Compliance¶
Note
Fugue’s infrastructure as code (IaC) security features for repository environments are now available in closed beta. Fugue IaC security integrates with Regula to scan code files locally and in CI/CD pipelines.
Note
For instructions on manually bringing noncompliant resources back into compliance, see the Rule Remediation Steps.
Fugue checks the resources in your environment for compliance based on the compliance families you select:
AWS Well-Architected Framework
CIS AWS Foundations Benchmark
CIS Azure Foundations Benchmark
CIS Controls
CIS Docker Benchmark
CIS Google Foundations Benchmark
CIS Kubernetes (limited beta: Only supported for Repository environments)
CSA Cloud Controls Matrix
Fugue Best Practices
GDPR
HIPAA
ISO 27001
NIST 800-53
PCI DSS
SOC 2
Fugue also supports custom rules and custom families. Custom rules are defined in Rego, the Open Policy Agent query language. Custom families can include custom rules or Fugue-defined rules. See our note about how deleted rules affect compliance.
You may select any combination of families, including none if you prefer. To change the selected families, see the FAQ.
Note
A control is a specific recommendation within a compliance family defined by the standards-setting organization. In most Fugue-defined families, rules associated with a given family are also associated with controls, though custom families do not support controls. Example: PCI DSS (v3.2.1) 1.3.5. A rule checks cloud infrastructure configurations to determine whether a resource, region, or account complies with a specific policy. Example: “VPC flow logging should be enabled.” To learn more, jump ahead to Compliance Concepts.
Your overall compliance state for each environment is shown on the Environment Overview page shown when you log in:
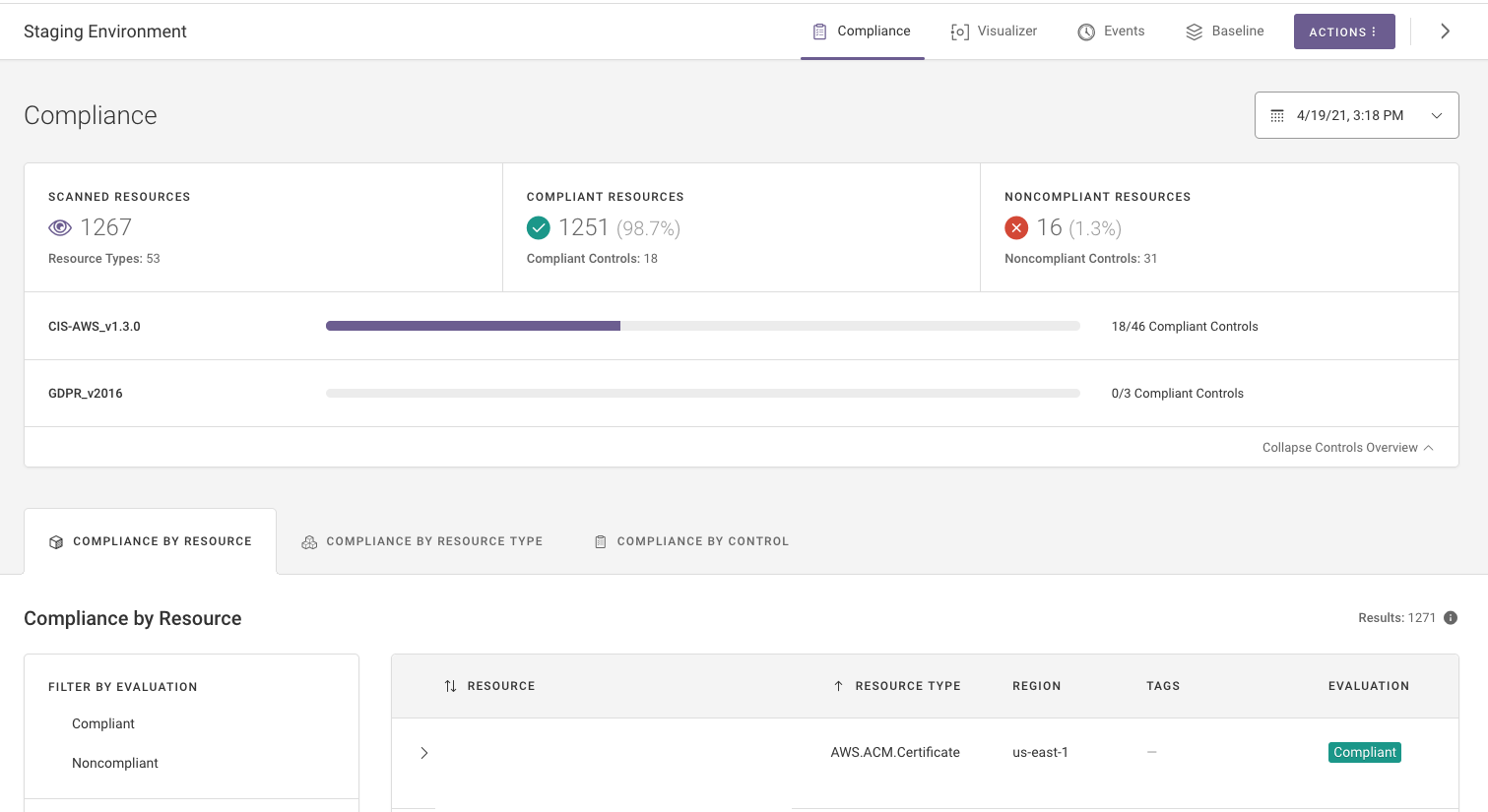
Select the name of an environment to see its dashboard. You’re taken to the Compliance page, which shows overall and detailed compliance state:
Compliance Concepts¶
What is a rule?¶
A rule checks resource configurations to determine whether a resource, region, or account complies with a specific policy. For example, the rule “IAM password policies should require a minimum length of 14 characters” checks whether an AWS account or IaC template has an appropriately complex IAM password policy configured. The rule “Virtual Machine data disks (non-boot volumes) should be encrypted” checks whether an Azure data disk resource has encryption enabled. Rules can either be Fugue-defined, or users can write custom rules. A rule is associated with one or more families, and in the case of most Fugue-defined families, a rule is associated with one or more controls.
