (MSSQL Server)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 1434 (MSSQL Admin)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 2382 (SQL Server Analysis Services browser)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 2383 (SQL Server Analysis Services)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 2484 (Oracle DB SSL)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 3020 (CIFS / SMB)
The following Azure rules were added to the CIS Controls 7.1., ISO 27001, SOC 2, NIST 800-53, HIPAA, GDPR, and PCI Compliance Families:
MySQL Database server firewall rules should not permit start and end IP addresses to be 0.0.0.0
PostgreSQL Database server firewall rules should not permit start and end IP addresses to be 0.0.0.0
Ensure Azure Application Gateway Web application firewall (WAF) is enabled
MySQL Database server ‘enforce SSL connection’ should be enabled
PostgreSQL Database server ‘enforce SSL connection’ should be enabled
Updated AWS CIS benchmark 2.1 rule to reflect that it needs to check that there is at least one CloudTrail with multi-region enabled that has logging on and management events set to true.
2020.05.29¶
Expanded AWS Service Coverage¶
Fugue launched support for resources in the following AWS services:
AWS Private Certificate Authority
Directory Service
Elastic File System
Glacier
Inspector
Kinesis
Kinesis Data Firehose
Organizations
Systems Manager (SSM)
To enable the services, update the Fugue IAM role to include the required permissions. Scan permissions are below.
"acm-pca:DescribeCertificateAuthority",
"acm-pca:GetCertificateAuthorityCertificate",
"acm-pca:GetCertificateAuthorityCsr",
"acm-pca:ListCertificateAuthorities",
"acm-pca:ListTags",
"ds:DescribeConditionalForwarders",
"ds:ListTagsForResource",
"elasticfilesystem:DescribeLifecycleConfiguration",
"elasticfilesystem:DescribeTags",
"glacier:GetVaultNotifications",
"glacier:ListTagsForVault",
"kinesis:DescribeStreamSummary",
"ssm:GetDocument",
"ssm:GetMaintenanceWindow",
"ssm:GetMaintenanceWindowTask",
"ssm:GetParameter",
"ssm:GetParameters",
"ssm:GetPatchBaseline",
"ssm:ListAssociations",
"ssm:ListResourceDataSync",
"ssm:ListTagsForResource"
Bug Fixes¶
Updated IAM permissions required for AWS config to include reading tags.
Fixed security group rule message to correctly include the open port on the Compliance by Control section.
2020.05.12¶
Support for CIS Controls 7.1¶
Fugue has added support for the CIS Controls 7.1 compliance family. CIS Controls are a set of actions for cyber defense based on common attack patterns, created by a group of experts such as NSA Red and Blue teams, the US Department of Energy nuclear energy labs, and law enforcement organizations. Refer to Compliance for more information on how to get started using the CIS Control compliance family.
Visualizer Updates¶
Updates include:
Added support for Amazon Redshift and Amazon EFS
Exporting a diagram of the visualizer now lists AWS regions
Added resource details for stubbed/implicit resources
Updates to Compliance Terminology¶
Fugue has updated terminology in our web user interface to provide more clarity on compliance across resources, rules, and controls.
Changes include:
Adjusting terminology to “controls” (from “rules”), where the product is referring to compliance controls.
Updating control evaluations and resource evaluations to have compliant/noncompliant values, as opposed to pass/fail.
Terminology definitions and explanations of how compliance evaluations are calculated are enumerated on the Compliance page.
2020.04.29¶
Scoping Environments to Multiple Regions¶
You can now create an AWS environment that spans multiple regions, as shown below. For more information on creating an environment that scans multiple regions, refer to Setup - AWS & AWS GovCloud.
Note: You cannot add multiple regions to existing environments. You need to create new environments through the API or UI. Once you have created the new environments, you can update their selected regions through the API. Refer to the AWS User Guide for more information.
You can filter by region on the Compliance by Resource page, as shown below.
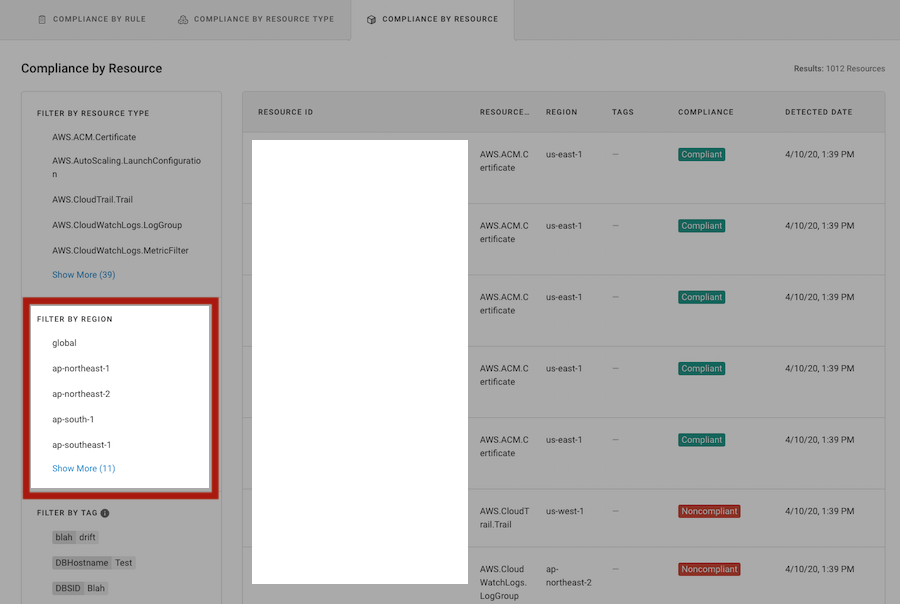
When an environment contains more than one region, horizontal brackets labeled by region separate the infrastructure. Global resources, such as the CloudFront distributions below, are labeled global. Refer to Visualizer for more information.
Responsive Registration Page and More¶
The Registration and Forgot Password pages are now responsive, as shown below.
Visualizer Updates¶
Compliance view updates
New References portion in resource details panel
The entire VPC or VNet is no longer shaded all red when it has compliance violations, as shown below. Refer to Visualizing Resource Compliance State for more information.
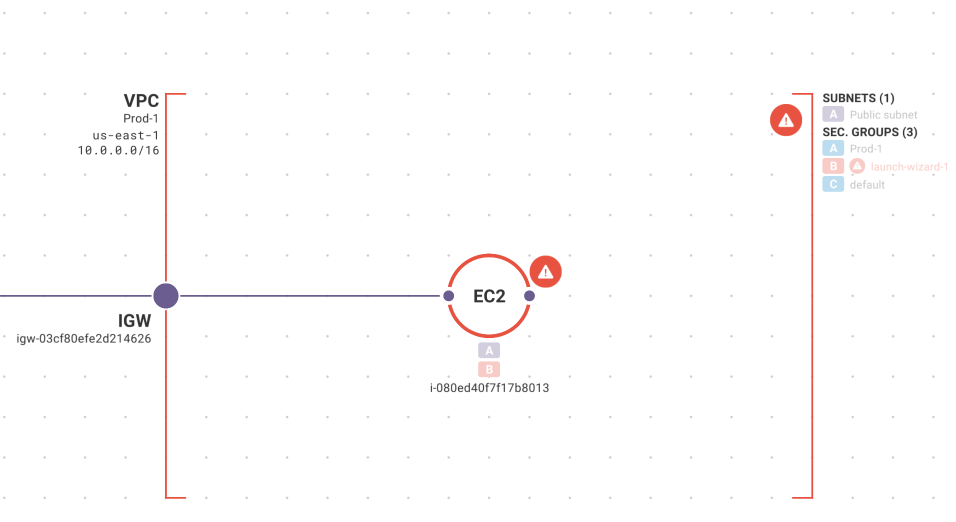
When you select a resource to view the resource details, a References panel is added, which lists other resources related to the currently selected resource. For example, if you select a VPC, it lists the associated security groups, subnets, networks, and internet gateways. You can click on a resource listed in the Reference section and it redirects you to that resource, as shown below. Refer to Viewing Resource Details for more information.
2020.04.16¶
Role Based Access Control (RBAC)¶
Fugue added a new RBAC policy – Editor. The Editor policy grants all the permissions in the Read Only policy and some of the permissions in the Admin policy. Editors cannot create or delete environments, configure custom rules, manage users, or configure API clients. They can, however, take actions such as changing environment settings, running scans, and configuring notifications and reports. For more information on working with RBAC, refer to Role-Based Access Control.
Cloud Resource Visualization¶
Cloud resource visualization now supports visualizing VPC gateway endpoints (refer to our blog post on Cloud Network Security 101: AWS VPC Endpoints for more information on security for VPC endpoints). VPC gateway endpoints (ENDPT) are shown as a line between a VPC and all S3 buckets or all DDB tables in the same region, as shown below. Refer to Visualizer for more information on working with cloud resource visualization.
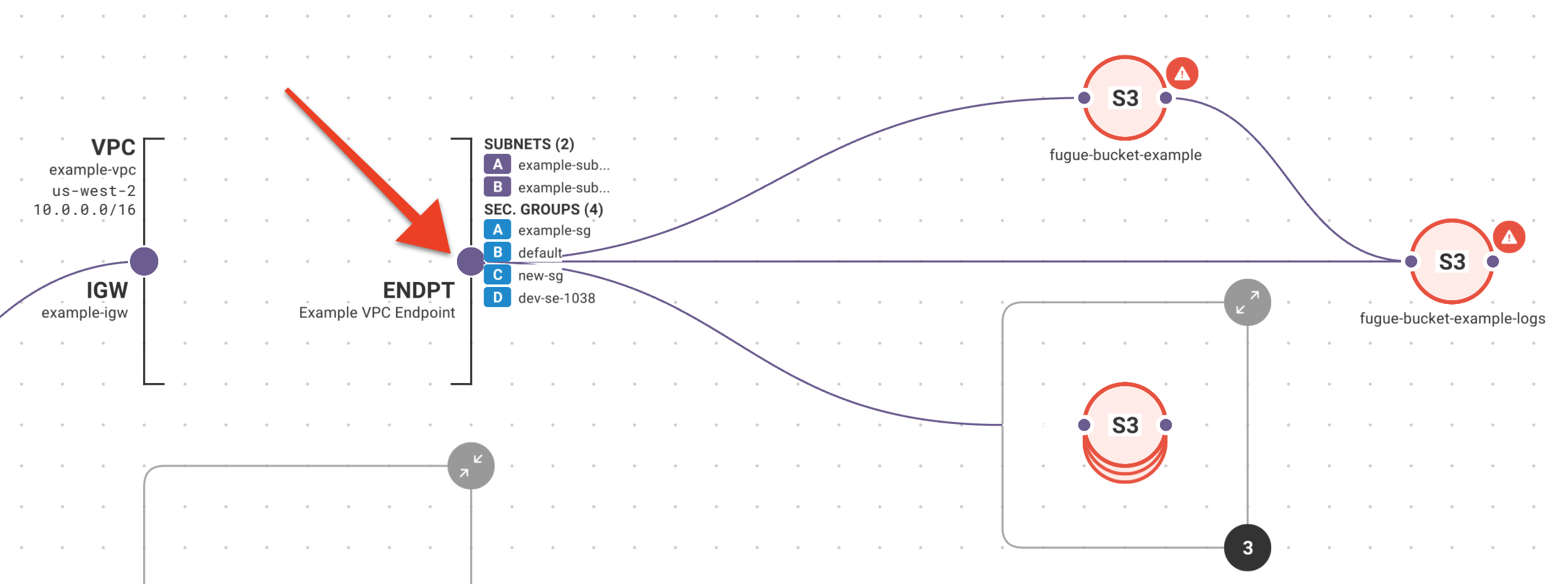
2020.04.07¶
UX Improvements¶
In the environment search field, you can enter spaces when searching for an environment, as shown below:
Rule Engine Upgrade¶
All rules evaluated by Fugue now use the open source Fugue Regot Toolkit, also known as Fregot. This yields performance improvements that will increase scan speeds for some large environments. Check out Fregot on GitHub.
New IAM Permissions Required¶
Due to internal upgrades, additional permissions are needed to scan or enforce any of the following AWS services:
CloudWatch
ECR
EFS
MediaStore
S3
SNS
SSM
Step Functions (SFN)
WAF
If your environments are configured to scan or enforce any of these services, you should update your IAM role policy to include these read-only permissions for the services you’ve enabled:
"cloudwatch:ListTagsForResource",
"ecr:ListTagsForResource",
"elasticfilesystem:DescribeLifecycleConfiguration",
"mediastore:ListTagsForResource",
"s3:GetBucketObjectLockConfiguration",
"sns:ListTagsForResource",
"ssm:GetDocument",
"states:ListTagsForResource",
"waf:GetLoggingConfiguration",
"waf:ListTagsForResource",
If these permissions are not included, scans will not fail; however, you may see an Incomplete Scan Results message.
For instructions, see How To: Update the Fugue IAM Role.
For more information about how Fugue handles IAM permissions, see IAM Policy Permissions.
Compliance Event Notifications¶
Previously, Fugue generated notifications when the following events occurred:
Existing resource transitions from compliant to noncompliant, or vice versa
Newly added resource is noncompliant
Existing resource that was missing data transitions to compliant, or vice versa
Existing resource that was missing data transitions to noncompliant, or vice versa
We are changing notifications logic to only summarize events where:
Existing resource transitions from compliant to noncompliant, or vice versa
Newly added resource is noncompliant
Bug Fixes¶
Fixed scan failure when no resources were detected in an environment and drift detection was enabled.
Improved the rules that check for inappropriate port 80 and 5800 ingress to work with ELBv2 and to describe what additional resources are relevant to the failure, if any.
2020.03.17¶
The visualizer now allows selection of VPCs and auto scaling groups (ASGs) in order to view the resource configuration details for those types.
Fugue now supports indicating a resource is transient in nature. When a resource is tagged with the key
fugue:transientand valuetruein AWS or Azure, drift events are not generated for changes to that resource. This is useful in situations where resources are created and destroyed dynamically.
