Example: Scan, Detect Drift, Enforce¶
This example shows how Fugue scans the cloud infrastructure in an environment and identifies compliance violations according to the compliance families you choose. You may optionally set a baseline and Fugue will detect when resources drift from that baseline. You can also choose to enable enforcement (AWS & AWS GovCloud), and Fugue will remediate drift, automatically reverting changes and returning infrastructure back to the known-good state of your baseline.
To learn more about the basics of Fugue, we recommend checking out Fugue 101.
Prerequisites¶
An existing Fugue environment (hint – see our AWS & AWS GovCloud or Azure & Azure Government walkthroughs!)
What We’ll Do In This Example¶
Let’s Go!¶
Scan Environment and View Compliance¶
First, navigate to your environment and kick off a new scan. You can do this by selecting the Actions button in the top right of an environment page, then clicking Start New Scan:
You’ll see a banner showing that the scan is in progress. When the banner indicates that the scan has finished, refresh the page, and you’ll see the compliance state of all the scanned resources and whether they passed or failed compliance validation.
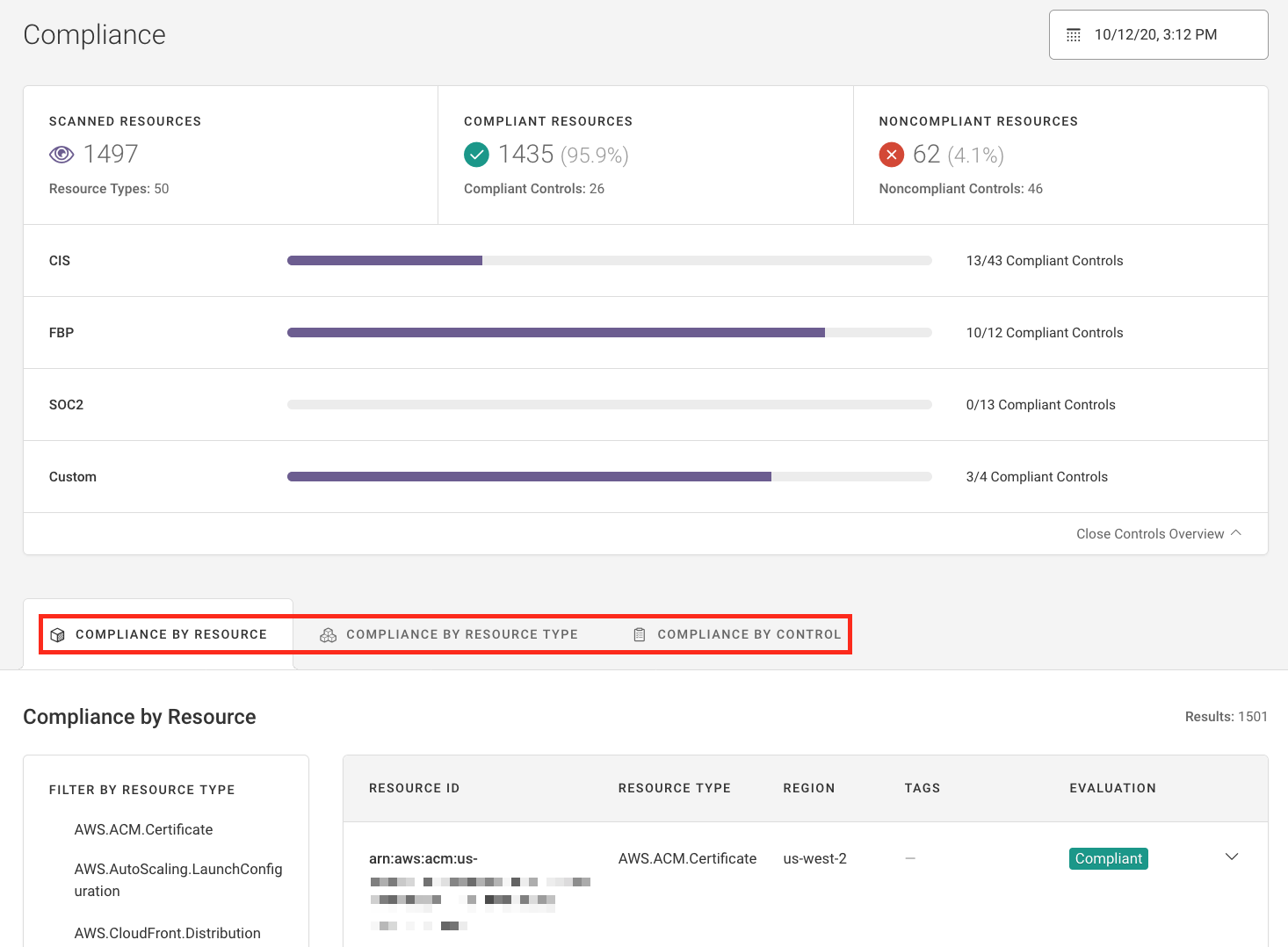
There are three different ways to view compliance state:
Compliance by Resource shows compliance state for individual resources. You might see that security group
sg-07273b045b3123456is noncompliant. If you select its resource ID, you’ll see more detailed information. For example, you might see that the security group failed NIST 800-53 (vRev4) AC-4 because it allows ingress from 0.0.0.0/0 to port 22.Compliance By Resource Type categorizes results by resource types and shows a ratio of compliant to noncompliant resources. You might see that you have 2 compliant Amazon S3 buckets and 4 noncompliant S3 buckets, or 3 compliant Azure virtual networks and 5 noncompliant virtual machines.