What is a family?¶
A family (synonymous with compliance family) is a group of rules. Families can be user-defined (custom families) or Fugue-defined. Fugue-defined families (except the default Custom Rules family) also contain controls. Custom families do not contain any controls.
What is a control?¶
A control (synonymous with compliance control) is a specific recommendation within a compliance family that defines a process, policy, or approach. For example, PCI DSS (v3.2.1) 1.3.5, “Permit only ‘established’ connections into the network,” is a control. A control is associated with a single family, and can be associated with one or more rules.
How do rules, families, and controls relate to each other?¶
A family contains one or more rules. Each rule can map to one or more controls in the family, and vice versa. Rules can belong to multiple families. For example:
The control PCI DSS (v3.2.1) 1.3.5, “Permit only ‘established’ connections into the network,” maps to the PCI DSS (v3.2.1) family, and to these rules:
“VPC flow logging should be enabled”
“VPC default security group should restrict all traffic”
and others
The rule “VPC flow logging should be enabled” maps to these families and controls:
PCI DSS (v3.2.1) 1.3.5, “Permit only ‘established’ connections into the network”
ISO 27001 (v2013) A.12.1.3, “The use of resources shall be monitored, tuned and projections made of future capacity requirements to ensure the required system performance”
and others
Some families are more prescriptive than others. For example, the CIS Foundations Benchmark families recommend very specific configurations, and therefore a CIS Foundations Benchmark control maps to a single rule. In contrast, SOC 2 (v2017) controls are much broader in scope and map to many rules (and vice versa), impacting different AWS, Azure, and Google resource types.
What is a rule result?¶
A rule result is determined by evaluating a rule on a specific resource, region, or account, and it has one of the following values:
Pass: The resource meets the rule’s set of conditions
Fail: The resource does not meet the rule’s set of conditions or a required resource is missing
Unknown: An error prevented the rule from being evaluated
Waived: The result was waived for this rule and resource
The relationships between a rule and the underlying resources (or accounts, regions) that are being evaluated form the core of higher-level compliance calculations such as resource evaluations and control evaluations. In both cases, values are determined from the underlying rule results.
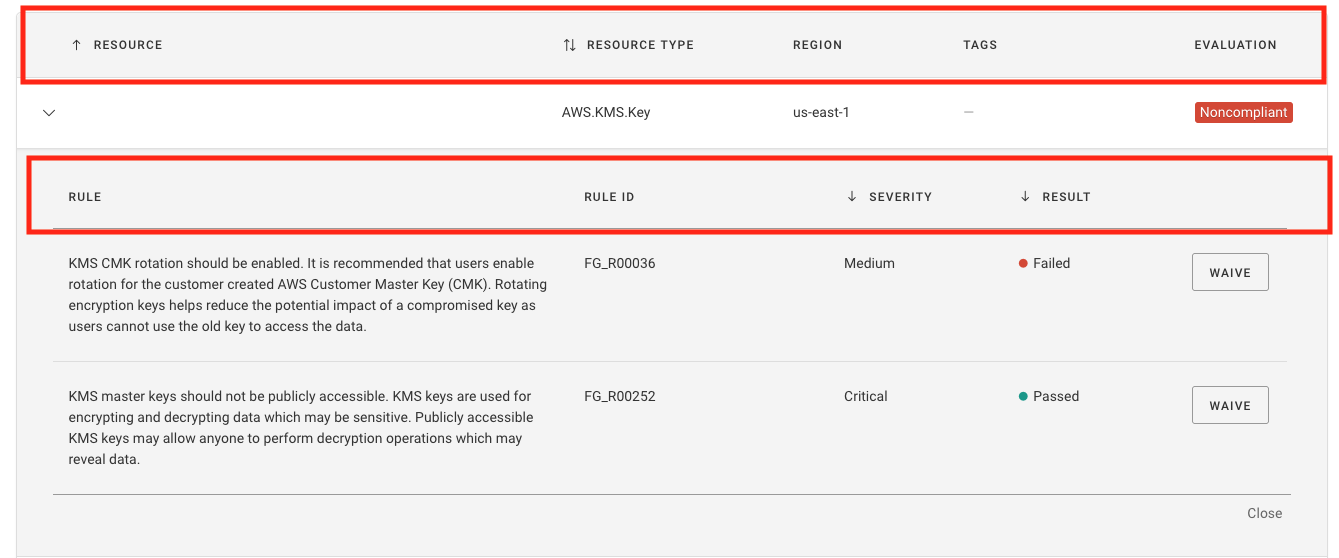
You can view results for all rules applied to a resource by selecting the resource on the Compliance by Resource page:
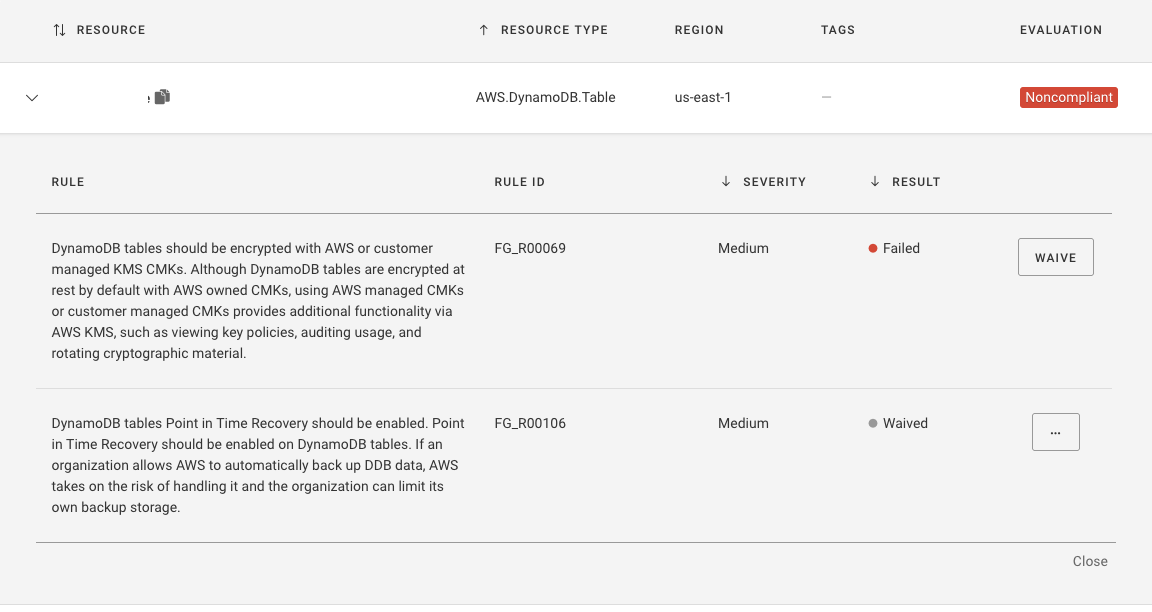
Above, the resource fugue-bucket-example has one Failed, one Passed, and one Waived rule result.
What is a resource evaluation?¶
A resource evaluation is a compliance value for a resource based on the rule results for all applicable rules. If the resource fails any applicable rule (e.g., if there is a single rule result with a “fail” value), the resource evaluation is noncompliant. If the resource passes all applicable rules (e.g., there are no rule results with a “fail” value), the resource is compliant.
A resource evaluation may be different for a given resource depending on which rules are applied.
For example, an Amazon S3 bucket might pass all the rules associated with SOC 2 and therefore be compliant in that context. On the other hand, when evaluated against all applicable rules in an environment (e.g., rules mapping to other compliance families), it might have one or more “fail” rule results and therefore be noncompliant.
Resource evaluation values¶
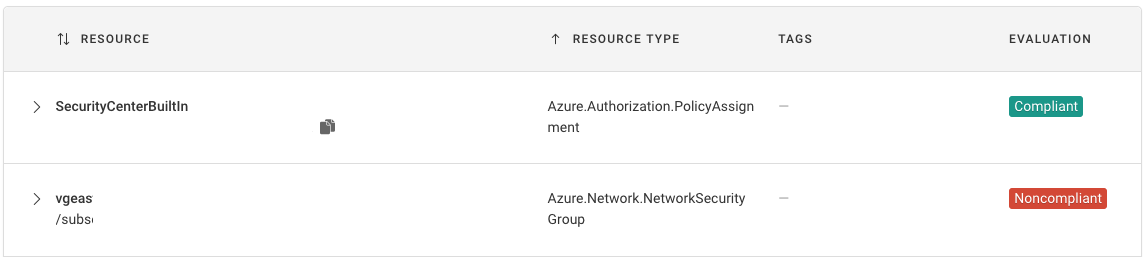
There are two outcomes for resource evaluations, viewable on the Compliance by Resource page:
Compliant: The resource passes all applicable rules.