AWS:
Azure:
2020.03.03¶
On-Demand Scan via the UI¶
Previously, you could only kick off an on-demand scan via the API. Now, Fugue enables you to use the UI to initiate on-demand scans. From the Actions drop-down, select Start New Scan within an environment to start a scan, as shown below.
Cloud Resource Visualization – View Resource Details¶
You can view configuration details about your resources within the cloud resource visualization. To view the resource details, zoom in and click on a resource, as shown below. See Visualizer for more information.
UX Improvements to Settings and Setting a Baseline¶
The Establish Baseline button and Settings are under the new Actions button, as shown below.
Bug Fixes¶
A bug has been resolved where the custom rule family would still display within an environment even after you delete all custom rules. Now if you delete all custom rules, the custom rule family no longer displays.
Removed Obsolete VPC Flow Logs Rule¶
The rules for confirming VPC flow logs are correctly enabled have been updated. Overall compliance results will remain unchanged; however, you may see compliance events relating to this change to the underlying rules.
2020.02.14¶
Cloud Resource Visualization – Collections & Additional Resource Support¶
An improvement has been made to cloud resource visualization to illustrate a resource that contains other resources, and this is known as a collection. For example, AWS auto scaling groups containing EC2 instances, and ECS services containing tasks, are rendered as collections. A collection is depicted as a square with a thick border containing zero or more nodes. Collections may also be expanded or collapsed to view individual nodes.
Additionally, the cloud resource visualizer now supports visualizing AWS.ECS.Task resources, as well as AWS.EC2.Instance resources belonging to auto scaling groups.
Rule Updates¶
The CIS 1-16 rule was updated to be more comprehensive by flagging users with inline policies.
2020.01.31¶
Additional AWS Resources - Beta¶
Fugue launched support for resources in the following AWS services:
Systems Manager
Directory Service
Kinesis
Kinesis Data Firehose
Elastic File System
Inspector
ACM PCA (AWS Certificate Manager Private Certificate Authority)
Glacier
If you are interested in gaining access to these beta resources, please email support@fugue.co.
Bug Fixes¶
The release also includes fixes including:
Ability to query by the “custom” family when retrieving compliance using the API
Optimize a Fugue Best Practices rule that ran slowly in some environments
Allow values greater than or equal to 24 for the CIS 1-10 password reuse control
Fix drift detection with some Cognito User Pool Clients, KMS grants, and Load Balancer Listener Rules
2020.01.13¶
Cloud Resource Visualization – Keyboard Shortcuts¶
The visualizer supports keyboard shortcuts. These shortcuts include:
Arrow Keys: Pan around the visualizer.
Plus (Equals) / Minus (Underscore) Keys: Zoom in and out.
Period Key: Open/close the sidebar.
Spacebar (Double Tap): Recenter the visualizer.
Multi-Factor Authentication Support (MFA)¶
Fugue supports multi-factor authentication (MFA). After you enable MFA, the next time you log in, you are prompted to scan a QR code using an authenticator app, as shown below. When you log into Fugue anytime subsequently, you are prompted to enter a one-time code after authenticating:
2019.12.23¶
Cloud Resource Visualization - Export Functionality¶
Improvements have been made to the export functionality for cloud resource visualization. When you export a .PNG of resources, the environment name, date/time of the scan, and account ID for AWS or subscription ID for Azure are included, as shown below. This makes it easier to identify the environment that you are looking at.
Additionally, the image filename includes the name of the environment, as well as the date/time of the scan.
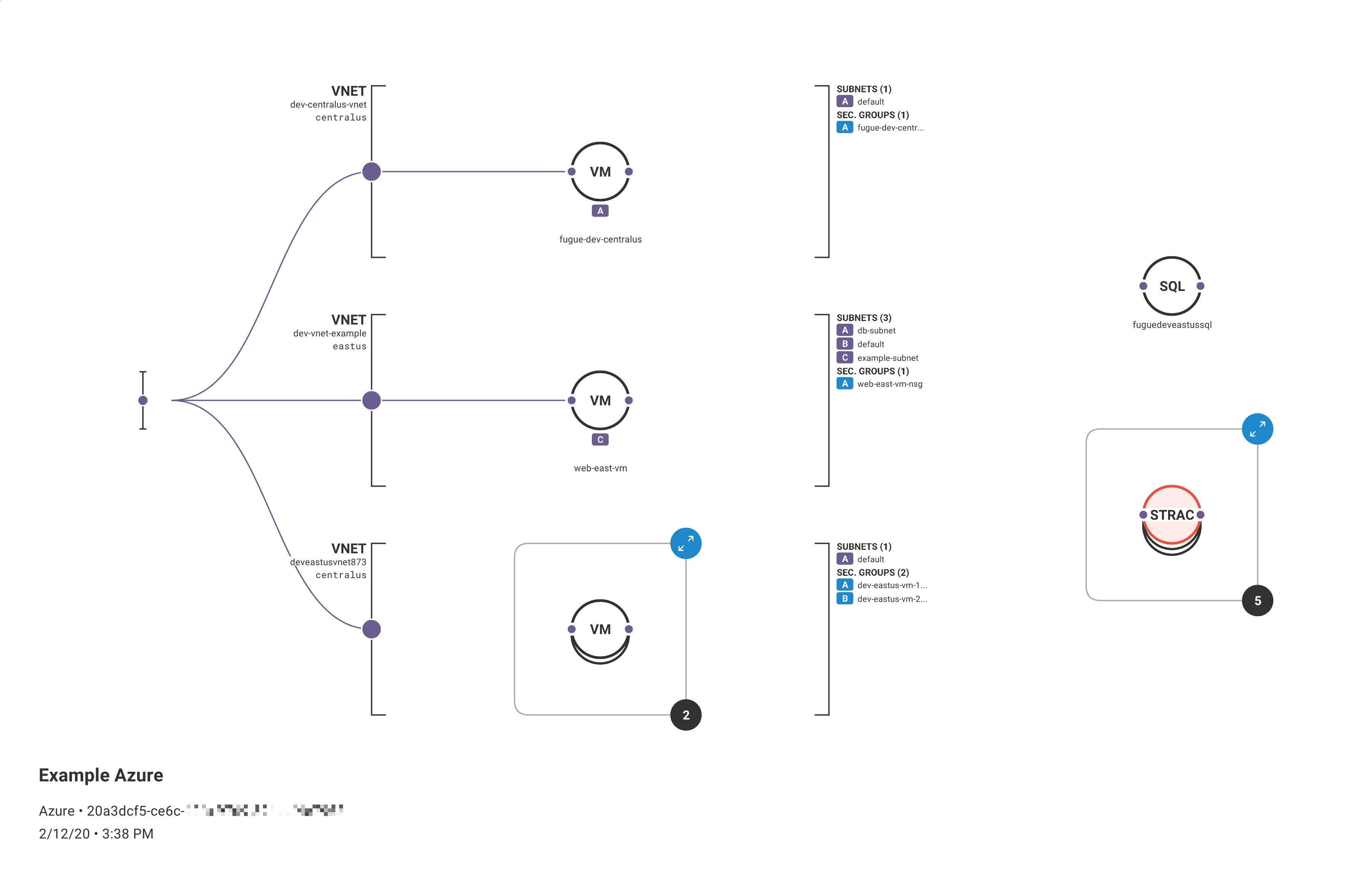
Cloud Resource Visualization - VPC Peering¶
Cloud resource visualization now shows VPC peering, as shown below. This allows you to see which VPCs have peering relationships.
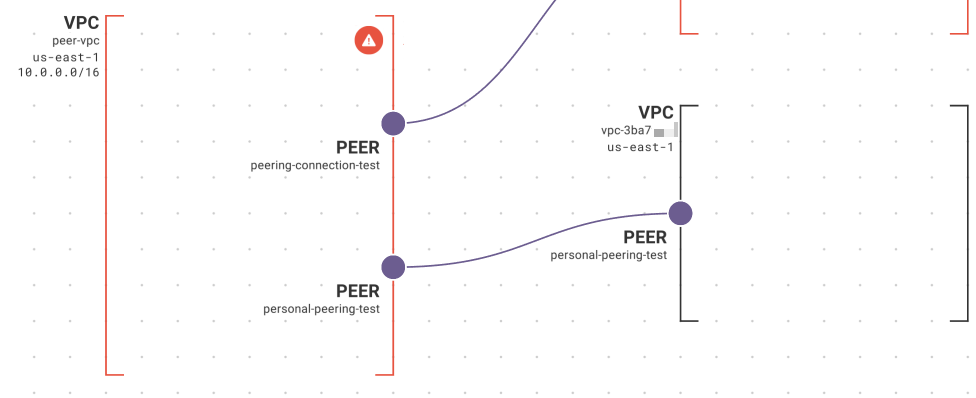
Search By Environment¶
The All Environments landing page now allows you to search by environment name or ID:
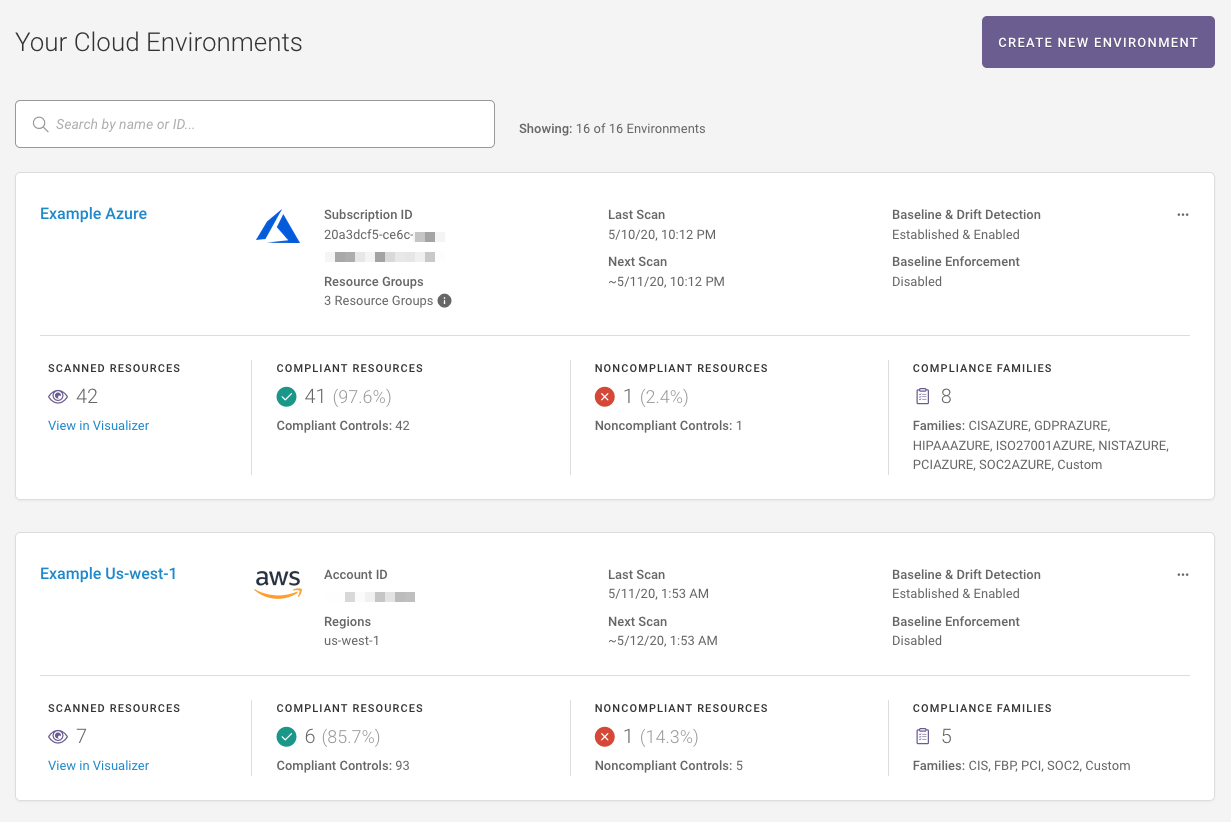
2019.11.21¶
Rule Remediation Steps in Documentation¶
The online documentation includes rule remediation steps for many common compliance violations. Follow the steps to manually bring resources back into compliance using the AWS Management Console, AWS CLI, Azure Portal, or Azure CLI. For the list of rule remediation steps, refer here.
Exporting Visualizer Diagrams and Customizing Your Visualizer View¶
You can export an image of your Fugue visualized environment, as well as customize what information displays within the visualizer, such as compliance information, and collapse/expand all groups. See Exporting a Diagram.
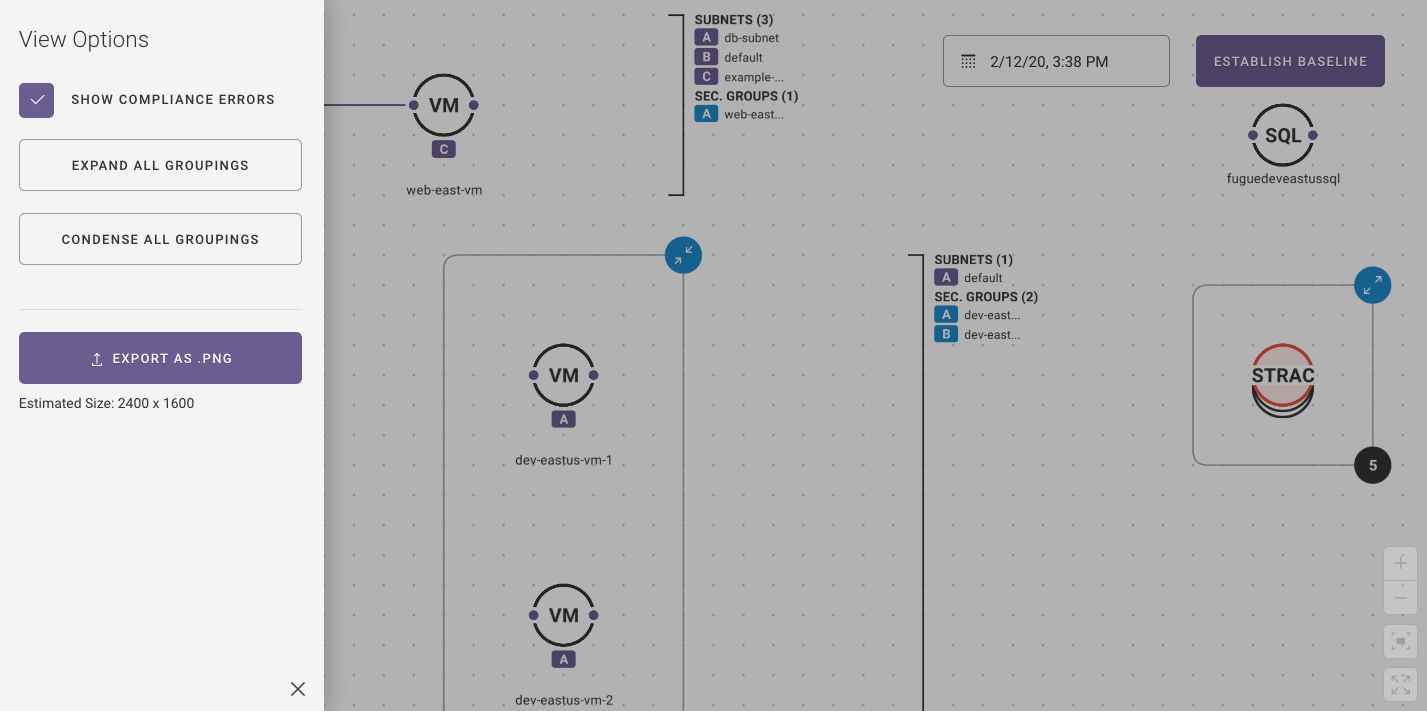
Ability to Delete User Groups¶
You can delete user groups, as shown below. See How to Delete Groups.
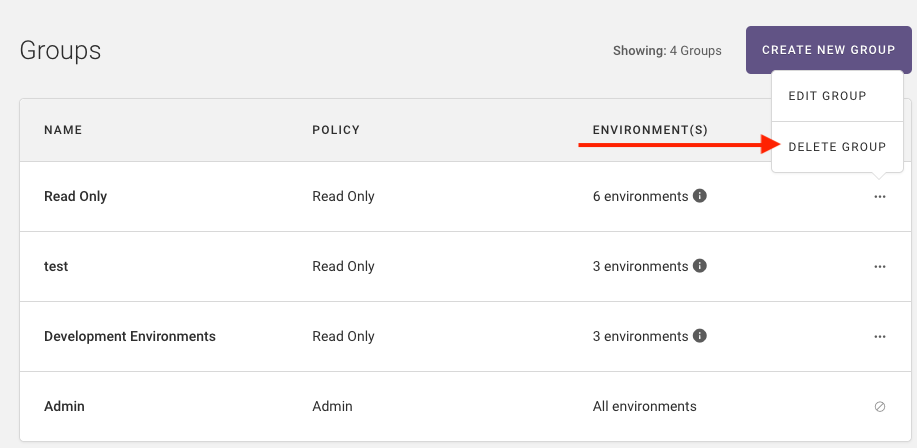
Fugue Developer and Fugue Enterprise¶
Fugue is now available in two plans: Developer and Enterprise. For more information, see the documentation in Fugue Plans.
New Account Overview Page¶
The Account Overview page lists your plan type, which is Enterprise for existing customers. Refer to the online documentation for more information.
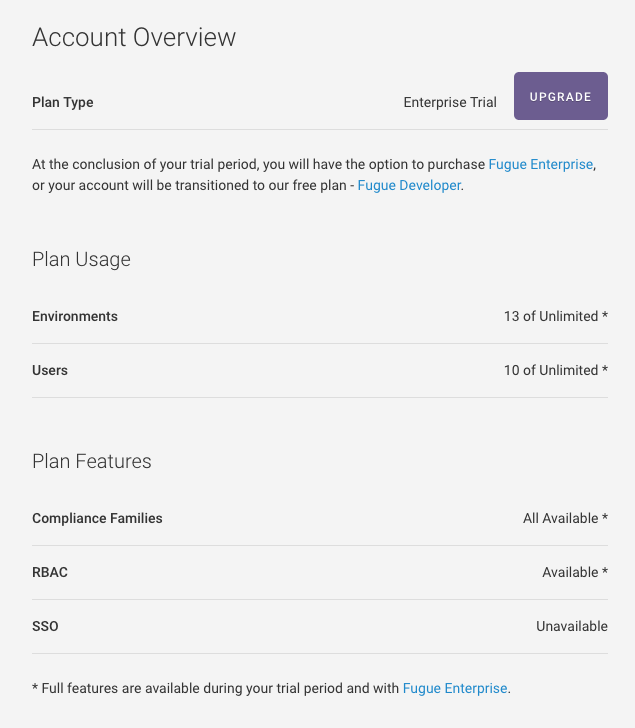
2019.10.31¶
Single Sign-On (Beta)¶
Fugue is excited to announce support for single sign-on (SSO) in beta. SSO allows users to provision and deprovision users from an existing identity provider (IdP).
The Fugue login page is changing, as shown below. Non-SSO users enter their username and password to log into Fugue:
Once SSO is enabled on your organization, users enter their email address and log into Fugue using your IdP. If you are interested in gaining access to SSO beta, please contact support@fugue.co.
Additional Compliance Family Support for Azure¶
Fugue now supports the following compliance families for Azure: ISO 27001, SOC 2, HIPAA, GDPR, NIST SP 800-53, and PCI-DSS.
Fugue Best Practices¶
Fugue released a set of Best Practices checks to complement existing controls to detect critical misconfigurations that can be exploited.
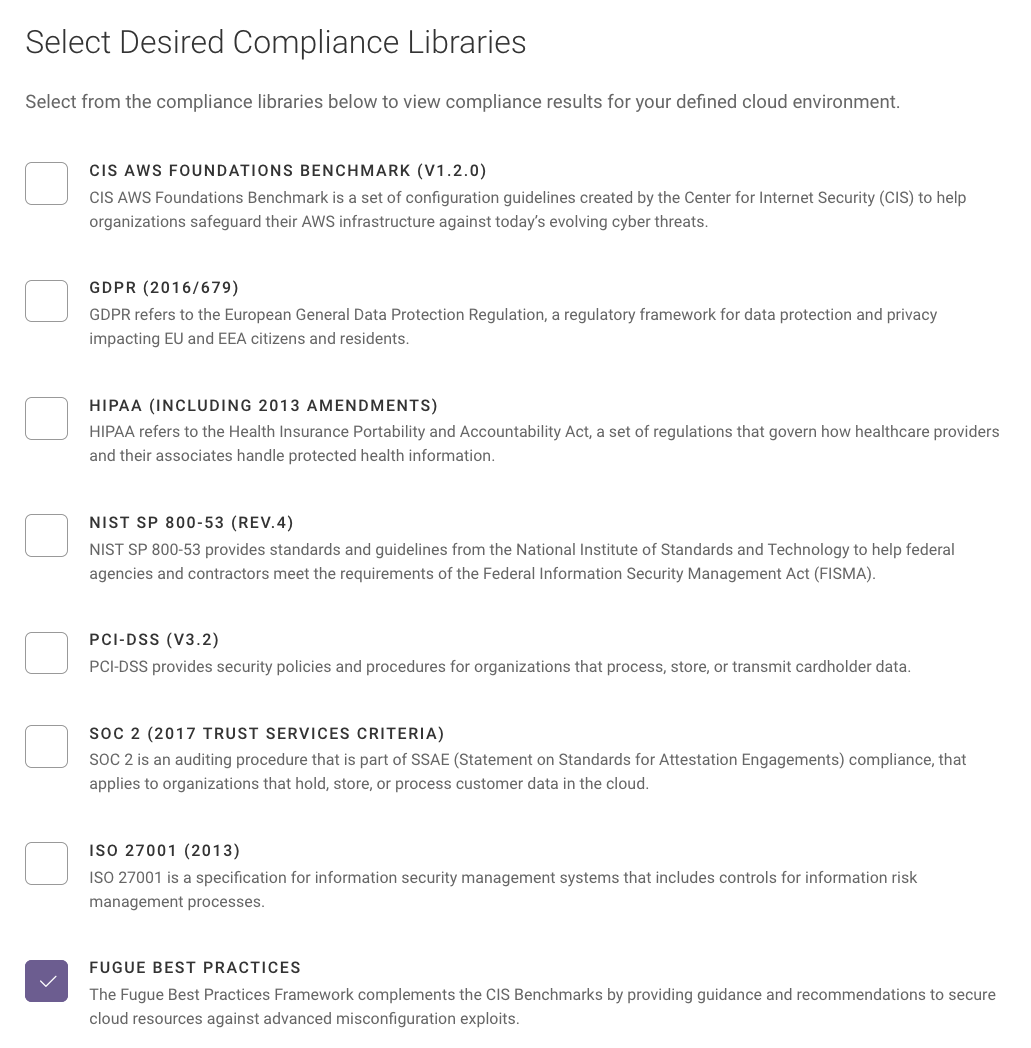
Some rules that are part of the Fugue Best Practices compliance family include:
IAM policies should not allow broad list actions on S3 buckets
IAM role trust policies should not allow all principals to assume the role
IAM roles attached to instance profiles should not allow broad list actions on S3 buckets
S3 bucket policies should not allow all actions for all principals
S3 bucket policies should not allow list actions for all principals
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 9200 (Elasticsearch)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 9300 (Elasticsearch)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 2379 (etcd)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 27017 (MongoDB)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 27018 (MongoDB)
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP port 27019 (MongoDB)
2019.10.17¶
Expanded AWS Service Coverage¶
Fugue now supports the following AWS services:
ACM (AWS Certificate Manager)
API Gateway
Cognito
ECR
ECS
EKS
GuardDuty
Lambda
Macie
MediaStore (AWS Elemental MediaStore)
RedShift
Route 53
Step Functions (SFN)
Secrets Manager
S3: Attributes to block public access
To start scanning for these newly supported services, you should either:
Option 1: Launch a new CloudFormation stack that contains the SecurityAudit read-only policy and add the following resources listed below as part of your inline policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"apigateway:GET",
"cloudwatch:GetDashboard",
"cloudwatch:ListDashboards",
"cognito-idp:DescribeIdentityProvider",
"cognito-idp:DescribeResourceServer",
"cognito-idp:DescribeUserPool",
"cognito-idp:DescribeUserPoolClient",
"cognito-idp:DescribeUserPoolDomain",
"cognito-idp:GetGroup",
"cognito-idp:ListGroups",
"cognito-idp:ListIdentityProviders",
"cognito-idp:ListResourceServers",
"cognito-idp:ListUserPoolClients",
"dynamodb:ListTagsOfResource",
"elasticache:ListTagsForResource",
"lambda:GetAlias",
"lambda:GetEventSourceMapping",
"lambda:GetFunction",
"macie:ListMemberAccounts",
"macie:ListS3Resources",
"mediastore:DescribeContainer",
"s3:ListBucket",
"secretsmanager:DescribeSecret",
"sns:GetSubscriptionAttributes",
"sns:ListSubscriptions",
"states:DescribeStateMachine",
"waf:GetWebACL"
],
"Resource": "*",
"Effect": "Allow",
"Sid": "0"
}
]
}
Option 2: Update your existing AWS IAM policy to include the SecurityAudit read-only policy if it is already not attached and add the following resources listed below as part of your inline policy:
Refer to AWS IAM Permissions and Add an Inline Policy for more information.
Updates to the Visualizer¶
Added the ability to pinch on your trackpad to zoom in and out on the visualizer.
2019.10.03¶
Custom Rules¶
Users can now write custom rules to extend Fugue functionality to specific enterprise requirements, with CRUD actions and syntax/testing available via UI, API, and CLI.
Custom rules are written with Open Policy Agent’s Rego query language. OPA is a policy-as-code framework and CNCF open source project commonly used for policy on Kubernetes and other cloud technologies.
Visualizer¶
Collapsed nodes that have a mix of compliant and non compliant resources display as stacks with red and black coloring, as highlighted below:
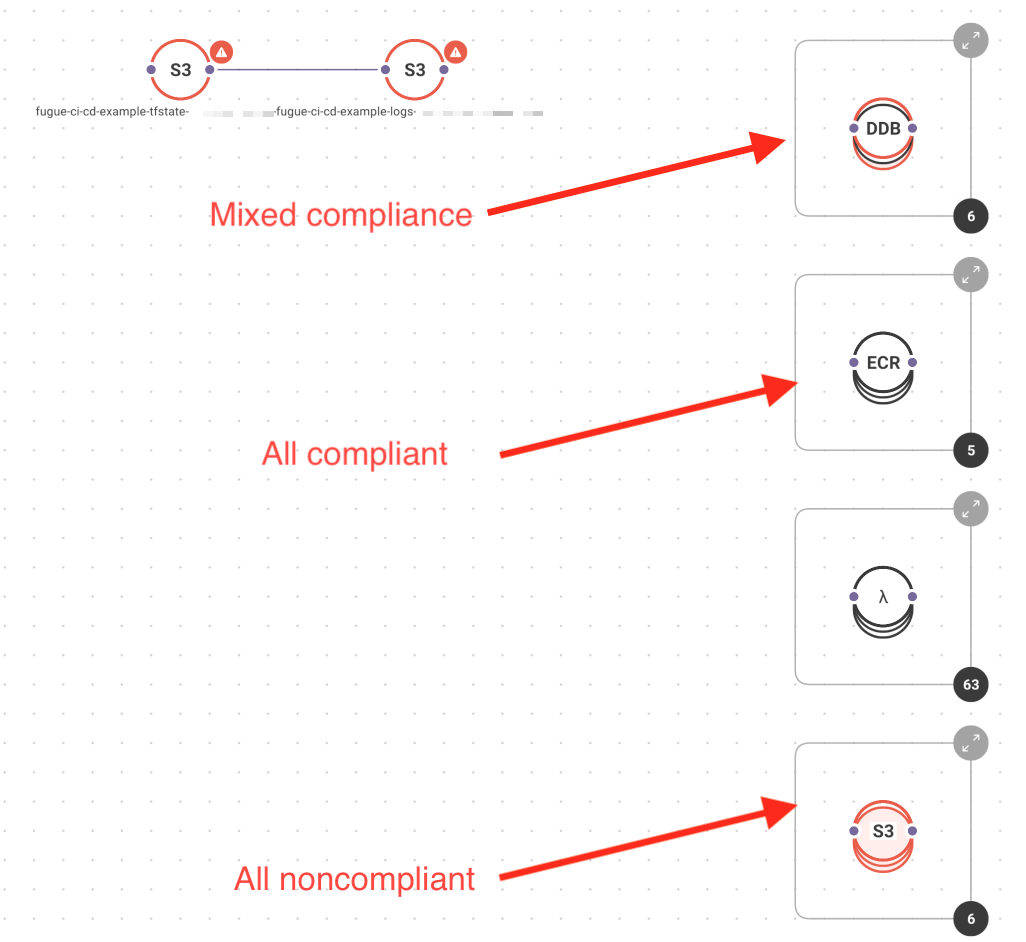
2019.09.13¶
Visualizer updates¶
Visualizer UX improvements — Added an expand icon and number of resources that exist within a collapsed node. For example, if you have 13 S3 buckets collapsed in a node, the number 13 is shown, as shown below. Clicking the icon expands the collapsed S3 buckets.
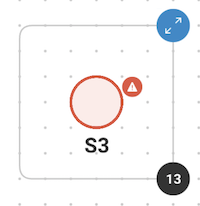
Clicking the
 (warning) icon displays the compliance violations for a resource.
(warning) icon displays the compliance violations for a resource.Clicking on a subnet or security group within a node or on the list on the side, highlights all the places within your infrastructure where the security group or subnet resides, as shown below.
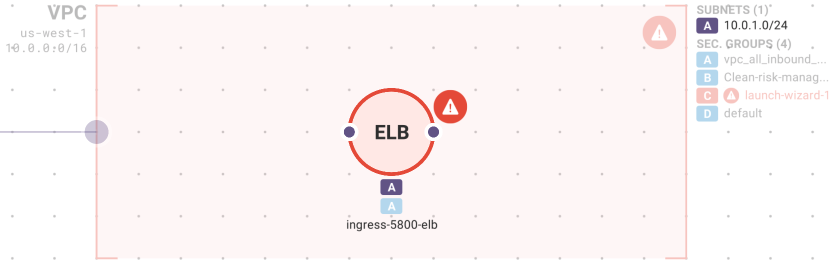
Displaying the compliance violations for subnets and security groups.
Performance improvements
IAM role generation updates¶
Updates to IAM role generation for read-only permissions, which allows Fugue to scan and detect drift for your environments. When you create a new IAM role utilizing the Fugue UI, the Security Audit read-only policy is attached to the role along with inline policies to cover other permissions that are not covered by the Security Audit policy. If you have existing environments, you can continue to use your existing IAM role as is or choose to attach the SecurityAudit policy and remove the inline policies covered by the Security Audit policy.
2019.08.23¶
Updates to the navigation within the Environment Details page— the visualizer is located on its own page, Environment Settings have been moved to the top level navigation, and the Drift Events page is renamed to Events.
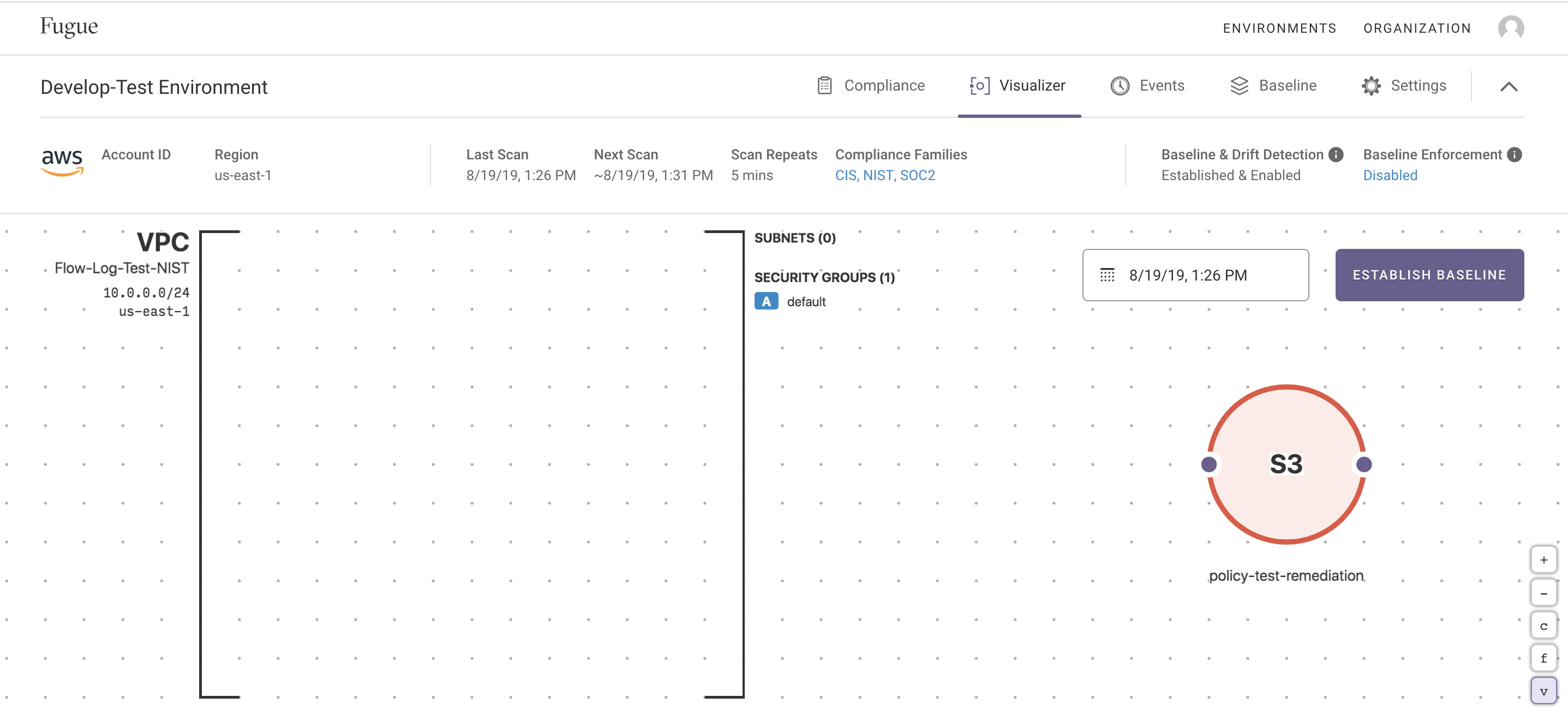
Updates to the user interface. The Organizations tab is now located at the same level as Environments and updates were made to the environment cards, as shown below. Additionally, on the Environment Landing page, selecting View in Visualizer redirects users to the Visualizer page.
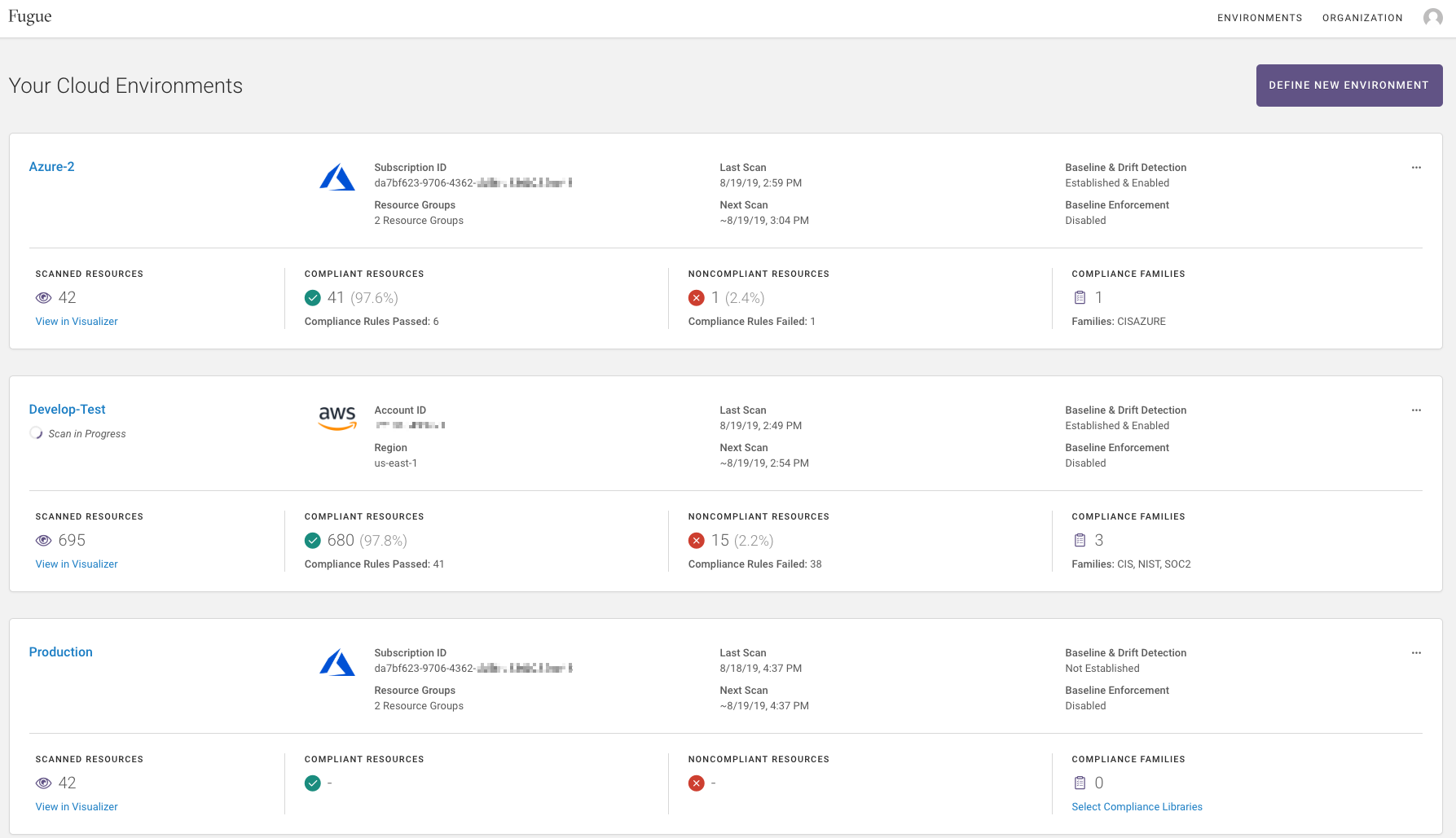
Baseline enforcement is now supported for Azure.
Displaying compliance errors within the visualizer on VPC.
The /resources API endpoint now requires authorization. Previously, users were able to hit this endpoint without authenticating with Fugue. To use the /resources endpoint authentication is now required.
2019.08.07¶
Docs site: The Fugue Documentation site has been redesigned, moved to https://docs.fugue.co, and features the following new content:
The visualizer includes security group and subnet labeling within VPCs. This makes it easier to identify which security groups and subnets are associated with a particular VPC, as shown below. To learn more about the visualizer, refer here.
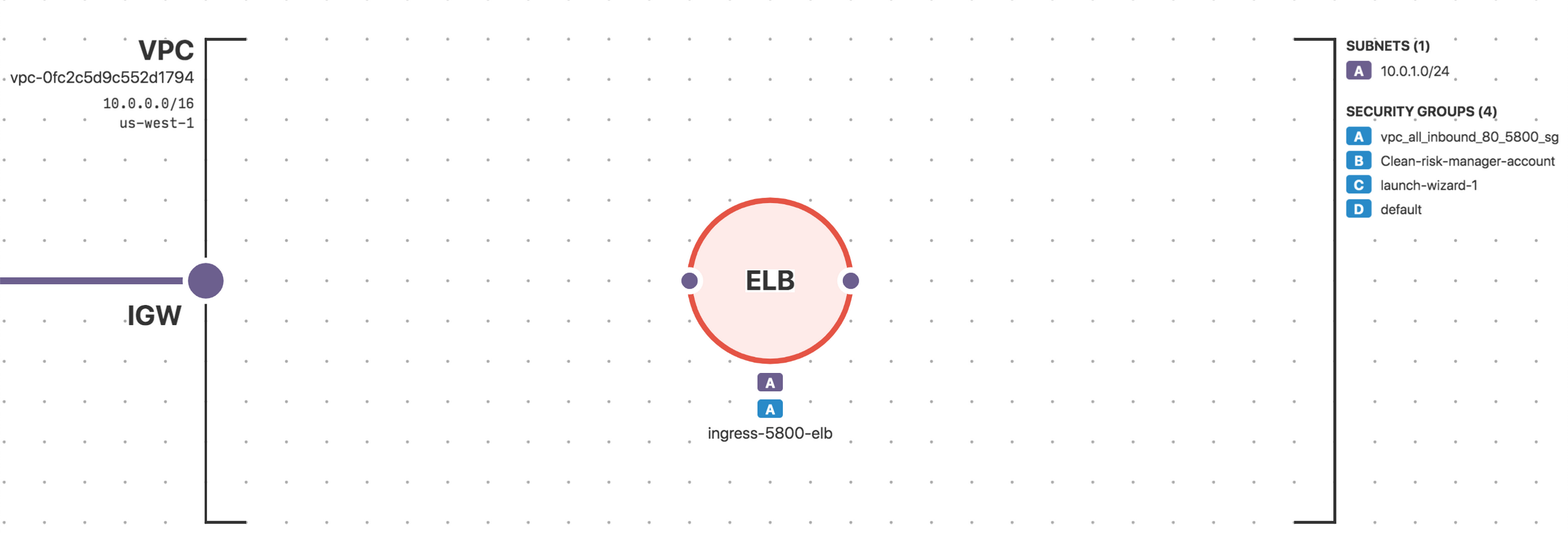
The visualizer “full screen” fills the browser window, rather than the entire screen.
The visualizer supports Azure, as shown below.
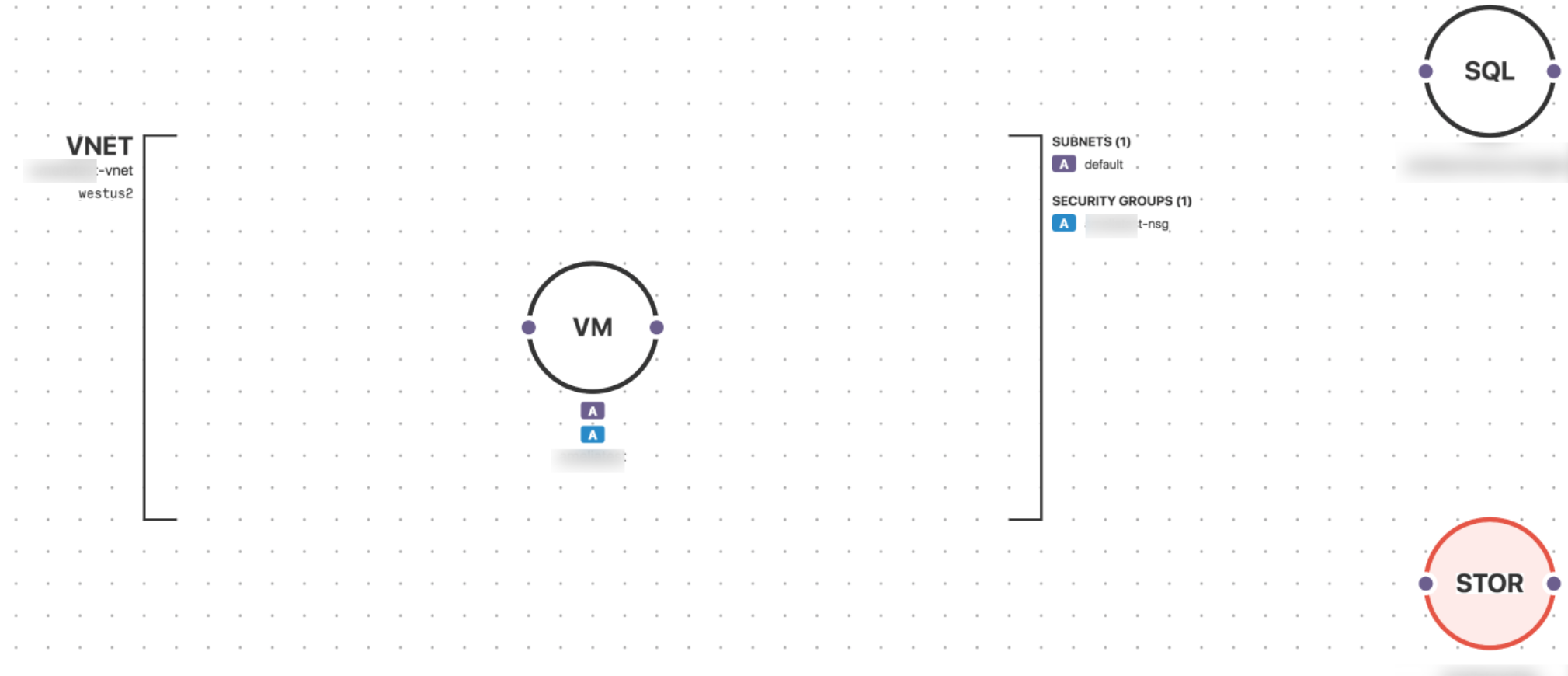
Azure notifications are available to alert on compliance, drift, and baseline enforcement events. To get started using notifications, refer here.
Fixed an issue with the CIS AWS 2-5 rule: “Ensure AWS Config is Enabled in all Regions.”
2019.07.08¶
Visualization: Cloud resource visualization displays resources that are not compliant within an environment, as shown below:
Expanded rule coverage:
IAM root account should not be used. Corresponds to the following compliance controls:
ISO27001_A.6.1.2;ISO27001_A.9.2.3;ISO27001_A.9.4.1
SOC2_CC5.2;SOC2_CC6.1;SOC2_CC6.3
CIS_AWS_1.2.0_1-1
HIPAA_§164.308(a)(1)(ii)(D);HIPAA_§164.308(a)(6)(i);HIPAA_§164.312(b)
GDPR_30-(1)
Ensure multi-factor authentication (MFA) is enabled for all IAM users that have a console password. Corresponds to the following compliance control:
CIS_AWS_1.2.0_1-2
Ensure credentials unused for 90 days or greater are disabled. Corresponds to the following compliance controls:
ISO27001_A.9.2.3;ISO27001_A.9.2.4;ISO27001_A.9.3.1
SOC2_CC6.1;SOC2_CC6.2;SOC2_CC6.3
CIS_AWS_1.2.0_1-3
NIST-800-53_IA-4d;NIST-800-53_IA-4d
HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1):HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1);HIPAA_§164.308(a)(3)(ii)(B),HIPAA_§164.308(a)(3)(ii)(C),HIPAA_§164.308(a)(4)(i),HIPAA_§164.308(a)(4)(ii)(B),HIPAA_§164.308(a)(4)(ii)(C),HIPAA_§164.312(a)(2)(i),HIPAA_§164.312(a)(2)(ii),HIPAA_§164.312(a)(2)(iii),HIPAA_§164.312(d)
PCI_DSS_8.1.4
Ensure access keys are rotated every 90 days or less. Corresponds to the following compliance controls:
ISO27001_A.9.2.3;ISO27001_A.9.2.4;ISO27001_A.9.3.1
SOC2_CC6.1;SOC2_CC6.2;SOC2_CC6.3
CIS_AWS_1.2.0_1-4
NIST-800-53_IA-4d;NIST-800-53_IA-5 (1)(d)
HIPAA_§164.308(a)(5)(ii)(D);HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1);HIPAA_§164.308(a)(3)(ii)(B),HIPAA_§164.308(a)(3)(ii)(C),HIPAA_§164.308(a)(4)(i),HIPAA_§164.308(a)(4)(ii)(B),HIPAA_§164.308(a)(4)(ii)(C),HIPAA_§164.312(a)(2)(i),HIPAA_§164.312(a)(2)(ii),HIPAA_§164.312(a)(2)(iii),HIPAA_§164.312(d)
PCI_DSS_8.2.4
Ensure no root account access key exists. Corresponds to the following compliance controls:
ISO27001_A.9.2.3;ISO27001_A.9.3.1;ISO27001_A.9.4.1
SOC2_CC5.2;SOC2_CC6.1;SOC2_CC6.3
CIS_AWS_1.2.0_1-12
HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1)
PCI_DSS_8.1
Ensure hardware MFA is enabled for the “root” account. Corresponds to the following compliance controls:
ISO27001_A.9.2.3;ISO27001_A.9.3.1;ISO27001_A.9.4.1;ISO27001_A.9.4.1;ISO27001_A.9.4.3
SOC2_CC5.2;SOC2_CC6.1;SOC2_CC6.3
CIS_AWS_1.2.0_1-14
HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1)
Ensure MFA is enabled for the “root” account. Corresponds to the following compliance controls:
SO27001_A.9.2.3;ISO27001_A.9.3.1;ISO27001_A.9.4.1;ISO27001_A.9.4.1;ISO27001_A.9.4.3
SOC2_CC5.2;SOC2_CC6.1;SOC2_CC6.3
CIS_AWS_1.2.0_1-13
NIST-800-53_IA-2 (1)
HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1);HIPAA_§164.308(a)(3)(i);HIPAA_§164.312(a)(1);HIPAA_§164.308(a)(3)(ii)(B),HIPAA_§164.308(a)(3)(ii)(C),HIPAA_§164.308(a)(4)(i),HIPAA_§164.308(a)(4)(ii)(B),HIPAA_§164.308(a)(4)(ii)(C),HIPAA_§164.312(a)(2)(i),HIPAA_§164.312(a)(2)(ii),HIPAA_§164.312(a)(2)(iii),HIPAA_§164.312(d)
PCI_DSS_8.1
Expanded service coverage: Fugue now supports the following resource:
IAM.CredentialReport. To start scanning forIAM.CredentialReport, update your Fugue IAM role to include:
"iam:GenerateCredentialReport",
"iam:GetCredentialReport",
"iam:ListVirtualMFADevices"
Refer to the Service Coverage page to see the full list of supported service coverage. If you have any questions, reach out to support@fugue.co.
Improvements to the Compliance by Resource modal: The compliance controls that fail are displayed under the description of the rule, as shown below:
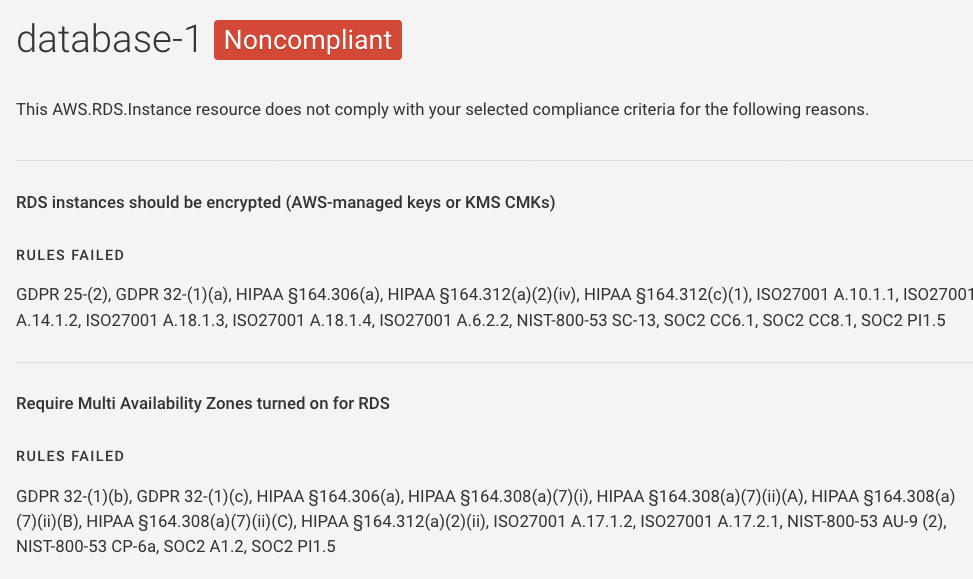
2019.07.03¶
Features¶
Support for Azure: Cloud service coverage is being expanded to include Azure in addition to AWS. This makes Fugue a multi-cloud solution. For setup instructions, see Setup - Azure. For general information, see Azure.
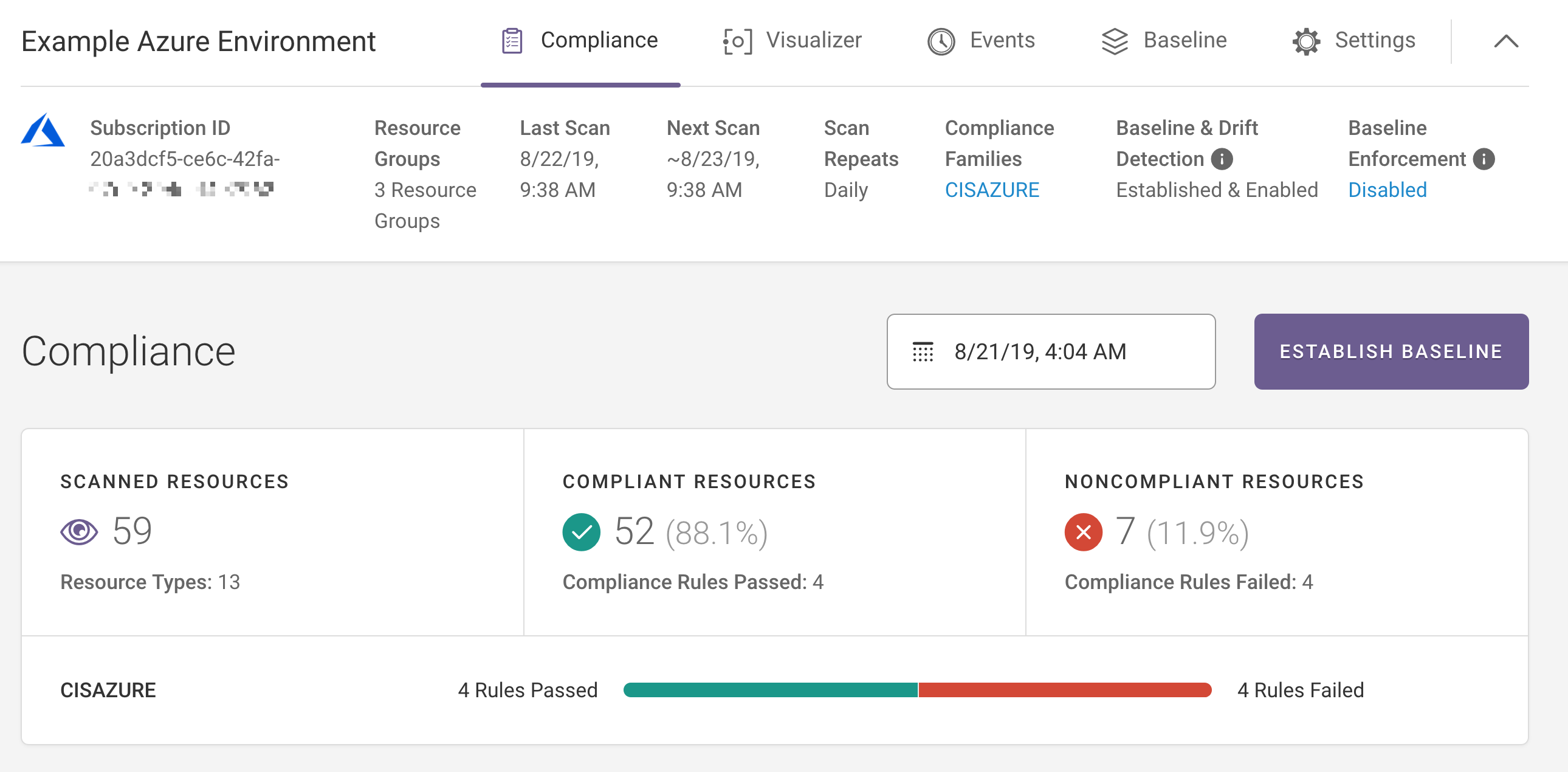
2019.06.26¶
Features¶
Notifications: Fugue offers notifications for compliance, drift, and baseline enforcement events within environments, allowing you to be alerted to infrastructure changes detected during a scan without having to log into Fugue.