Compliance By Control shows the results of the scan organized by compliance control. You might see that CIS AWS (v1.2.0) 1.10, IAM Policy Prevent Password Reuse, failed due to 1 noncompliant resource. Or you might see that your infrastructure is compliant with CIS Azure (v1.1.0) 6.5, Ensure that Network Watcher is “Enabled.”
For more information about each view, see Compliance.
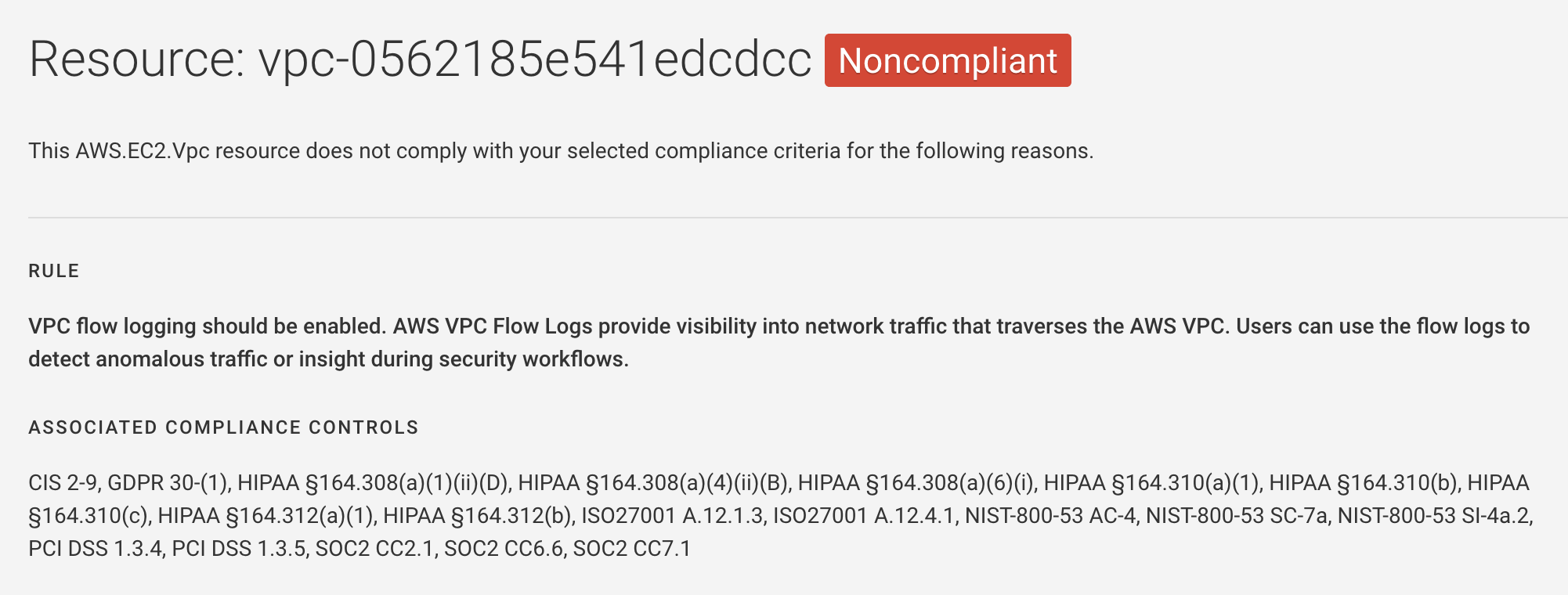
At this point, you can decide whether or not to manually bring any noncompliant resources into compliance. For example, say Fugue indicates that VPC vpc-0562185e541edcdcc violates CIS AWS (v1.2.0) 2.9, which requires that each VPC must have a flow log associated with it. In this case, you can choose to enable a flow log for the VPC in order to set a known-good baseline, or you can leave it disabled.