Noncompliant: The resource fails one or more applicable rules.
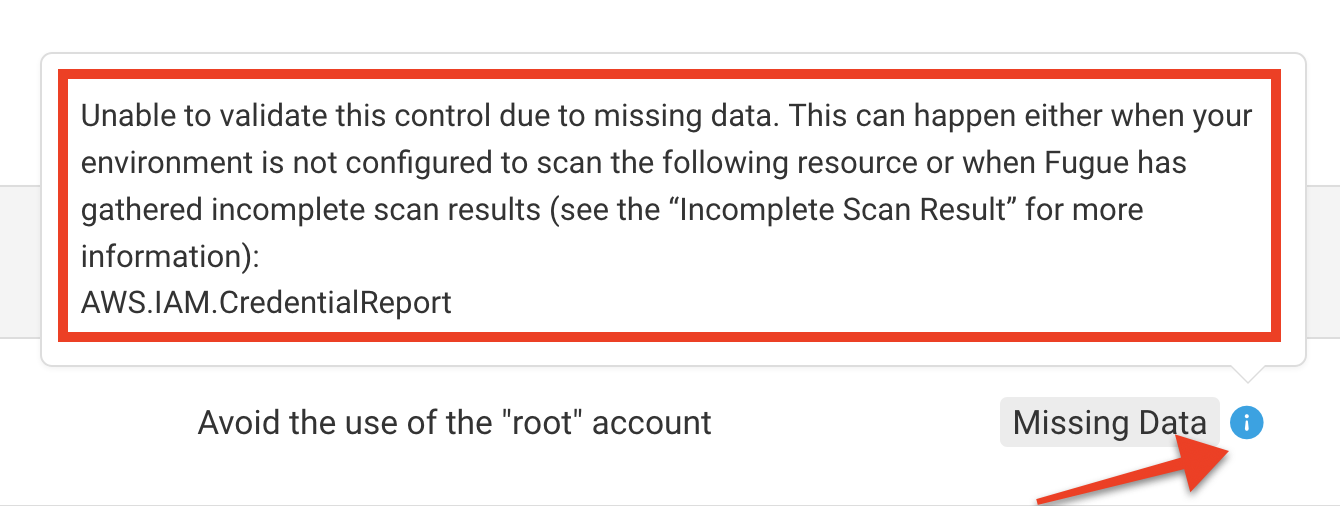
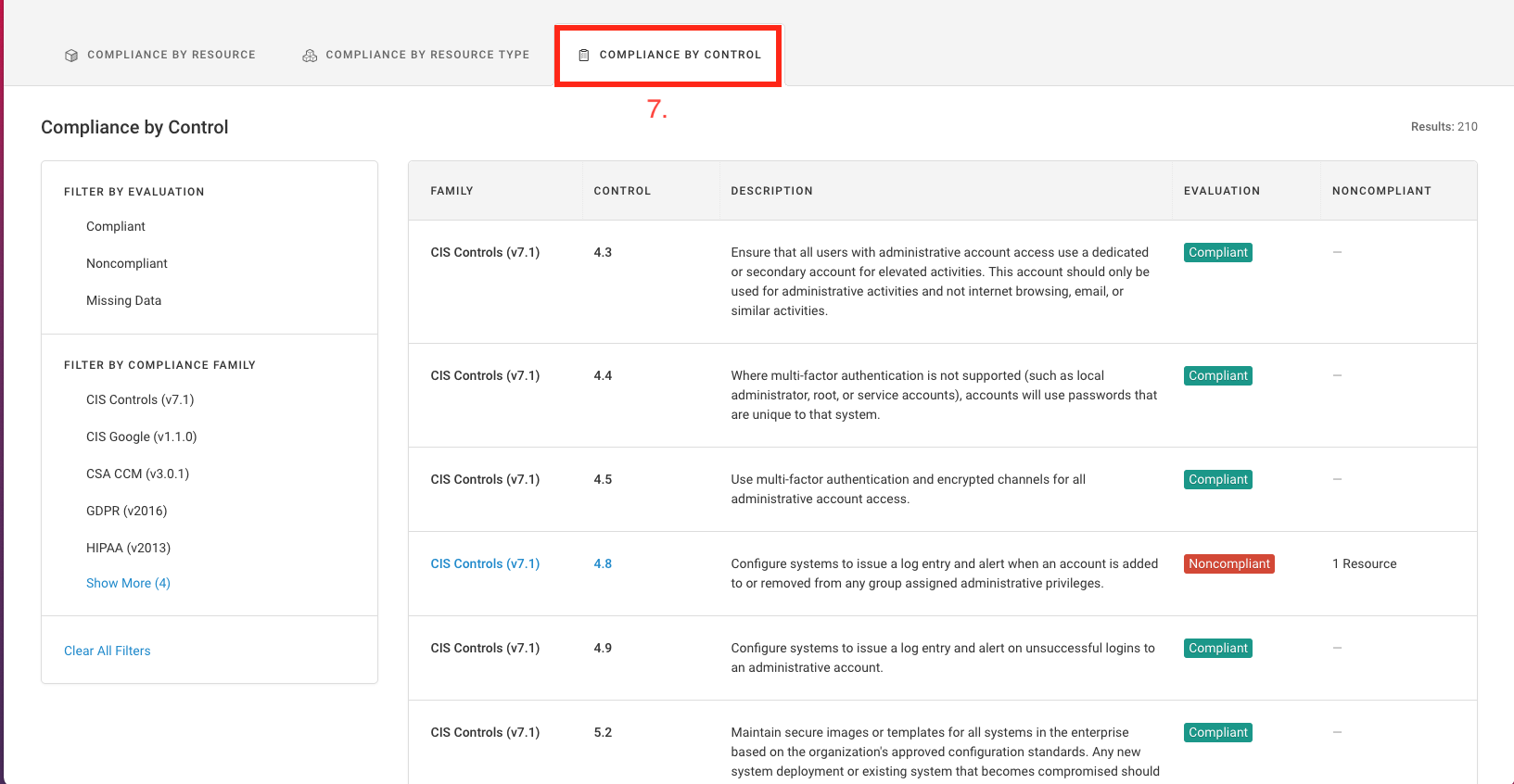
What is a control evaluation?¶
A control evaluation is the compliance value of a control based on the results of all applicable rules. If any resource fails any rule that maps to a control (e.g., if there is a single rule result with a “fail” value), the control is noncompliant. If all applicable resources pass all the rules that map to a control (e.g., there are no rule results with a “fail” value), the control is compliant. If the control can’t be assessed because a required resource doesn’t exist or Fugue lacks permission to assess it, the control’s value is Missing Data. Note that “missing data” is called Unknown in the API.
For example, if PCI DSS (v3.2.1) was selected for an environment, an Amazon VPC without a flow log could pass the rule “VPC default security group should restrict all traffic” but fail the rule “VPC flow logs should be enabled.” Since both rules map to the control PCI DSS (v3.2.1) 1.3.5, “Permit only ‘established’ connections into the network,” the control is noncompliant.
Control evaluation values¶
There are three outcomes for control evaluations, viewable on the Compliance by Control page:
- Compliant
All resources pass the control’s underlying rules.
- Noncompliant
One or more resources fails one or more of the control’s underlying rules.
- Missing Data (labeled
Unknownin the API) A control can’t be assessed because it requires a specific resource, but the resource doesn’t exist or Fugue lacks the necessary permissions to assess it.
You can hover over the i symbol next to the Missing Data label to see which resources are required:
Rule Severity Definitions¶
Rule severity establishes the level of risk posed by a misconfiguration to the security posture of your runtime or IaC resources.
