How To: Create a Fugue IAM Role¶
This quick tutorial shows how to create the AWS Identity & Access Management (IAM) role for Fugue to scan an AWS or AWS GovCloud environment. You create the role by launching a CloudFormation stack in your account.
Note
See a list of all possible IAM permissions here.
You may alternatively create the role via the AWS CLI.
What’s Going to Happen?¶
When you launch a stack to create an IAM role in your account, Fugue creates the role with permissions according to the resource types you selected. It assigns two policies:
The AWS-managed SecurityAudit read-only policy
If needed, a supplemental inline policy granting any required read permissions not covered by
SecurityAudit
If you’d like to see the permissions tailored to your selected resource types, follow the instructions here. For a list of all possible permissions Fugue might need, see IAM Policy Permissions.
Note that the role also has a trust policy that specifies an external ID. Fugue generates this unique ID for your tenant to prevent other parties from assuming the role without the ID, even if they have your role ARN.
Let’s Go!¶
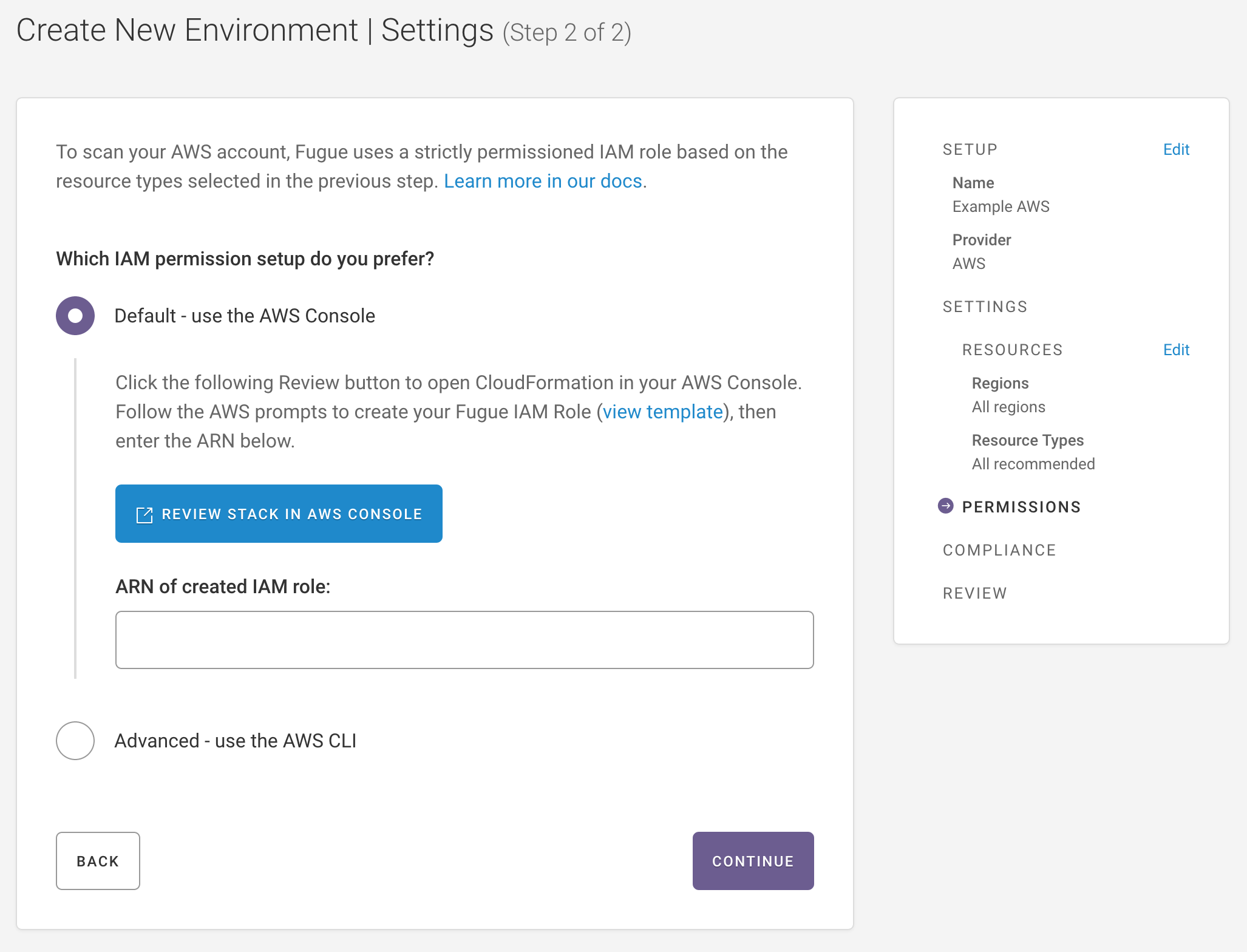
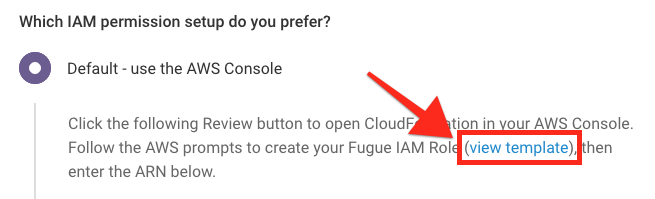
After you’ve named your environment and selected your resources in the Create New Environment workflow, you’ll arrive at the permissions page:
Launch CloudFormation Stack¶
Select Review Stack in AWS Console.