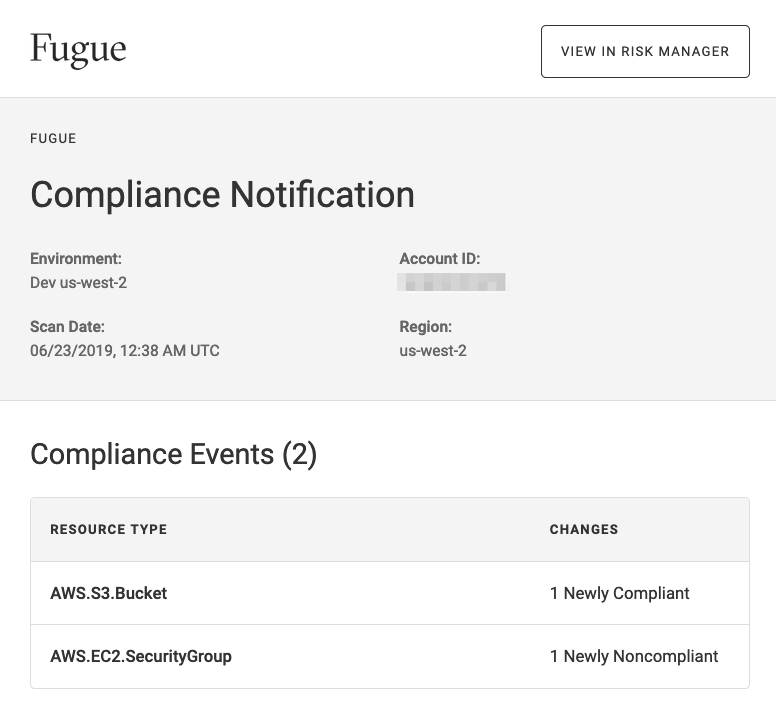
Within Organization Settings, you may add notifications and choose to be notified by email, Amazon SNS topic, or both. By using the SNS integration, you can connect Fugue notifications to third-party tools such as Slack.
Full screen visualizer: You can expand cloud resource visualization to a full screen view. This allows you to better interact with and view your infrastructure. Clicking the
fbutton, as highlighted below, opens the full screen visualization experience.
Here’s an example of full screen mode:
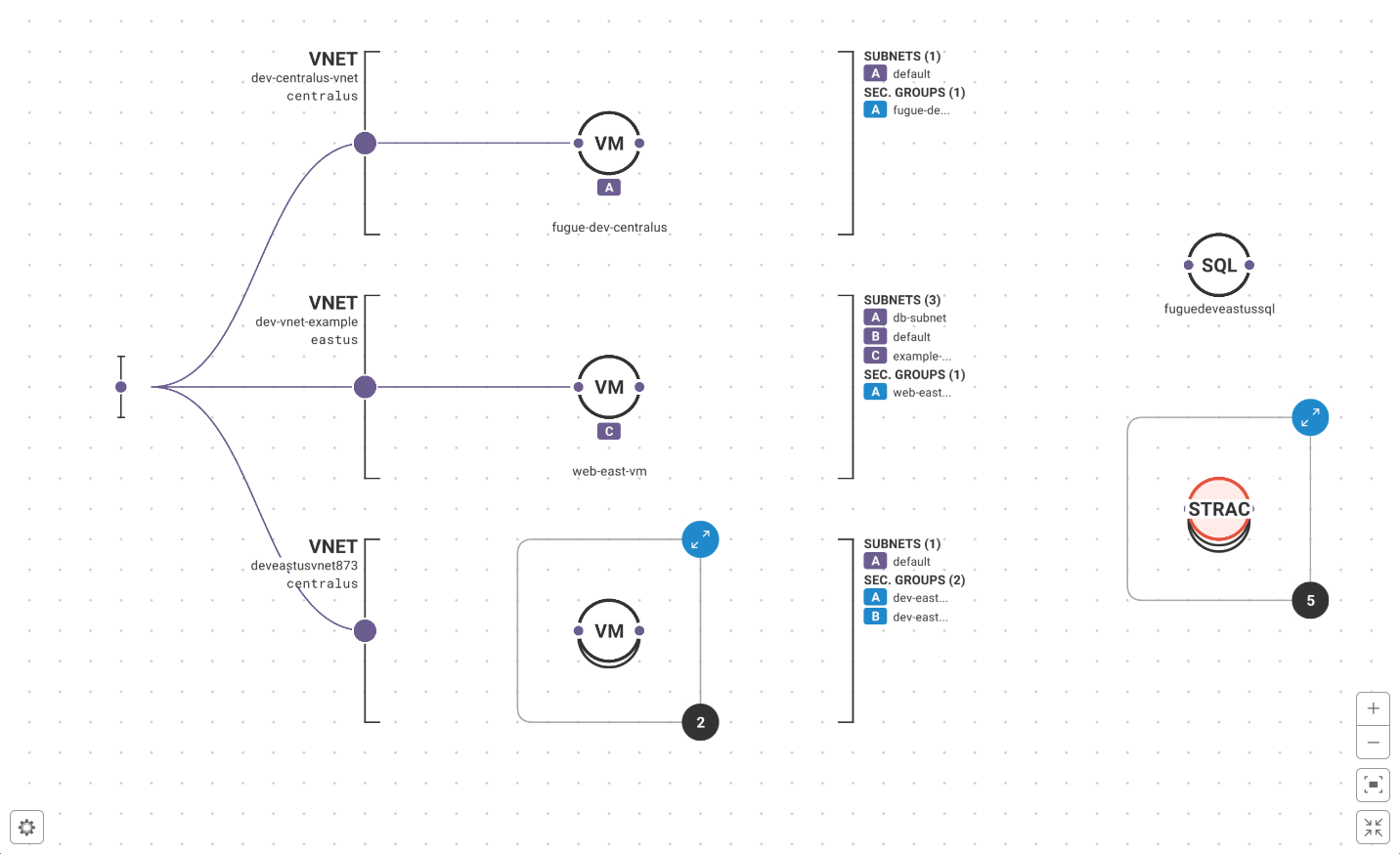
Updates to the “Create Environment” workflow: The “create environment” workflow has been updated as follows. In the first step, you enter your environment’s name and select the cloud service provider:
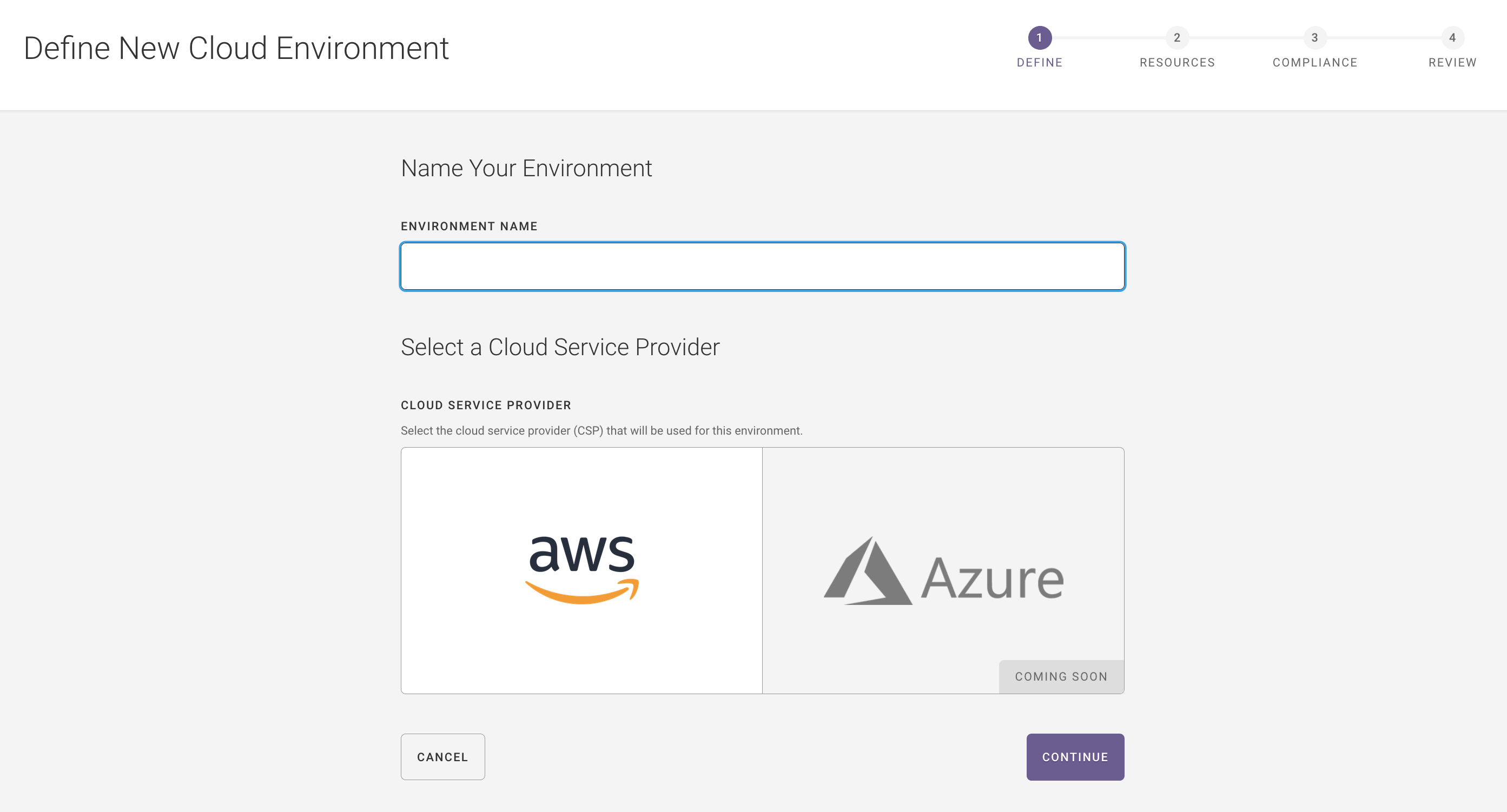
In the second step, you select the region and resource types, and then enter the AWS IAM role ARN:
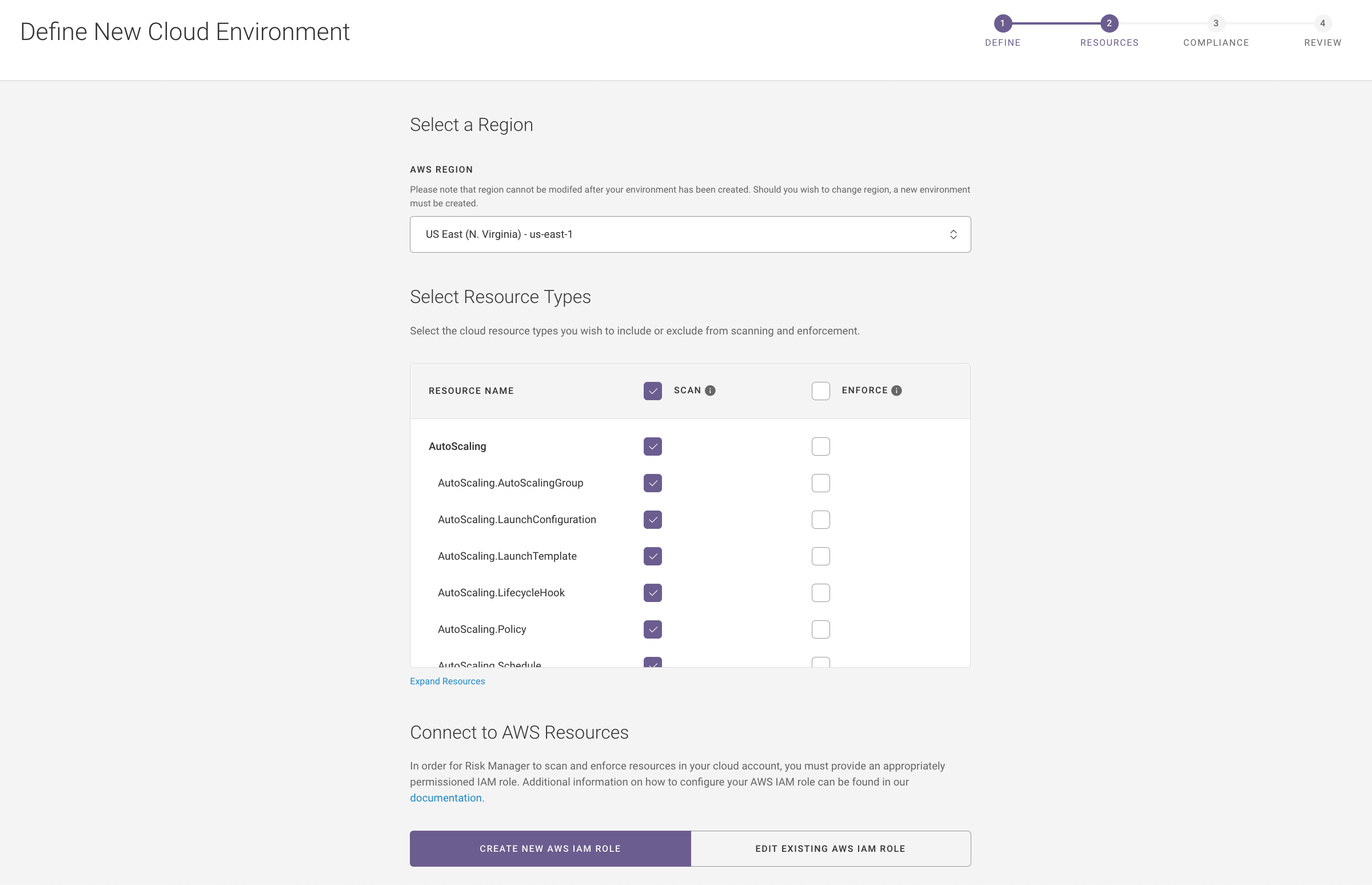
In the third step, you select the compliance libraries you want Fugue to use to assess your infrastructure:
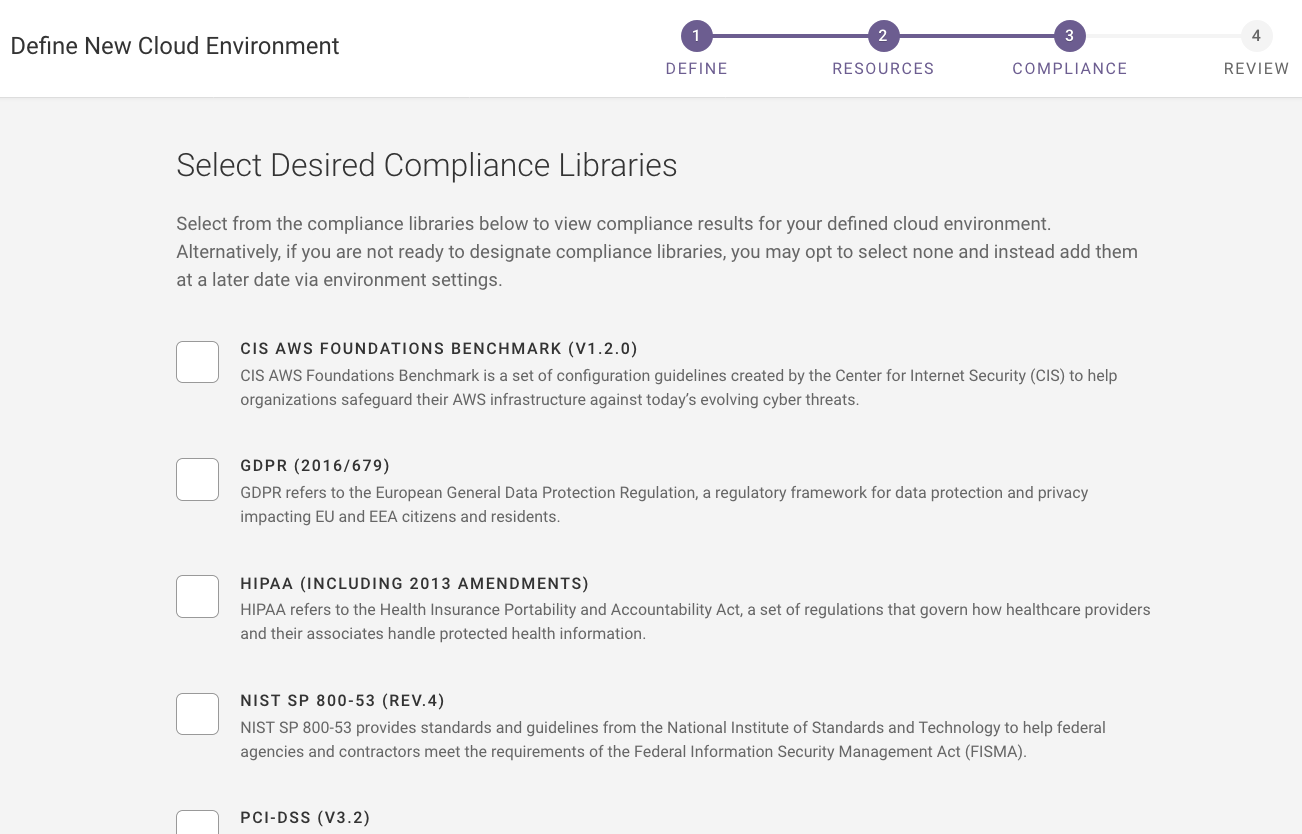
In the fourth step, you can view a summary of the environment name, region, AWS IAM role ARN, the selected compliance standards, and the selected resource types to scan and enforce, as shown below:
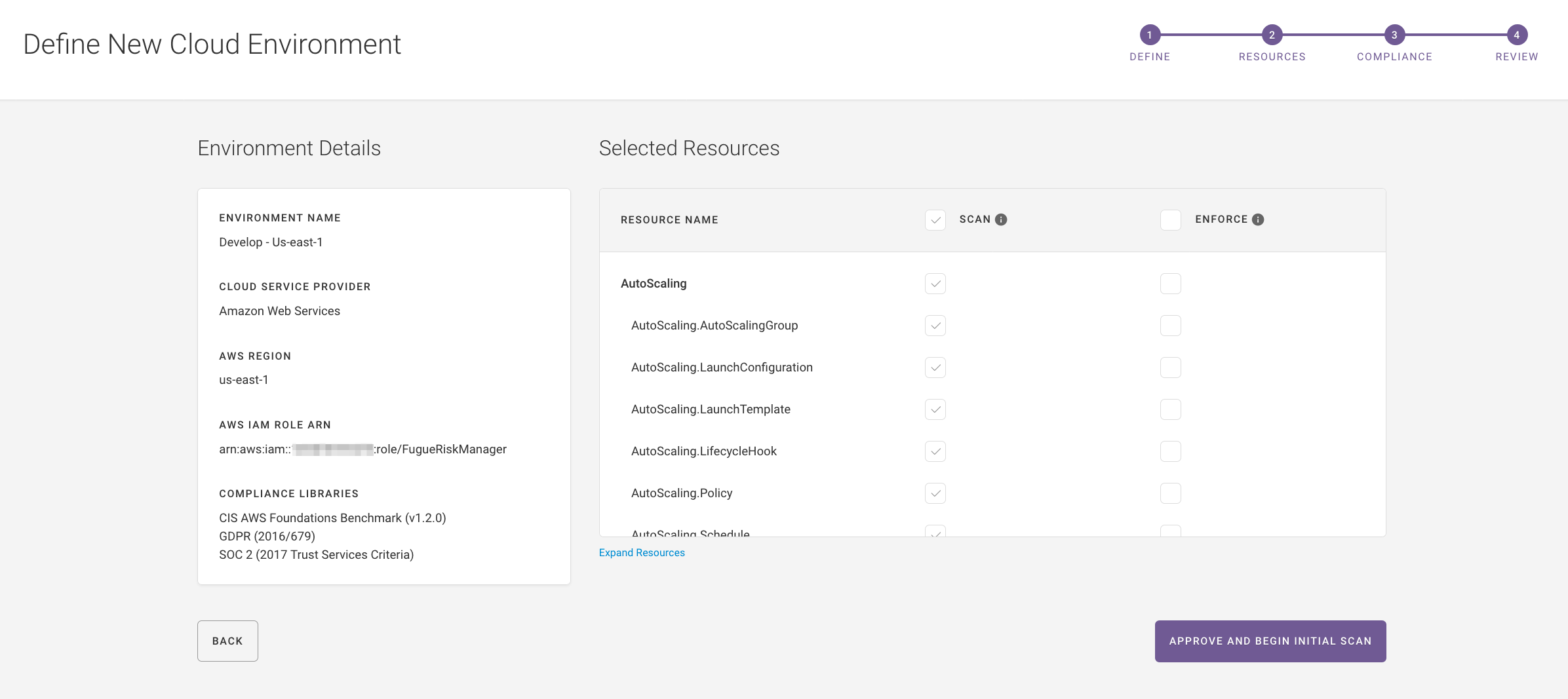
For full setup instructions, see Setup.
2019.06.10¶
Fugue Risk Manager is now simply Fugue.
Features¶
AWS GovCloud regions: Fugue now supports AWS GovCloud regions via the Fugue application and API. All existing functionality for other commercial AWS regions is supported for AWS GovCloud regions including:
Assess AWS GovCloud regions for compliance violations against the following compliance standards: CIS AWS, NIST SP 800-53, PCI-DSS, HIPAA, GDPR, SOC 2, and ISO 27001.
Enable configuration drift detection and optionally, enforcement on baselines.
Cloud resource visualization: Fugue’s new cloud resource visualization feature creates detailed, interactive diagrams of your cloud resources. This allows you to quickly visualize cloud infrastructure configurations and relationships without having to create diagrams by hand, which can be a painstaking and error-prone process. Diagrams are generated and updated automatically. You can zoom in or out to more closely inspect the resources:
Improved compliance control messages: The compliance control message contains additional information about what caused a resource to be noncompliant and violate the control, as shown below.
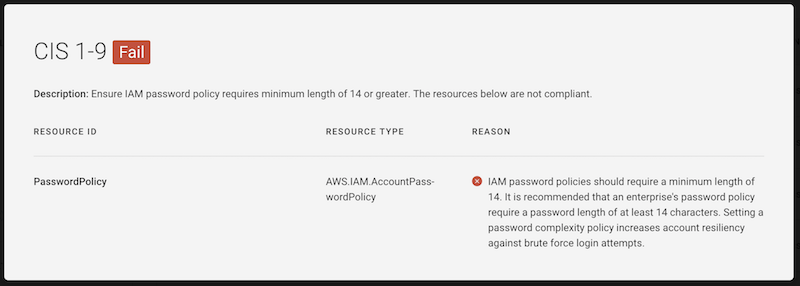
2019.05.29¶
Features¶
Added service coverage support for
ElastiCache.Cluster,ElastiCache.ParameterGroup, andElastiCache.ReplicationGroupresources.To scan for ElastiCache clusters, parameter groups, and replication groups, update your Fugue IAM role to include the following permissions:
"elasticache:DescribeCacheClusters",
"elasticache:DescribeCacheParameterGroups",
"elasticache:DescribeCacheParameters",
"elasticache:DescribeReplicationGroups",
"elasticache:ListTagsForResource"
Note
When ElastiCache.Cluster resources belong to an ElastiCache.ReplicationGroup, the clusters themselves are not scanned but the replication group is. The replication group manages the clusters and contains all of the relevant settings, so there is no need to scan the clusters individually.
In contrast, ElastiCache clusters that do not belong to a replication group are scanned individually.
Refer to the Service Coverage page to see the full list of supported services. If you have any questions, reach out to support@fugue.co.
Created the Fugue API Reference, which contains Swagger documentation and examples.
2019.05.09¶
Features¶
Added service coverage support for Amazon S3 bucket ACLs. The new functionality will provide more protection for S3 buckets.
Users who have enabled scanning on S3 buckets must update their Fugue IAM role to include the following permission, or scans involving S3 buckets will be incomplete:
"s3:GetBucketACL"
If you have any questions, reach out to support@fugue.co.
Added service coverage support for SNS subscriptions and CloudWatch Metric Alarms.
To scan for SNS subscriptions and CloudWatch Metric Alarms, update your Fugue IAM role to include the following permissions:
"cloudwatch:DescribeAlarms",
"sns:GetSubscriptionAttributes",
"sns:ListSubscriptions"
Refer to the Service Coverage page to see the full list of supported services. If you have any questions, reach out to support@fugue.co.
Added support for SOC 2 and ISO 27001 compliance standards.
SOC 2 governance applies to organizations storing customer data in the cloud.
ISO 27001 is a specification for an information security management system that includes controls for information risk management processes.
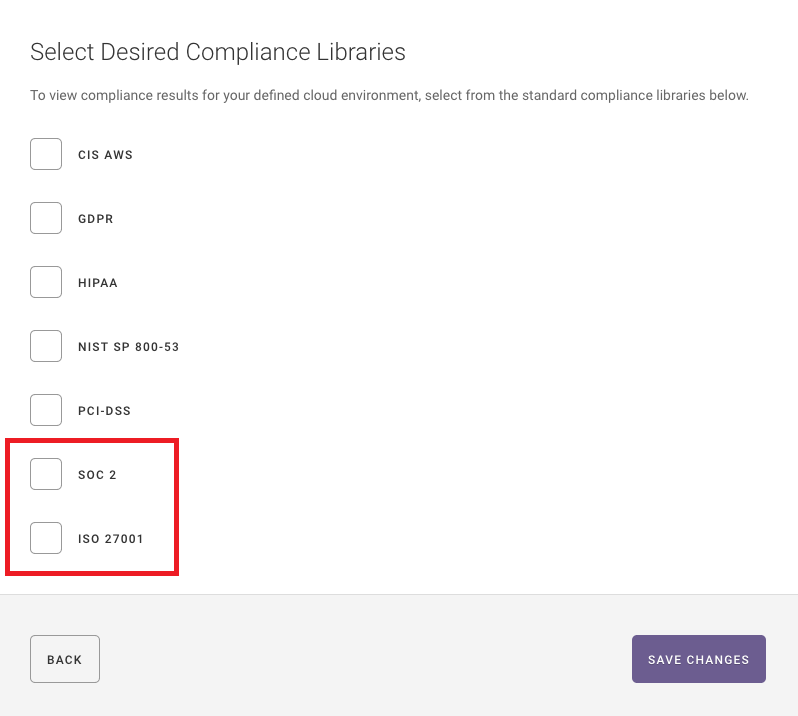
Bug Fixes and Improvements¶
Fugue automatically logs users out of the application every 24 hoursinstead of once a month.
Other bug fixes and improvements.
2019.04.25¶
Features¶
Improved API Clients table to display the client secret age and last activity of the API client. In the previously released API Clients table, the client secret’s age and the last activity of the client secret did not display within the table. It is important to know your client secret’s age so you can properly rotate it according to your organization’s security policy. Additionally, displaying the last activity for the client secret allows you to revoke and/or delete client secrets that are no longer in use. For more information, see the API page.