Likewise, if you have an Azure storage account that has “Secure transfer required” disabled, you can opt to enable it or just leave it as is.
If you only want to view your infrastructure’s compliance state, feel free to stop here. But if you’d like to set a baseline to detect and optionally remediate drift, continue reading – there’s more to see!
Set a Baseline And Detect Drift¶
If you’ve reviewed the compliance status of your infrastructure and have finished making any modifications, you can set the baseline. At the top right of the page, click the Actions button, then select Establish Baseline from the drop-down menu:
You’ll be prompted to confirm your selection. After you select “Yes, Establish Baseline,” Fugue establishes the current snapshot of resource configuration as the source of truth. If a resource is modified or deleted, or if a new resource is created, Fugue will detect it.
To test out Fugue’s drift detection feature, use the AWS Management Console, AWS CLI, Azure Portal (or Azure Government Portal), or Azure CLI to change a resource in the baseline. Let’s start by modifying something small. You can decide what to do based on the infrastructure you have, but here are some ideas:
Change the port range in an AWS or Azure security group ingress rule
Change the public access level for Azure blob containers
Change a statement in an AWS Identity & Access Management (IAM) policy
After you’ve modified the resource, Fugue will detect the change during its next scan. If you don’t want to wait, you can manually trigger a scan.
Once the next scan is completed, results appear on the Events page, which lists each drift or enforcement event. You’ll see the following data:
Resource ID: The AWS ID of a resource that changed. Example:
vpc-0439fb61Resource type: The type of resource that changed. Example:
Azure.Storage.AccountChange: The type of drift. Either
Added,Removed, orModifiedEvent type: The type of event. Either
DriftorRemediationResult: Whether or not a resource was enforced. Either
Revertedor blankDetected date: When the drift was detected. Example:
7/13/19, 7:39 PM
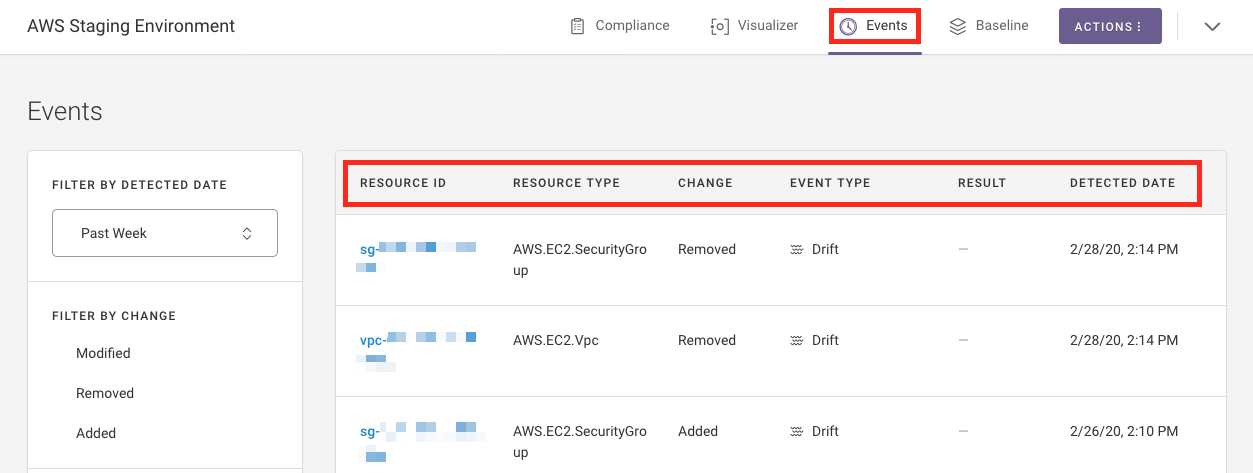
Above, you can see several drift events. Each item above represents a resource addition, deletion, or modification.
Now that you’ve seen Fugue’s drift report, you can stop here if you’re content with reviewing it and manually determining whether to revert resources. But if you’d like to explore Fugue’s baseline enforcement feature, keep reading!
Enable Baseline Enforcement (AWS & AWS GovCloud)¶
To enable baseline enforcement (AWS & AWS GovCloud), select the Actions button at the top right of the page and find the ![]() Edit Environment option in the drop-down menu. This is where you can change your environment name, update your IAM role ARN or Azure credentials, select different compliance standards, and enable/disable enforcement.