Select Next on the next three pages, keeping defaults.
Check the box to acknowledge that CloudFormation may create IAM resources with custom names.
Select Create Stack.
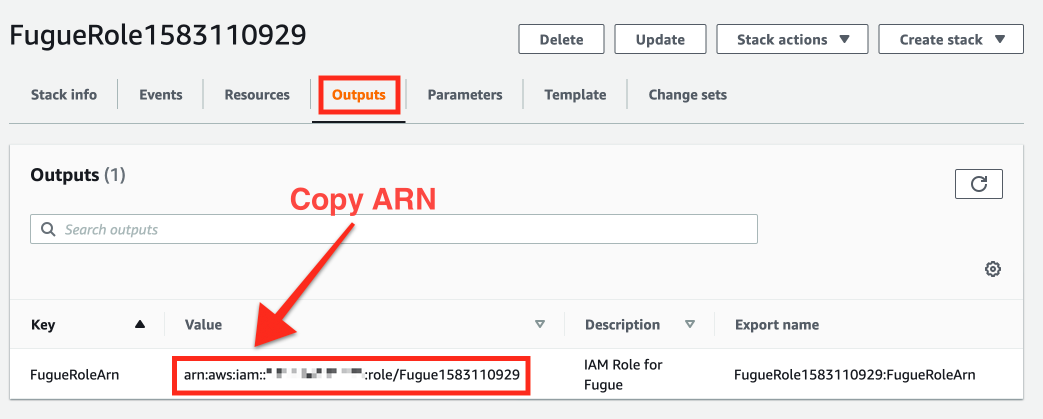
On the created stack page, select the Outputs tab.
Copy the IAM role ARN from the Value column after it appears (this may take a few seconds and require refreshing).
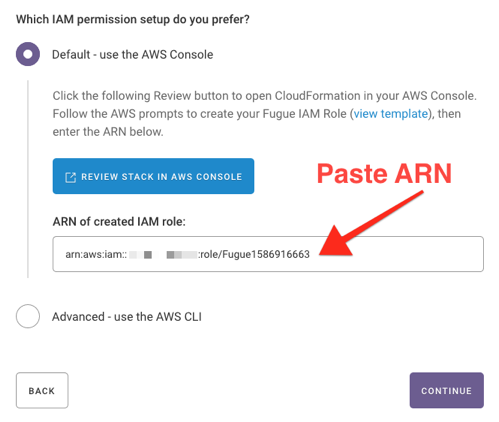
Paste the IAM role ARN in the AWS IAM Role ARN field in Fugue.
That’s it – you’re done! You just created an IAM role for Fugue.
How do I see the role permissions before creating the role?¶
You can inspect the exact permissions Fugue will grant the role by viewing the CloudFormation stack template. To do so, click the view template link in the Create New Environment workflow:
You’ll see a modal containing the CloudFormation template Fugue generated for you based on the resource types you selected for scanning. The template includes the AWS-managed read-only SecurityAudit policy and a tightly-scoped supplemental policy to cover any additional permissions.
See the list of SecurityAudit permissions here. For a list of all possible permissions, see IAM Policy Permissions.
What’s Next?¶
Check out Setup - AWS & AWS GovCloud to continue getting started with Fugue. You can also jump ahead to one of our other examples.
Or, if you’d prefer, learn how to:
