AWS Security Hub Integration¶
Summary¶
AWS Security Hub is an AWS service that helps teams analyze and prioritize security issues from different products and tools more quickly. You can now send Fugue findings to your AWS Security Hub instance. Some use cases include:
Route security events from AWS Security Hub to SIEMs or log management tools.
Streamline audits by layering in evidence from Fugue with other insights from AWS security tools.
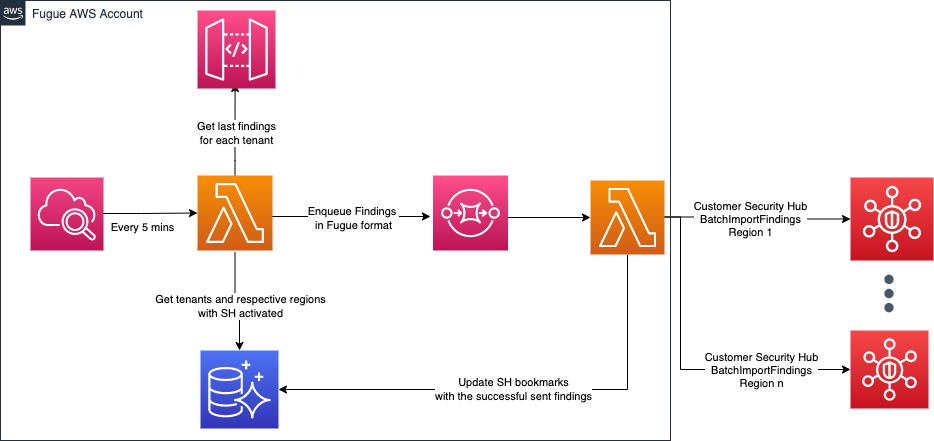
Architecture¶
Fugue is a SaaS application that sends findings from a Fugue AWS account to a customer’s AWS Security Hub regional endpoint. Fugue utilizes an Amazon CloudWatch scheduled event (on a 5 minute interval) to trigger an AWS Lambda function to ingest new Fugue findings from an internal API, and then enqueues Fugue findings to Amazon SQS. Amazon SQS then triggers another AWS Lambda function which translates Fugue findings into the AWS Security Finding Format (ASFF), sends appropriately formatted findings to customer AWS Security Hub regional endpoints, and updates a RDS database with the successful findings.
Integration Steps¶
If your AWS account is managed by AWS Organizations, your administrator may have already configured a Security Hub administrator account and member accounts - which means that Security Hub may already be enabled. You can verify this by navigating to the Security Hub console, and seeing if you can set up Security Hub for a given region.
If you need to set up AWS Security Hub manually, please follow these instructions from AWS. Please make a note of the region(s) that Security Hub is configured in.
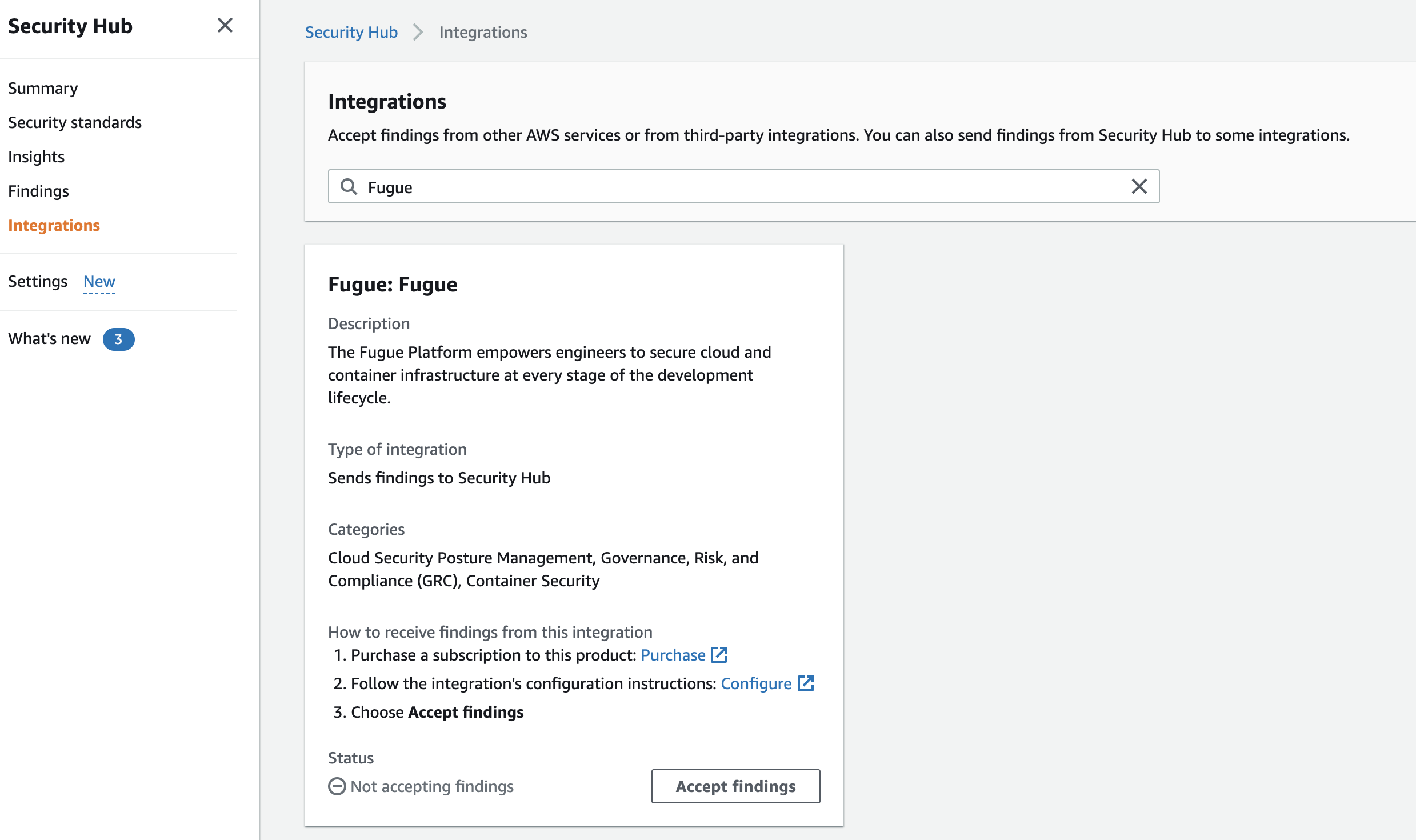
In the AWS console, navigate to the Security Hub service in the correct region, and select Integrations.
Search for Fugue, and select Accept findings.
5. Reach out to Fugue support, and inform the team that you would like Fugue to send findings to your AWS Security Hub instance. Please be prepared to provide Fugue with the following:
Your Tenant ID
The region(s) in which you configured AWS Security Hub
Integration Considerations¶
Fugue batches sending findings to AWS Security Hub in 5 minute intervals, so you should expect some delay between Fugue identifying a potential misconfiguration, and you seeing a finding in Security Hub.
Fugue supports AWS Security Hub in all regions except the following:
ap-northeast-3ap-east-1af-south-1cn-north-1cn-northwest-1
Findings Fields¶
Fugue maps Fugue findings to the following AWS Security Finding Format (ASSF) fields:
AwsAccountId: The AWS Account ID for the resource associated with the findingCompliance/RelatedRequirements: Fugue includes compliance controls associated with the finding, such asCIS-AWS_v1.2_3.1to this fieldCompliance/Status: This value isFAILEDfor all new findingsCreatedAt: The timestamp for when the Fugue finding was createdDescription: A description of the rule that the resource failed, with information on its security relevanceGeneratorId: This maps to Fugue’s rule IDs, such asFG_R00023Id: The Fugue finding IDProductArn: Fugue’s AWS Security Hub product arn:arn:aws:securityhub:<region>::product/fugue/fugueProductFields/ProviderName:Fugueis the value usedRecordState: The Fugue finding status - eitheropenorclosedRemediation: Provides a link to Fugue documentation for a given rule with remediation stepsResources/Id: Includes the resource ARN (or resource ID if ARN is not available) for the resource associated with the findingResources/Type: Provides the AWS format for the resource type, such asAWS::S3::BucketSchemaVersion: Hardcoded to2018-10-08Severity/Label: Maps directly to Fugue findings severity - eitherCRITICAL,HIGH,MEDIUM,LOW, orINFORMATIONALTitle: A short summary of the rule associated with the findingTypes: Hardcoded asSoftware and Configuration ChecksUpdatedAt: The timestamp for when the Fugue finding was most recently updated