Edit Environment option in the drop-down menu. This is where you can change your environment name, update your IAM role ARN or Azure credentials, select different compliance standards, and enable/disable enforcement.
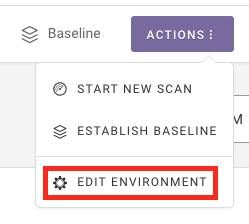
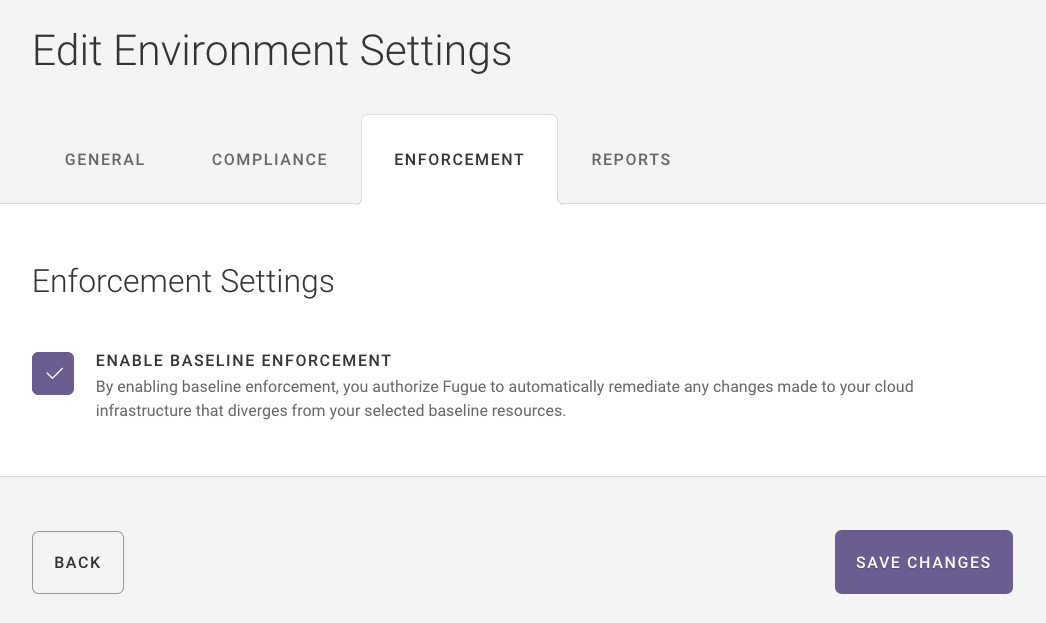
In the dialog that pops up, select the Enforcement tab and check the box next to Enable Baseline Enforcement. Note that by doing so, you authorize Fugue to automatically remediate any changes made to your cloud infrastructure that diverges from your selected baseline resources.
Now that we’ve turned on baseline enforcement, let’s make a small modification for Fugue to revert.
Change the name of an Amazon VPC
Change the protocol of a security group egress rule
Change a tag on a resource
After you’ve modified the resource, Fugue will detect the change and remediate it during its next scan.
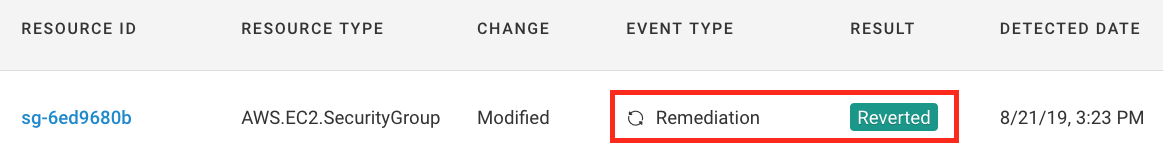
Once the next scan has completed, results again appear on the Events page. This time, however, you should see that the resource you changed has been changed back – it now has an event type of Remediation and a result of Reverted. You can verify the changes by checking the AWS Management Console. You’ll see that Fugue has returned your infrastructure to the known-good state of your baseline, and you didn’t have to lift a finger!
What’s Next?¶
Next, you can set up notifications to be alerted whenever Fugue detects a compliance, drift, or remediation event. Or, learn more about visualizing your cloud infrastructure. Want to dive into another example? Check out how to integrate Fugue with Slack.
Note
While Fugue can be viewed as an essential component for maintaining your infrastructure compliance, we cannot provide an explicit guarantee or official certification for any compliance standard(s) or benchmark included in the product. We recommend working with an approved auditor to obtain any official compliance certifications.