Critical: A misconfiguration that directly exposes infrastructure and data to public access or enables attacks to take control of infrastructure via privilege escalation.
Critical examples:
IAM root user access key should not exist
SQS access policies should not have global
"*.*"accessS3 bucket ACLs should not have public access on S3 buckets that store CloudTrail log files
High: A misconfiguration that may expose information to public access, such as overly permissive security group rules or unencrypted data.
High examples:
IAM should have virtual MFA enabled for the root account
EBS volume encryption should be enabled
VPC security group rules should not permit ingress from ‘0.0.0.0/0’ to TCP/UDP port 22 (SSH)
Medium: A misconfiguration that may not lead to data or infrastructure compromise but represents gaps in security posture such as lack of logging or monitoring that will impair investigation efforts.
Medium examples:
IAM password policies should prevent reuse of previously used passwords
VPC flow logging should be enabled
S3 bucket versioning and lifecycle policies should be enabled
Low: A misconfiguration that may violate security best practices, but is unlikely to affect your infrastructure and data or ability to respond to issues.
Low examples:
IAM policies should not be attached to users
Ensure a support role has been created to manage incidents with AWS Support
RDS instances should have FedRAMP approved database engines
Informational: A misconfiguration that is not security-related but may impact operational excellence or cost optimization.
Fugue Best Practices¶
Fugue offers its own compliance family, Fugue Best Practices. The Fugue Best Practices Framework complements the CIS Benchmarks by providing guidance and recommendations to secure cloud resources against advanced misconfiguration exploits. To learn how to enable Fugue Best Practices (and other compliance families), see the FAQ.
Browsing the Data¶
The main elements of the Compliance page include:
The Environment Summary¶
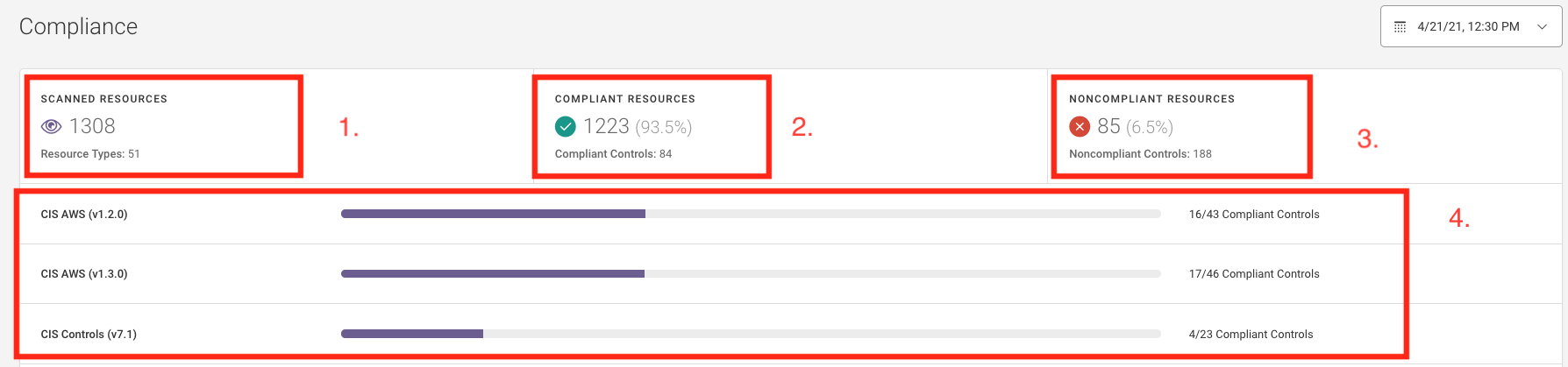
Scanned resources shows the total number of resources that were scanned.
Compliant resources shows the total number of resources that are compliant based on the families you’ve selected.
Noncompliant resources shows the number of resources that are noncompliant based on the families you’ve selected.
Each compliance family shows how many of its controls are compliant.
The Compliance Tabs¶
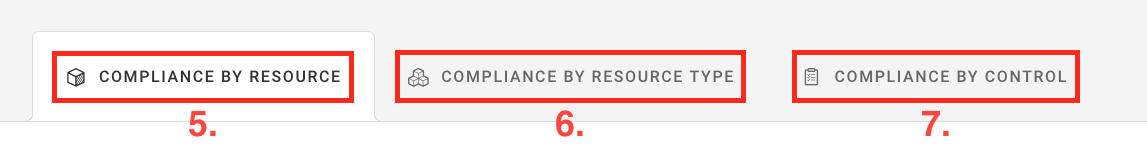
There are three Compliance tabs:
Note
Custom families do not return results on the Compliance by Resource Type and Compliance by Control tabs as custom rules do not map to controls.
5. Compliance by Resource¶
The Compliance by Resource tab shows the resource evaluation and applied rules for individual resources.
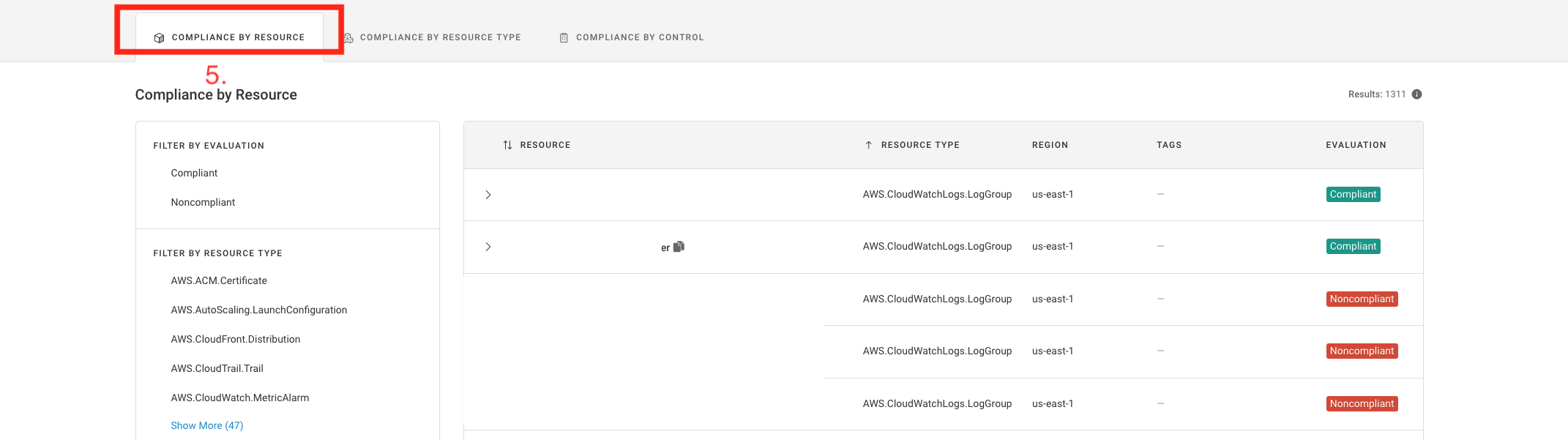
For each resource, the Compliance by Resource tab also shows:
Resource ID, Resource name (Both display for resources where there are distinct names and IDs)
Resource type
Tags
If you select the resource, the details will expand to show the following:
Rules applied to the resource
Controls associated with each rule
Rule severity for each rule
Rule result for each rule:
Passed,Failed, orWaivedButton to Waive each rule, or a
...button to edit or delete an existing waiver
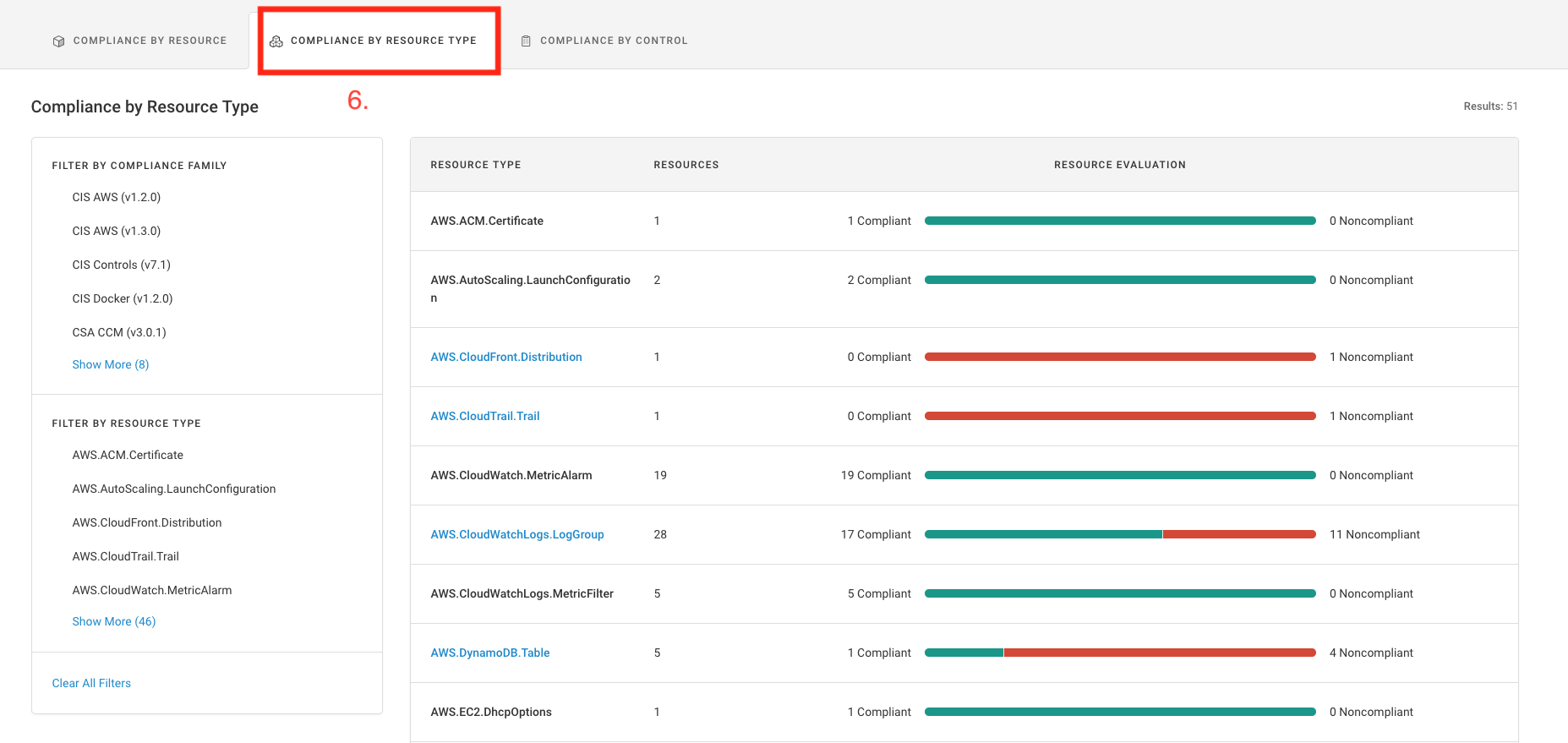
6. Compliance by Resource Type¶
The Compliance by Resource Type tab shows resource evaluations grouped by resource type and shows a ratio of compliant to noncompliant resources.