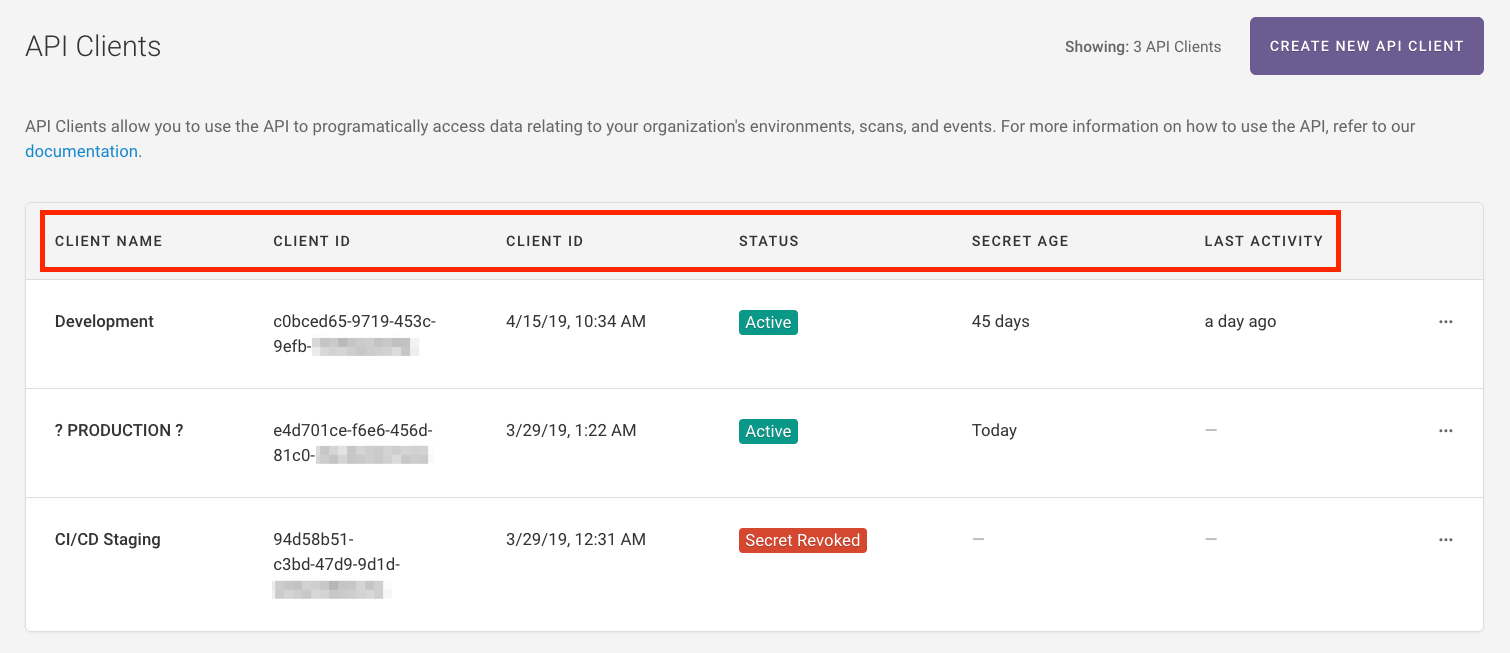
Improved page load times of the environment list and environment detail pages
Improved link to “Edit IAM Role in AWS Console” to point directly to list of roles in the console
Bug Fixes¶
Fixed an issue where the list compliance results by rule API endpoint would return no results when no compliance family was selected
Various scan fixes
2019.03.28¶
Features¶
The API has 4 main areas of functionality:
Create, update, and delete environments
Run scans on demand or on a specific schedule
Retrieve scan results by compliance rule or resource type
Retrieve drift and enforcement events
For more information, refer to the API user guide and the API documentation.
Additional compliance checks for PCI and HIPAA have been added.
The new PCI compliance rules include:
AWS Glacier requires that AWS S3 bucket policy only accepts HTTPS. This applies to PCI_DSS_4.1.
Point in time recovery is enabled on the AWS Dynamo database. This applies to PCI_DSS_3.1.
Users specified backup retention periods for AWS RDS. This applies to PCI_DSS_3.1.
Any security group for a private subnet does not have CIDR ingress from 0.0.0.0/0. This applies to PCI_1.2.1 and PCI_1.3.1.
The new HIPAA compliance rules include:
AWS Glacier requires that AWS S3 bucket policy only accepts HTTPS.
Enable transport encryption for AWS ElastiCache.
AWS service coverage has been expanded to support SNS Topics, WAF Web ACLs, and CloudFront Distributions. If you want to scan for these newly released services, you will want to update your IAM Role to include:
"cloudfront:GetDistribution",
"cloudfront:ListDistributions",
"cloudfront:ListTagsForResource",
"sns:GetTopicAttributes",
"sns:ListTopics",
"waf:GetWebACL",
"waf:ListWebACLs"
Refer to the Service Coverage page to see the full list of supported service coverage. If you have any questions, reach out to support@fugue.co.
2019.03.15¶
Features¶
The compliance report email allows you to view the compliance state of your environment without having to log into Fugue.
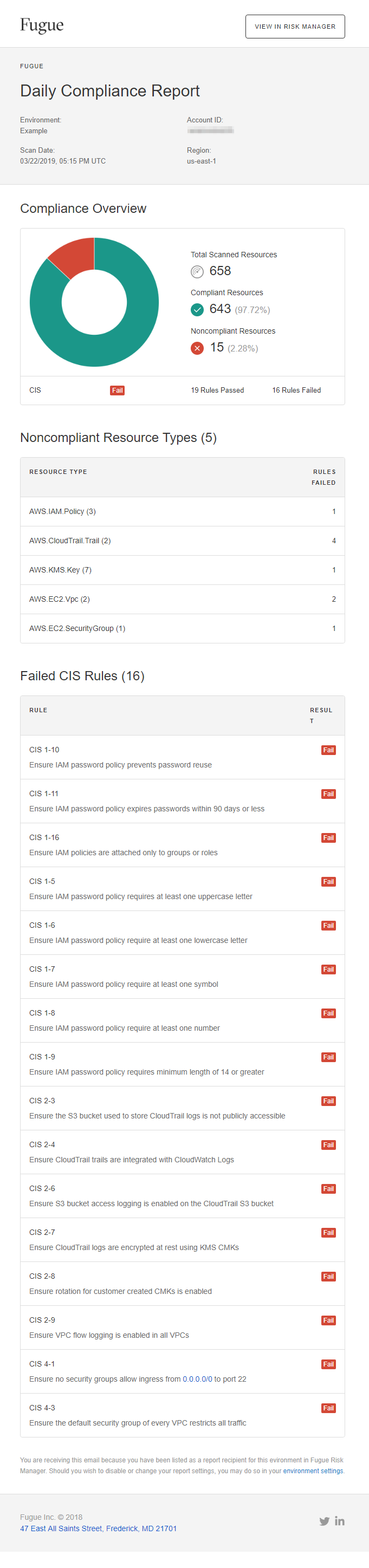
Additional Payment Card Industry (PCI) rules have been added within Fugue. These rules include:
PCI DSS 8.1.4, which requires that users have a password that contains at least 7 characters and includes both alphabetic and numeric characters.
PCI DSS 8.2.5, which requires users do not submit a new password/phrase that is the same as any of the last four passwords/phrases they used.
PCI DSS 4.1, which requires that AWS CloudWatch metric filter alarms is via SQS and not via HTTPS.
PCI DSS 8.2.4, which requires users to change their passwords/phrases at least once every 90 days.
PCI DSS 10.5.3 and PCI DSS 10.7, which requires that versioning and lifecycle policy be enabled for Amazon S3 buckets.
Bug Fixes¶
Addressed an issue where clicking outside a modal window failed to close it.
Addressed an issue where selecting Edit Environment Setting on the Environment landing page failed to redirect users to the Edit Environment Settings modal window.
Addressed an issue where selecting a resource that was not included in your IAM role ARN would cause the scan to fail. Now, the scan completes and the resources not included in your role ARN are listed in a message.
2019.02.25¶
The multi-user feature allows users to invite other parties in their organization to access and collaborate on the same Fugue environments.
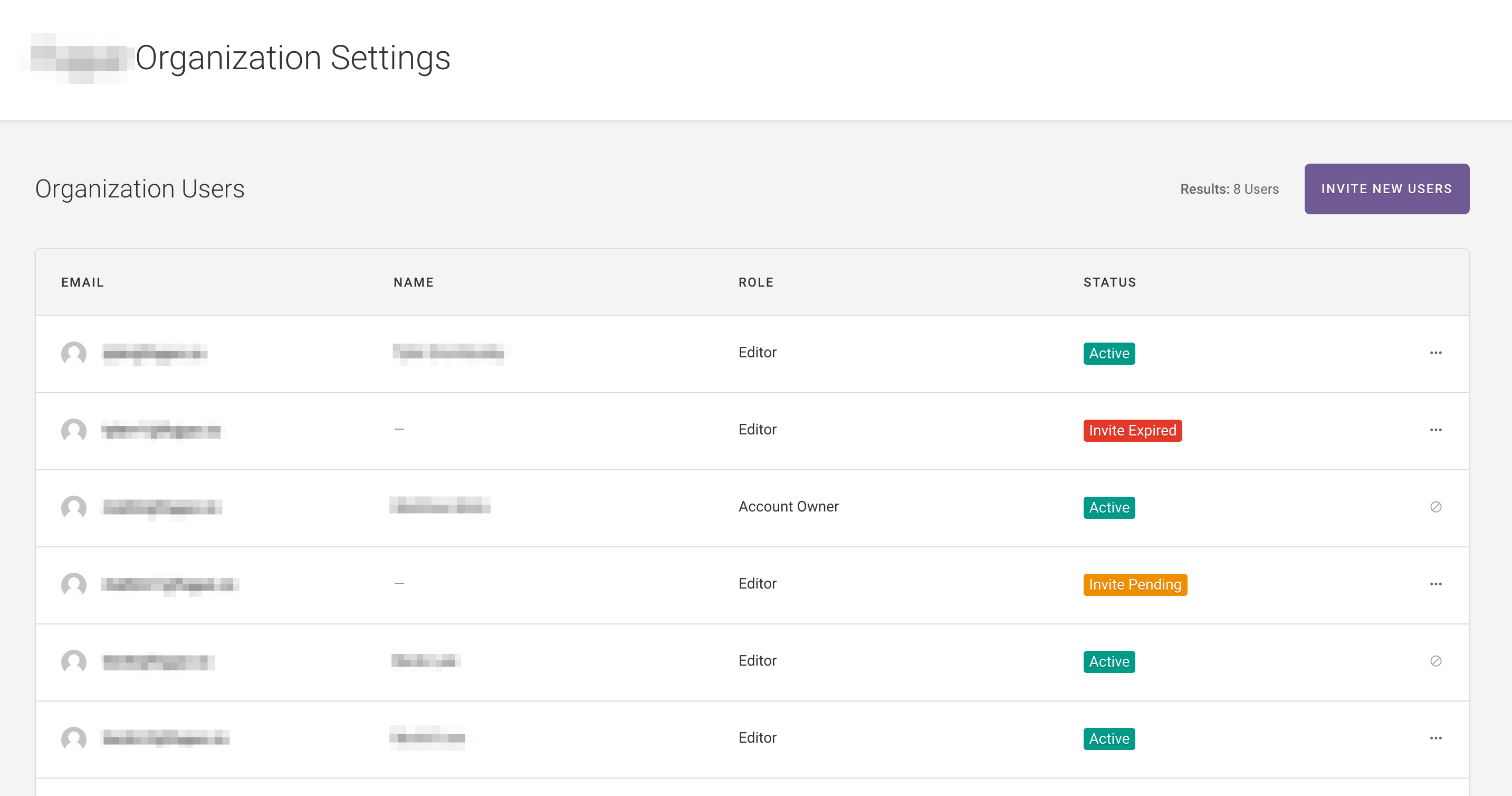
2019.02.12¶
PCI DSS rules are now supported within Fugue.
Added service coverage support for CloudTrail, Config, SQS, VPC, and KMS.
2019.01.28¶
Users can select the specific resources that they want to manage within Fugue. Compliance scanning, drift detection, and baseline enforcement only occur on the selected resources. For details, see Setup.
Rules that pertain to resources that Fugue isn’t permitted to scan now display with an “Unknown” label.
Service coverage has been expanded to support RDS.
Users can see when their next scan is scheduled to start.
2018.11.26¶
Features¶
Scan cloud environments for risks and generate risk reports¶
Use Fugue to scan your cloud environment and produce comprehensive reports identifying compliance violations in your cloud infrastructure. Use this report in conjunction with an auditor to address these violations. Once all violations are addressed, the security teams can demonstrate Fugue’s functionality to both the CISO and the auditor. Fugue supports scanning and identifying compliance violations for the following compliance standards or benchmarks: CIS, NIST, HIPAA, and GDPR. The report also provides a snapshot of your infrastructure at any point in time.
Scan cloud environments for drift based on the declared baseline¶
Once you work with an auditor to address the compliance violations in your cloud infrastructure, you can establish a baseline. This lets Fugue know that this is the declared baseline and Fugue scans the environment for any changes to this declared baseline. If a change is detected, which is also known as drift, Fugue notifies you via the Drift Detection page.This allows you to proactively review and fix drift in your cloud environment. Use this drift report to show your CISO, security team, and auditor that Fugue detected the drift and enabled you to manually correct the issue. To learn more about enabling drift detection with Fugue, refer to details in Configuration.
Enable baseline enforcement on resources in cloud environments¶
Once you establish a baseline, you can enable self-healing, which is known as baseline enforcement within Fugue. When baseline enforcement is enabled, Fugue scans your environment and if any resources in your baseline are modified, they are reverted back to the baseline state. You can use the Drift report to show your CISO, security team, and auditor that drift occurred, and it was reverted back to the baseline state. To learn more about enabling baseline enforcement, refer to details in Configuration.