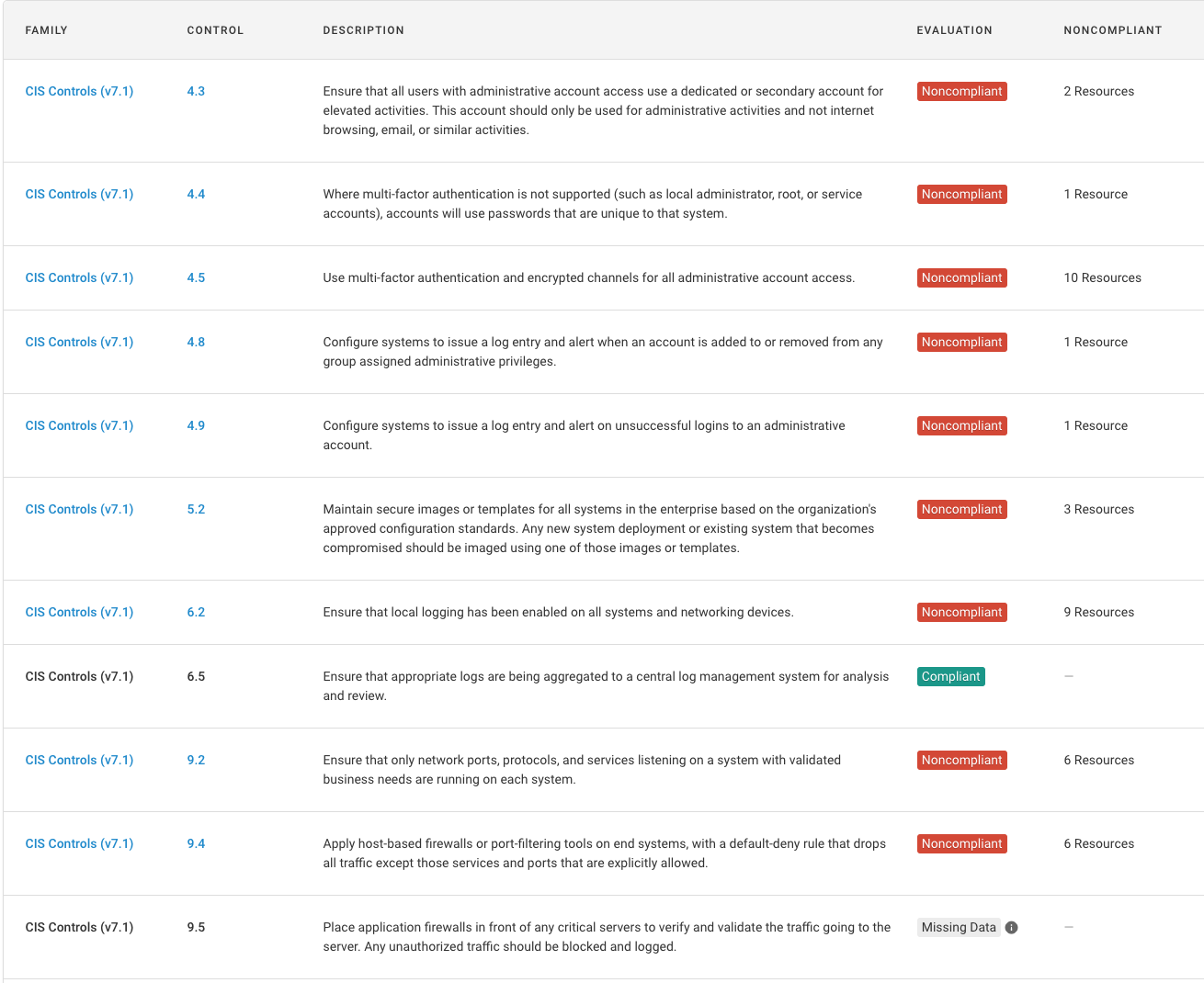
7. Compliance by Control¶
The Compliance by Control tab shows the control evaluation and number of noncompliant resources for each compliance control.
Filtering Results¶
Filtering is available based on the tab selected and varies along with the way the data is organized and displayed:
Compliance by Resource filters
Resource Type
Region
Tag
Evaluation (compliant, noncompliant)
Input Type (repository environments only)
Filepath (repository environments only)
Compliance by Resource Type filters
Compliance family
Resource type
Compliance by Control filters
Compliance family (e.g., CIS Azure Foundations Benchmark, GDPR)
Evaluation (compliant, noncompliant, missing data)
Select the filter toggle to show or hide the filter options.
Sharing Filtered Results¶
Once filters are applied, you can share them via URL. Additionally, filter state is saved as you navigate between the Compliance, Visualizer, Events, Baseline, and Environment Settings pages.
Changing the Number of Rows¶
If there are more than 20 items in the selected tab, you’ll see a dropdown menu below the list. You can choose to show 20, 50, or 100 rows per page:

Further Reading¶
To learn how to view reports and dashboards, and schedule emails containing report content, see Reports & Dashboards.
Note
While Fugue can be viewed as an essential component for maintaining compliance, we cannot provide an explicit guarantee or official certification for any compliance standard(s) or benchmark included in the product. We recommend working with an approved auditor to obtain any official compliance certifications.
